Preface: Upgrade from Xamarin to [.]NET, Microsoft support for Xamarin will end on May 1, 2024 for all Xamarin SDKs including Xamarin.Forms.
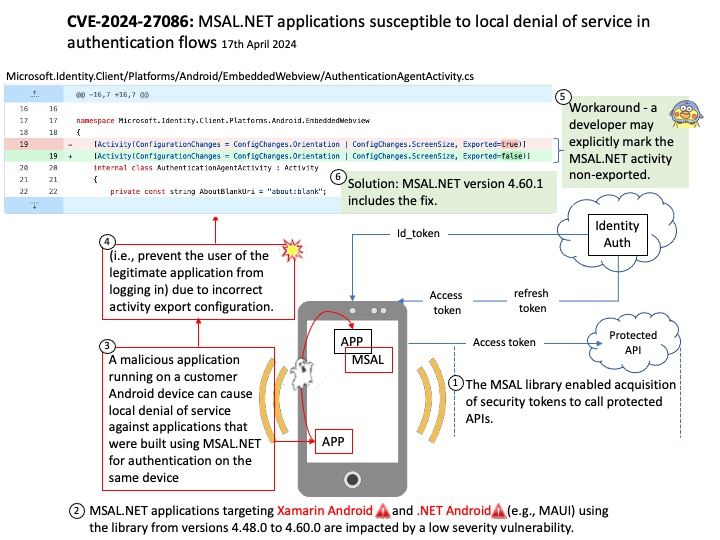
Background: The Microsoft Authentication Library (MSAL) enables developers to acquire security tokens from the Microsoft identity platform to authenticate users and access secured web APIs. It can be used to provide secure access to Microsoft Graph, other Microsoft APIs, third-party web APIs, or your own web API.
-Xamarin is an open-source platform for building modern and performant applications for iOS, Android, and Windows with [.] NET. Xamarin is an abstraction layer that manages communication of shared code with underlying platform code.
-NET Multi-platform App UI (. NET MAUI) apps can be written for the following platforms: Android 5.0 (API 21) or higher is required. iOS 11 or higher is required.
Vulnerability details: The MSAL library enabled acquisition of security tokens to call protected APIs. MSAL[.}NET applications targeting Xamarin Android and [.]NET Android (e.g., MAUI) using the library from versions 4.48.0 to 4.60.0 are impacted by a low severity vulnerability. A malicious application running on a customer Android device can cause local denial of service against applications that were built using MSAL[.]NET for authentication on the same device (i.e., prevent the user of the legitimate application from logging in) due to incorrect activity export configuration.
Solution: MSAL[.]NET version 4.60.1 includes the fix.
Workaround: developer may explicitly mark the MSAL[.]NET activity non-exported.
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2024-27086