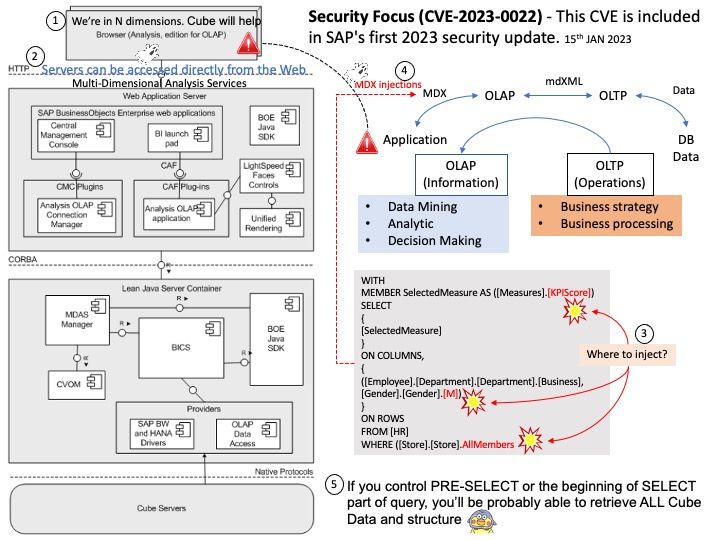
Preface: OLAP is all about BI and Big Data. Online analytical processing (OLAP) is an approach to formulate and answer multidimensional queries to large datasets.
Background: SAP have released a new statement of direction for SAP BusinessObjectsthat introduces a new version of the SAP BusinessObjects BI suite code named SAP BusinessObjects BI 2024, available on-premises and through managed cloud. SAP will provide clear use case migration paths for the components that they plan to end support of after 2027.
https://www.sap.com/documents/2020/03/908ee705-8a7d-0010-87a3-c30de2ffd8ff.html
Vulnerability details: A code injection flaw in the BusinessObjects Business Intelligence platform (CVSS score of 9.9).
SAP BusinessObjects Business Intelligence Analysis edition for OLAP allows an authenticated attacker to inject malicious code that can be executed by the application over the network. On successful exploitation, an attacker can perform operations that may completely compromise the application causing a high impact on the confidentiality, integrity, and availability of the application.
What was that happen? In what way Does customer will trigger this vulnerability? As usual, vendor did not disclosed the details. But in case of similar design. Attacker will do the attack in this way. For details, please refer to diagram for reference.
Official Announcement: Please see the link for details of this official announcement
https://www.sap.com/documents/2022/02/fa865ea4-167e-0010-bca6-c68f7e60039b.html
Affected Products: SAP BusinessObjects Business Intelligence platform (Analysis edition for OLAP), Versions – 420, 430

-10thJan2023.jpg)