Official Published: 10/06/2025
Preface: Microsoft partners with the Android ecosystem by enabling its PlayReady DRM technology for content protection on Android devices, both in apps and web browsers. This integration allows developers to protect premium content like live TV and video-on-demand (VOD) using Android’s Java DrmManagerClient API, while web browsers use the Encrypted Media Extensions (EME) standard to access PlayReady via a Content Decryption Module (CDM). Leading Android device manufacturers often embed a PlayReady client into their devices, and Microsoft provides a Porting Kit to help them do so.
Background: The core of the Android OS operating system is the Android Open Source Project (AOSP), which is free open source software (FOSS) licensed primarily under the Apache License. However, most devices run a proprietary version of Android developed by Google, which comes pre-installed with additional proprietary, closed-source software, most popular Google Mobile Services (GMS), which includes core applications such as Google Chrome, the digital distribution platform Google Play, and the related Google Play Services development platform.
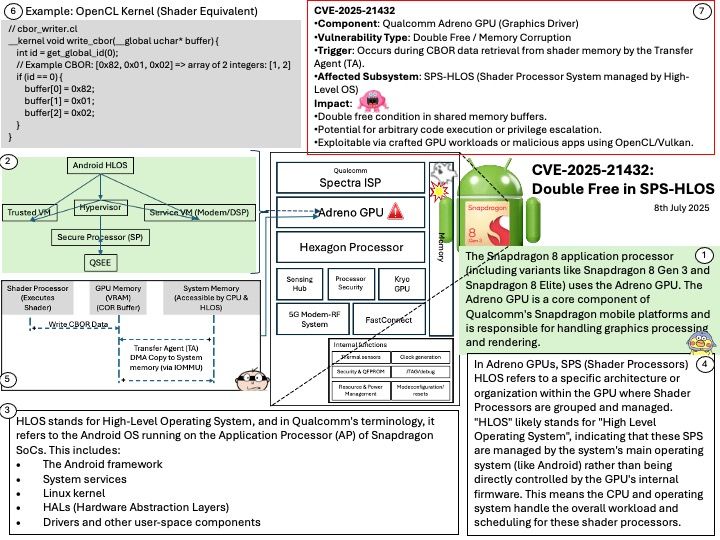
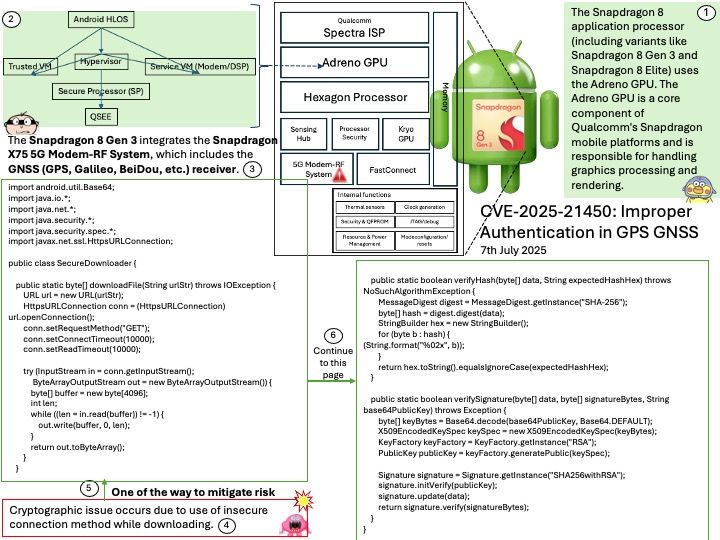
Qualcomm Android source code is divided into development source code and proprietary source code. Proprietary source code is further divided into proprietary non-HLOS software and proprietary HLOS software. HLOS is the High-level Operating System, and non-HLOS software refers to software below the HLOS layer.
Vulnerability details: Memory corruption during PlayReady APP use case while processing TA commands.
CVE-2025-27053 : If the BUFFER_SIZE is incorrectly calculated (e.g., too small for the actual data exchanged), the TA might read or write beyond the allocated memory, leading to memory corruption. The vulnerability CVE-2025-27053 is a memory corruption issue caused by incorrect buffer size calculation in HLOS when processing TA commands in the PlayReady APP usecase. Here’s why it affects Qualcomm Snapdragon chips.
Official announcement: Please refer to the url for details –
https://docs.qualcomm.com/product/publicresources/securitybulletin/october-2025-bulletin.html