Headline news yesterday (20th Dec 2016) report Ukraine Suffers Power Outage. It was the 2nd time of power disruption this year. As far as I remember the 1st incident occurred on Jan 2016. The motivation of this news lets information security experts re-think about BlackEnergy DDos tools.The Blackenergy soft tools found 2007, a notorious powerful distributed denial of services soft tool conducted cyber attacks suspended Georgian Soviet Socialist Republic communication facilities. Sum up the cyber attack in nuclear power facilities, it gives people to feel those incidents looks like a political fights. Sounds like naughty boy intend to turn off neighbor main water tap to create troubles.
Analyze of nuclear power facility of attacks
Hardcore type malware: Stuxnet, Duqu, and Flame are categories hardcore type malware. The hardcore type malware usually achieve the following actions.
Incident historical records:
- June 2010 – Stuxnet malware to sabotage Iran’s nuclear program.
- May 2012 – Flame malware targeted cyber espionage in Middle Eastern countries.
- Dec 2014 – South Korean nuclear operator hacked amid cyber-attack fears.
- Mar 2015 – South Korea claims North hacked nuclear data.
- Apr 2016 – A malware infected systems at the Gundremmingen nuclear plant in Germany.
- Oct 2016 – Headline News: Rep. Kim Jin-pyo, a lawmaker of the main opposition Minjoo Party of Korea, told Yonhap News Agency in a telephone interview that the hacking targeted the “vaccine routing server” installed at the cyber command.
Weaponize types of malware: contains sabotage, interfere, traffic monitoring function and remote control functions.
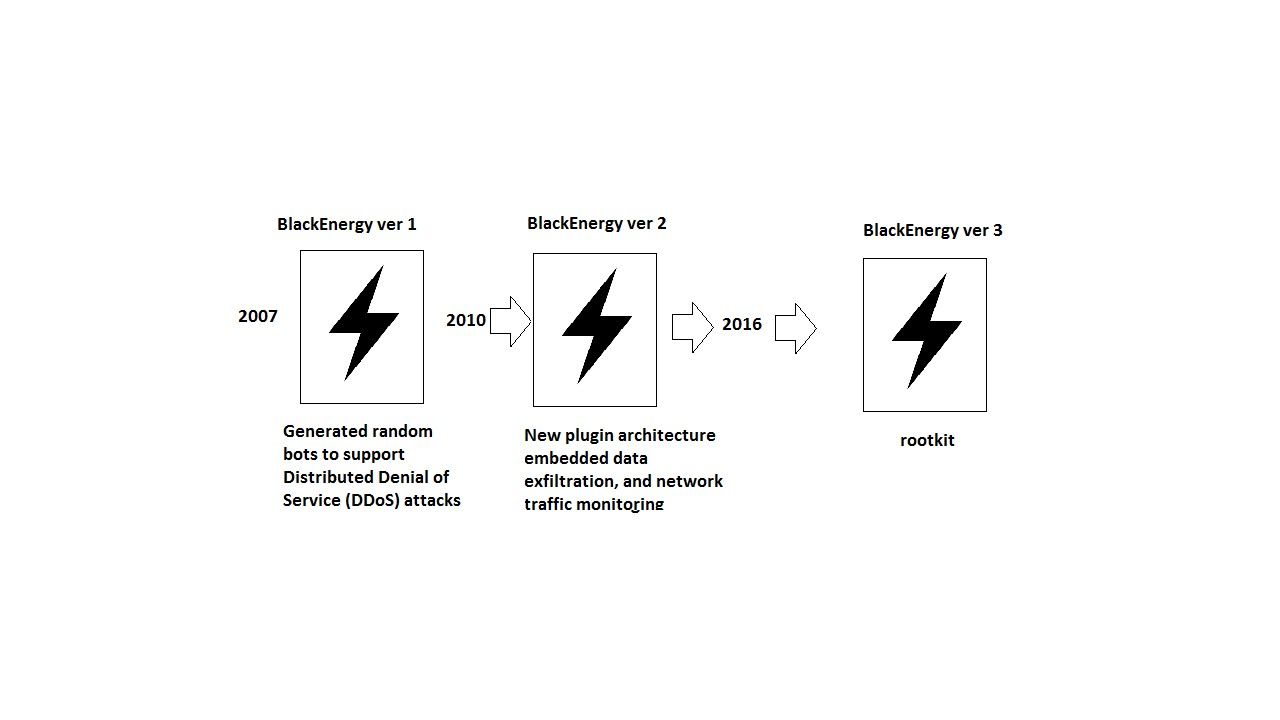
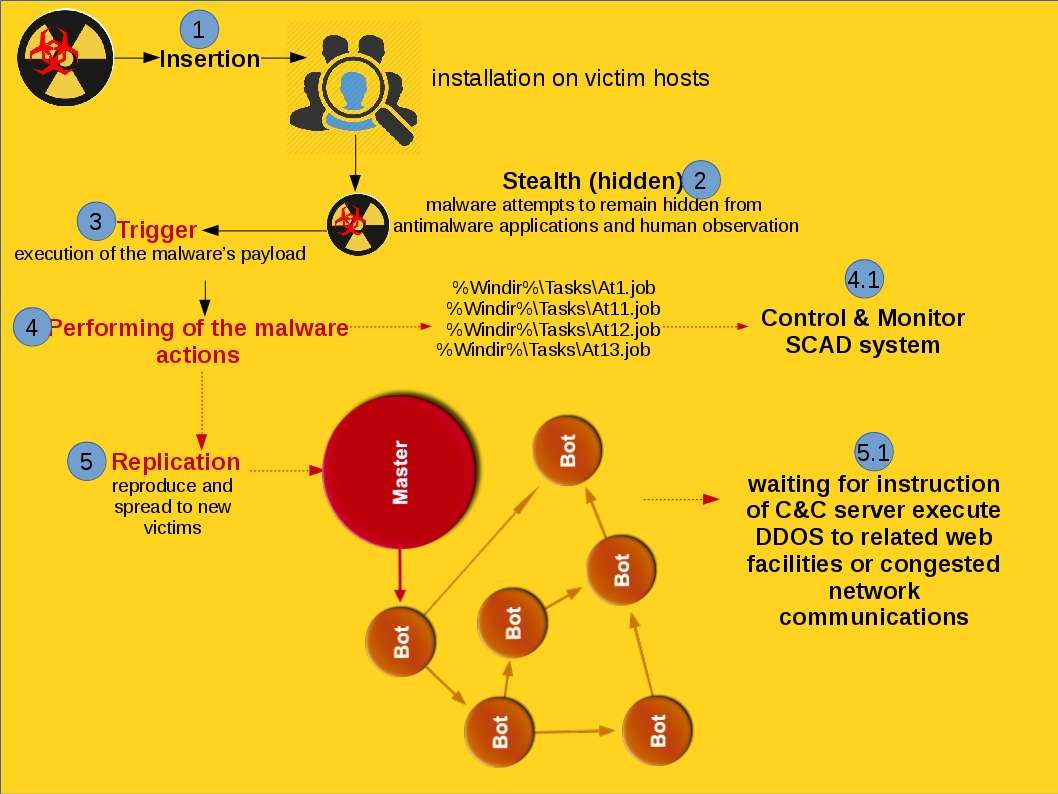
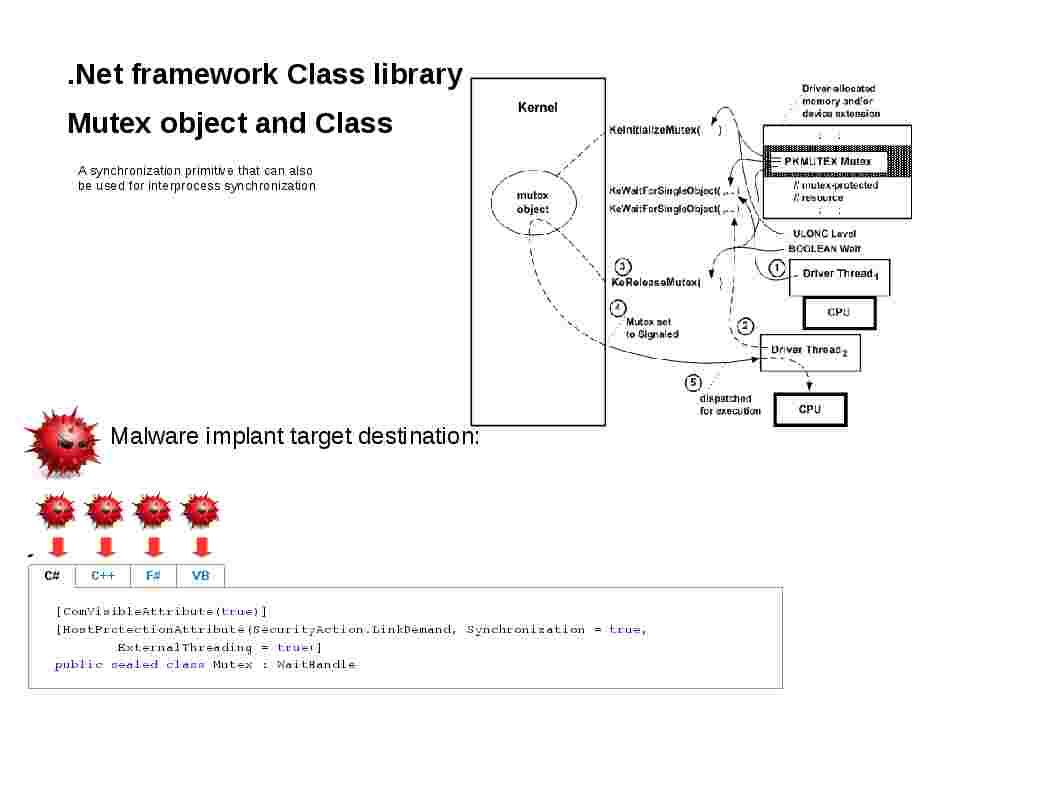
The original goal of design for BlackEnergy is provides powerful distributed denial of service function. To meet attacker functional requirement, BlackEnergy began supporting plugins in 2007. This is the second generation of BlackEnergy. The malware plugin feature make use of mutex objects to avoid infecting the system more than once, as well as to coordinate communications among its multiple components on the host (see below diagram for reference). To evade virus and malware detection, malware avoids using a hardcoded name for its mutex.
The third generation of BlackEnergy take advantage of OLE object (CVE-2014-6352). Embedded mailicous code to MS office xls format of document gained remote code execution. Since the blackenergy hash exposed to the world (see below details for reference). More than 90% of above antivirus program can detected. It looks that the severity level of risk dropped.
SHA256: f5785842682bc49a69b2cbc3fded56b8b4a73c8fd93e35860ecd1b9a88b9d3d8
Target windows component: Win32 DLL
Attack scenario: PE32 executable for MS Windows (DLL) (GUI) Intel 80386 32-bit
Malware implant target destination:
- Win32 Executable MS Visual C++ (generic) (67.4%)
- Win32 Dynamic Link Library (generic) (14.2%)
- Win32 Executable (generic) (9.7%)
- Generic Win/DOS Executable (4.3%)
- DOS Executable Generic (4.3%)
Status update on 21st Dec 2016
Ukraine Suffers Power Outage Possibly Due to Energy Plant Hack on 17th Dec 2016 Sat. What do you think? Do you think a new shape of blackenergy was born? My speculation is that the cyber attacks in nuclear power facilities will going to increase coming months.
For reference:
Some genuinely prize content on this website , bookmarked .
Thank you for all of the work on this web site. Debby enjoys making time for investigation and it’s really obvious why. My spouse and i notice all relating to the dynamic ways you provide very helpful techniques on your web blog and even invigorate response from some other people on the issue and my princess is discovering a lot. Have fun with the remaining portion of the new year. Your carrying out a great job.
wonderful issues altogether, you just received a new reader. What could you recommend in regards to your publish that you just made some days ago? Any certain?
Hello my family member! I wish to say that this article is amazing, nice written and come with approximately all significant infos. I would like to look more posts like this .
I really like your writing style, great information, appreciate it for posting : D.
Wow, fantastic blog structure! How long have you ever been blogging for? you made blogging look easy. The whole glance of your web site is wonderful, let alone the content material!
I have been absent for a while, but now I remember why I used to love this blog. Thank you, I will try and check back more often. How frequently you update your web site?
It is really a nice and useful piece of information. I am happy that you shared this useful info with us. Please keep us up to date like this. Thank you for sharing.
I’ll right away grasp your rss feed as I can not to find your email subscription link or newsletter service. Do you’ve any? Kindly allow me understand so that I may just subscribe. Thanks.
I definitely wanted to make a simple remark so as to thank you for those marvelous suggestions you are giving at this site. My extensive internet lookup has now been recognized with wonderful concept to write about with my best friends. I would declare that most of us website visitors actually are extremely fortunate to exist in a magnificent website with many lovely people with useful plans. I feel truly privileged to have come across your entire web page and look forward to many more fabulous minutes reading here. Thanks a lot once more for a lot of things.
I not to mention my guys came digesting the good techniques on your site then immediately came up with an awful suspicion I never thanked the blog owner for those techniques. Most of the ladies had been as a result glad to read through all of them and already have without a doubt been enjoying those things. Thank you for actually being so thoughtful and also for selecting this kind of tremendous topics millions of individuals are really eager to understand about. Our honest apologies for not saying thanks to sooner.
Just wanna tell that this is handy , Thanks for taking your time to write this.
Wow, awesome blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your website is magnificent, as well as the content!
Your self should toward be a component of a contest for one particular of the utmost good quality web sites upon the world-wide-web. I’m transferring in the direction of advocate this blog site!
I conceive you have mentioned some very interesting points , regards for the post.
I got what you mean , thanks for posting .Woh I am happy to find this website through google. “Money is the most egalitarian force in society. It confers power on whoever holds it.” by Roger Starr.
I’ve learn several excellent stuff here. Definitely value bookmarking for revisiting. I wonder how much attempt you set to make such a excellent informative web site.
Enjoyed looking through this, very good stuff, appreciate it. “Nothing happens to any thing which that thing is not made by nature to bear.” by Marcus Aurelius Antoninus.
Simply wanna input that you have a very nice website , I enjoy the style it actually stands out.
Normally I don’t learn post on blogs, however I would like to say that this write-up very forced me to try and do it! Your writing style has been amazed me. Thank you, quite great post.
My brother recommended I might like this website. He was entirely right. This post actually made my day. You cann’t imagine just how much time I had spent for this information! Thanks!
I have been surfing online more than 3 hours as of late, yet I never discovered any interesting article like yours. It is lovely worth sufficient for me. In my view, if all website owners and bloggers made just right content as you probably did, the web might be much more useful than ever before.
Pretty section of content. I just stumbled upon your blog and in accession capital to assert that I get actually enjoyed account your blog posts. Any way I’ll be subscribing to your augment and even I achievement you access consistently fast.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such great info being shared freely out there.
Thanks, I’ve recently been searching for info approximately this topic for a long time and yours is the greatest I’ve discovered so far. But, what in regards to the conclusion? Are you sure about the supply?
Hi there! This is kind of off topic but I need some advice from an established blog. Is it very difficult to set up your own blog? I’m not very techincal but I can figure things out pretty quick. I’m thinking about setting up my own but I’m not sure where to begin. Do you have any tips or suggestions? Cheers
I would like to thank you for the efforts you’ve put in writing this website. I’m hoping the same high-grade blog post from you in the upcoming also. In fact your creative writing abilities has inspired me to get my own web site now. Really the blogging is spreading its wings rapidly. Your write up is a great example of it.
I delight in, lead to I discovered just what I was looking for. You have ended my 4 day long hunt! God Bless you man. Have a great day. Bye
Whats up very cool web site!! Man .. Excellent .. Superb .. I will bookmark your site and take the feeds also…I am glad to seek out so many helpful information right here in the post, we’d like develop extra strategies in this regard, thank you for sharing.
Once I initially commented I clicked the -Notify me when new comments are added- checkbox and now every time a remark is added I get four emails with the identical comment. Is there any means you’ll be able to take away me from that service? Thanks!
Keep functioning ,impressive job!
I have been browsing online greater than three hours as of late, yet I never discovered any attention-grabbing article like yours. It is pretty price sufficient for me. Personally, if all website owners and bloggers made just right content as you did, the internet can be a lot more useful than ever before.
Appreciate you for sharing these kind of wonderful blogposts. In addition, the optimal travel along with medical insurance approach can often reduce those concerns that come with traveling abroad. Some sort of medical crisis can before long become very costly and that’s absolute to quickly place a financial weight on the family finances. Setting up in place the excellent travel insurance program prior to leaving is well worth the time and effort. Thank you
I do believe all of the ideas you’ve introduced to your post. They are very convincing and can certainly work. Nonetheless, the posts are very quick for newbies. Could you please prolong them a little from subsequent time? Thanks for the post.
I have read a few excellent stuff here. Definitely worth bookmarking for revisiting. I surprise how a lot attempt you set to make this kind of wonderful informative site.
This is one awesome post.Really thank you! Will read on…
You made some decent points there. I looked on the internet for the subject matter and found most persons will go along with with your site.
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish only about gossips and internet and this is really frustrating. A good blog with interesting content, that is what I need. Thanks for keeping this web-site, I’ll be visiting it. Do you do newsletters? Can not find it.
Thanks a lot for sharing this with all people you actually realize what you’re speaking about! Bookmarked. Kindly additionally consult with my site =). We will have a link trade agreement between us!
Hello, there. I know this is off-topic, but I was wondering which blog platform are you using for this site? I’m getting fed up of WordPress because I’ve had problems with hackers and I’m looking at options for another platform. I would be fantastic if you could point me in the direction of a good platform
It is perfect time to make some plans for the future and it is time to be happy. I have read this post and if I could I want to suggest you some interesting things or suggestions. Maybe you can write next articles referring to this article. I desire to read more things about it!
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thank you again
Of course, what a fantastic blog and informative posts, I definitely will bookmark your blog.Best Regards!
Good write-up, I¡¦m regular visitor of one¡¦s site, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
Wow! Thank you! I permanently needed to write on my site something like that. Can I include a fragment of your post to my site?
Hey, you used to write magnificent, but the last few posts have been kinda boring¡K I miss your great writings. Past several posts are just a little out of track! come on!
Excellent beat ! I wish to apprentice while you amend your site, how could i subscribe for a blog web site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast offered bright clear concept
I’m still learning from you, while I’m making my way to the top as well. I certainly liked reading all that is posted on your website.Keep the tips coming. I loved it!
Generally I do not read post on blogs, however I wish to say that this write-up very compelled me to take a look at and do so! Your writing style has been amazed me. Thanks, quite nice post.
It¡¦s really a cool and useful piece of information. I am satisfied that you simply shared this helpful information with us. Please stay us up to date like this. Thanks for sharing.
Great write-up, I am regular visitor of one¡¦s website, maintain up the nice operate, and It’s going to be a regular visitor for a long time.
It¡¦s really a cool and useful piece of info. I¡¦m satisfied that you shared this useful info with us. Please keep us informed like this. Thanks for sharing.
Woah! I’m enjoying the template/theme of this website. It’s simple, yet effective. A lot of times it’s very hard to get that “perfect balance” between superb usability and visual appeal. I must say you’ve done a very good job with this.
I needed to send you that tiny remark to be able to thank you so much once again considering the awesome tricks you have featured on this site. This has been simply wonderfully open-handed with people like you giving unreservedly exactly what many individuals would have offered for sale as an electronic book to get some dough on their own, specifically considering that you could possibly have tried it if you considered necessary. Those inspiring ideas also worked as the fantastic way to be certain that many people have the same desire the same as my personal own to realize lots more concerning this condition. I am certain there are numerous more pleasant times ahead for people who find out your blog post.
Your new valuable key points imply much a person like me and extremely more to my office workers. With thanks; from everyone of us.
419807 72963Very nice design and style and fantastic subject matter, very little else we want : D. 642482
Its not my first time to visit this web page, i am visiting this site dailly and take goodinformation from here everyday.
Hello! This is kind of off topic but I need some advice from an established blog. Is it very difficult to set up your own blog? I’m not very techincal but I can figure things out pretty quick. I’m thinking about creating my own but I’m not sure where to start. Do you have any ideas or suggestions? Cheers
Highly entertaining resources you have stated, a big heads up for setting up.
I don’t even know how I ended up here, but I thought this post was wonderful. I do not know who you might be but definitely you’re going to a famous blogger should you are not already Cheers! xrumer
I believe you have mentioned some very interesting details , thankyou for the post.
You have observed very interesting details ! ps decent web site . “Great opportunities to help others seldom come, but small ones surround us every day.” by Sally Koch.
Love to read it,Waiting For More new Update and I Already Read your Recent Post its Great Thanks.
Greetings from IdahoCarolinaOhioColoradoFloridaLos angelesCalifornia! I’m bored to tearsbored to deathbored at work so I decided to check outbrowse your sitewebsiteblog on my iphone during lunch break. I enjoyreally likelove the knowledgeinfoinformation you presentprovide here and can’t wait to take a look when I get home. I’m shockedamazedsurprised at how quickfast your blog loaded on my mobilecell phonephone .. I’m not even using WIFI, just 3G .. AnyhowAnyways, awesomeamazingvery goodsuperbgoodwonderfulfantasticexcellentgreat siteblog!
I’m not that much of a onlineinternet reader to be honest but your blogssites really nice, keep it up! I’ll go ahead and bookmark your sitewebsite to come back laterdown the roadin the futurelater on. CheersAll the bestMany thanks
This is veryreally interesting, You areYou’re a very skilled blogger. I haveI’ve joined your feedrss feed and look forward to seeking more of your greatwonderfulfantasticmagnificentexcellent post. Also, I haveI’ve shared your siteweb sitewebsite in my social networks!
I really can’t believe how great this site is. Keep up the good work. I’m going to tell all my friends about this place.
Nice post. Thank you!
I’ve been absent for a while, but now I remember why I used to love this web site. Thank you, I¡¦ll try and check back more often. How frequently you update your website?
Thank you for a marvelous posting! I enjoyed reading it you’re a fantastic author.I will make sure that you bookmark your site and may come back someday. I would like to encourage that you continue your great articles, have a wonderful weekend!