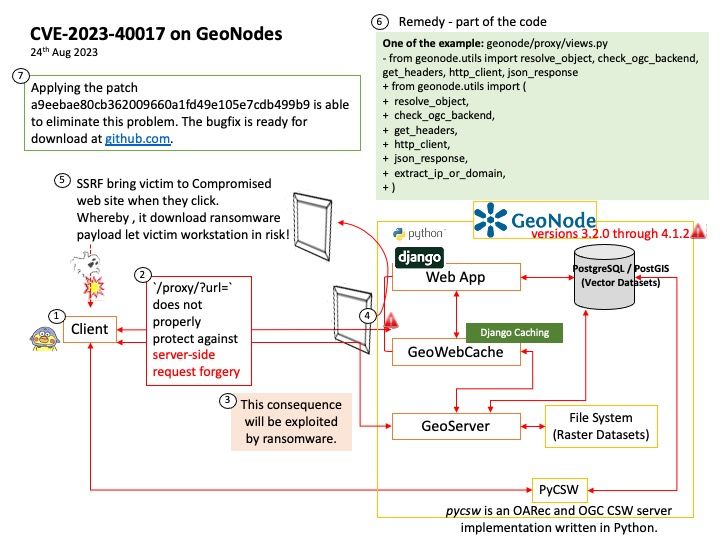
Preface: Server Side Request forgery (SSRF) in few years ago not bring IT admin attention. But when ransomware was born, SSRF vulnerability make worries because it can exploit by cyber criminals. So we should be careful when we know our web server apps contains SSRF vulnerability.
Background: GeoNode is a geospatial content management system, a platform for the management and publication of geospatial data. It brings together mature and stable open-source software projects under a consistent and easy-to-use interface allowing non-specialized users to share data and create interactive maps.
For reference:
- Django is a high-level Python web framework
- PostgreSQL / PostGIS (Vector Datasets)
- pyCSW – pycsw is an OARec and OGC CSW server implementation written in Python.
- Raster Datasets – Raster datasets represent geographic features by dividing the world into discrete square or rectangular cells laid out in a grid. Each cell has a value that is used to represent some characteristic of that location, such as temperature, elevation, or a spectral value.
- File System Raster Datasets – There are three methods to store image and raster data: as files in a file system, within a geodatabase, or managed from within the geodatabase but stored in a file system.
Vulnerability details: GeoNode is an open source platform that facilitates the creation, sharing, and collaborative use of geospatial data. In versions 3.2.0 through 4.1.2, the endpoint `/proxy/?url=` does not properly protect against server-side request forgery. This allows an attacker to port scan internal hosts and request information from internal hosts.
Remedy: A patch is available at commit a9eebae80cb362009660a1fd49e105e7cdb499b9.
Official announcement: For details, please refer to the link – https://nvd.nist.gov/vuln/detail/CVE-2023-40017