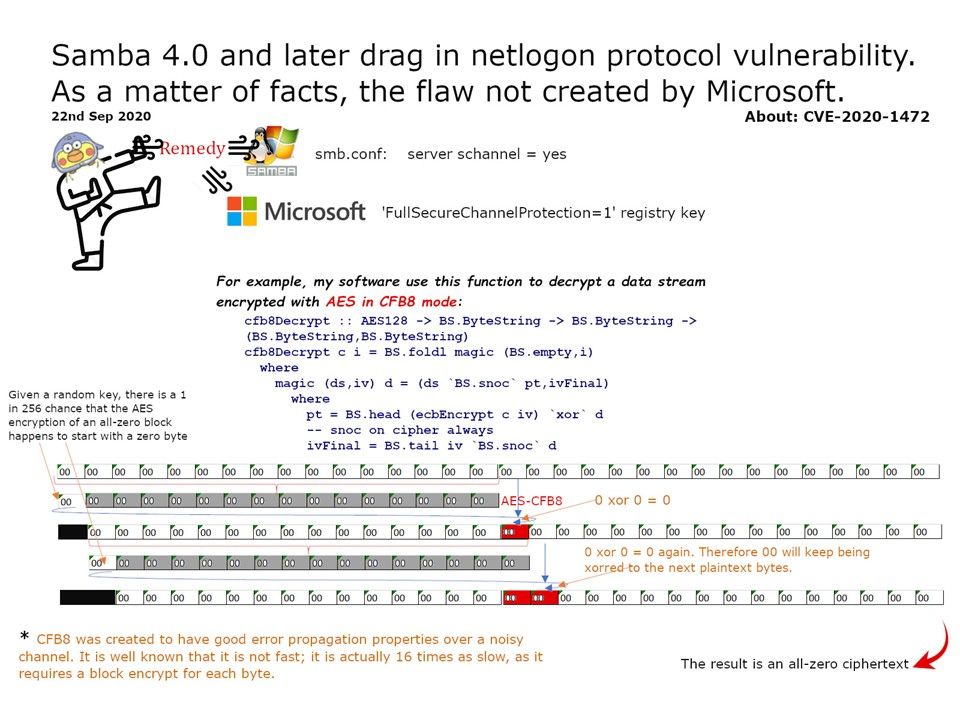
Preface: CFB8 was created to have good error propagation properties over a noisy channel. It is well known that it is not fast; it is actually 16 times as slow, as it requires a block encrypt for each byte.
Details: CVE-2020-1472, also known as “Zerologon,” was given a “critical” security rating from Microsoft. It has possibility let attacker gain fully control all identity services in the AD domain. As a result, any device under the domain will run malicious programs. But this headache will be expand to other 3rd party solution provider. The US government issued an emergency order requiring the Zerologon patch to be completed by next week.
My observation: If you have windows policy applied – accounts locked after invalid login attempts for 3 times. Perhaps it will avoid this attack.
Remediation on Samba server: In samba server config (smb.conf) modify ‘server schannel = yes
Samba official announcement – https://www.samba.org/samba/security/CVE-2020-1472.html
Attached diagram can provide information to you for reference.