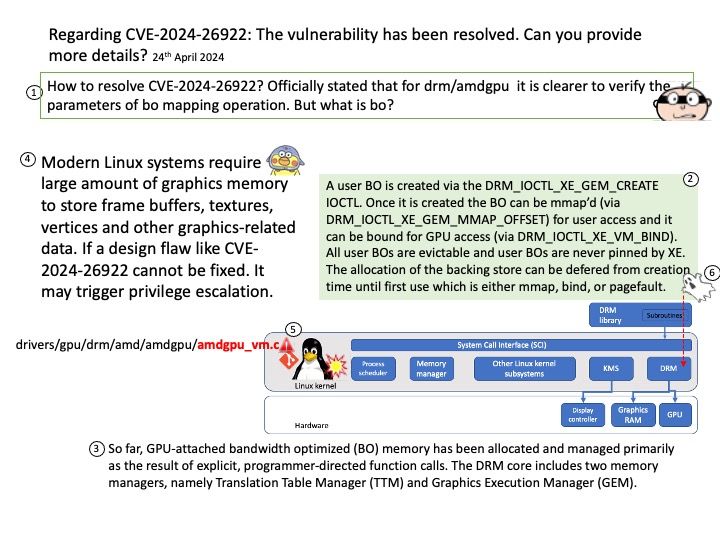
Preface: Modern Linux systems require large amount of graphics memory to store frame buffers, textures, vertices and other graphics-related data. If a design flaw like CVE-2024-26922 cannot be fixed. It may trigger privilege escalation.
Background: So far, GPU-attached bandwidth optimized (BO) memory has been allocated and managed primarily as the result of explicit, programmer-directed function calls. The DRM core includes two memory managers, namely Translation Table Manager (TTM) and Graphics Execution Manager (GEM).
Vulnerability details: In the Linux kernel, the following vulnerability has been resolved: drm/amdgpu: validate the parameters of bo mapping operations more clearly Verify the parameters of amdgpu_vm_bo_(map/replace_map/clearing_mappings) in one common place.
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2024-26922