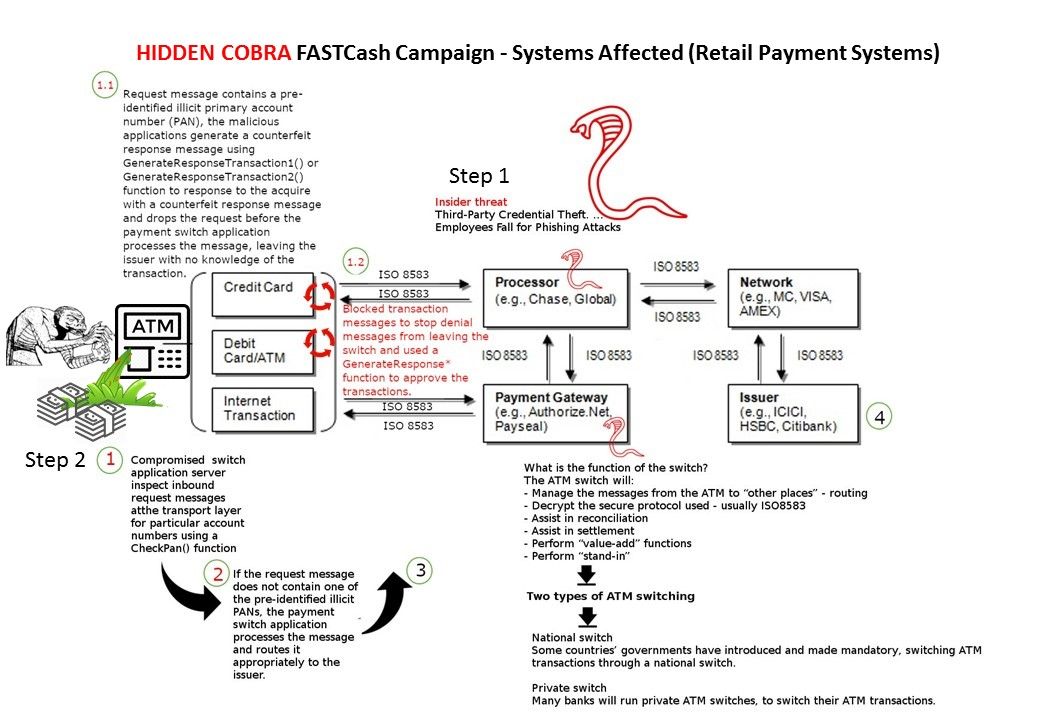
US Homeland security urge banking industry especially payment gateway services provider staying alert of new round of malicious cyber attack of their system. Similar of cyber attack was happened in Taiwan. The heist draw the cash equal to $2.6m (£2.1m). Homeland security reveal how the technique let ATM machine like human vomiting. But this is the bank note. You and me like it.
The key item of this attack is prioritize to compromise the switching application server. Then malicious applications generate a counterfeit response message using GenerateResponseTransaction1() or GenerateResponseTransaction2() function to response to the acquire with a counterfeit response message and drops the request before the payment switch application processes the message. As a result it fool the issuer with no knowledge of the transaction. Should you have interest of above details, please refer to below URL: