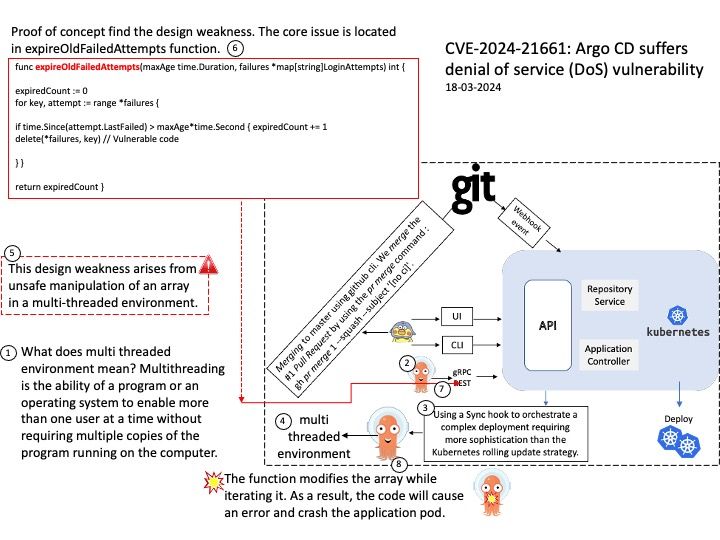
Preface: What does multi threaded environment mean? Multithreading is the ability of a program or an operating system to enable more than one user at a time without requiring multiple copies of the program running on the computer.
Background: Argo CD is implemented as a Kubernetes controller which continuously monitors running applications and compares the current, live state against the desired target state (as specified in the Git repo). Hooks are simply Kubernetes manifests tracked in the source repository of your Argo CD Application. Synchronization can be configured using resource hooks. Hooks are ways to run scripts before, during, and after a Sync operation. Hooks can also be run if a Sync operation fails at any point. For example:
Using a Sync hook to orchestrate a complex deployment requiring more sophistication than the Kubernetes rolling update strategy.
Vulnerability details: An attacker can exploit a critical flaw in the application to initiate a Denial of Service (DoS) attack, rendering the application inoperable and affecting all users. The issue arises from unsafe manipulation of an array in a multi-threaded environment.
Official announcement: Please see the link below for details – https://nvd.nist.gov/vuln/detail/CVE-2024-21661