Preface: IEEE 802.2 provides two connectionless and one connection-oriented operational modes:
– Type 1 is an unacknowledged connectionless mode for a datagram service.
– Type 2 is a connection-oriented operational mode.
– Type 3 is an acknowledged connectionless service. It supports point-to-point communication only.
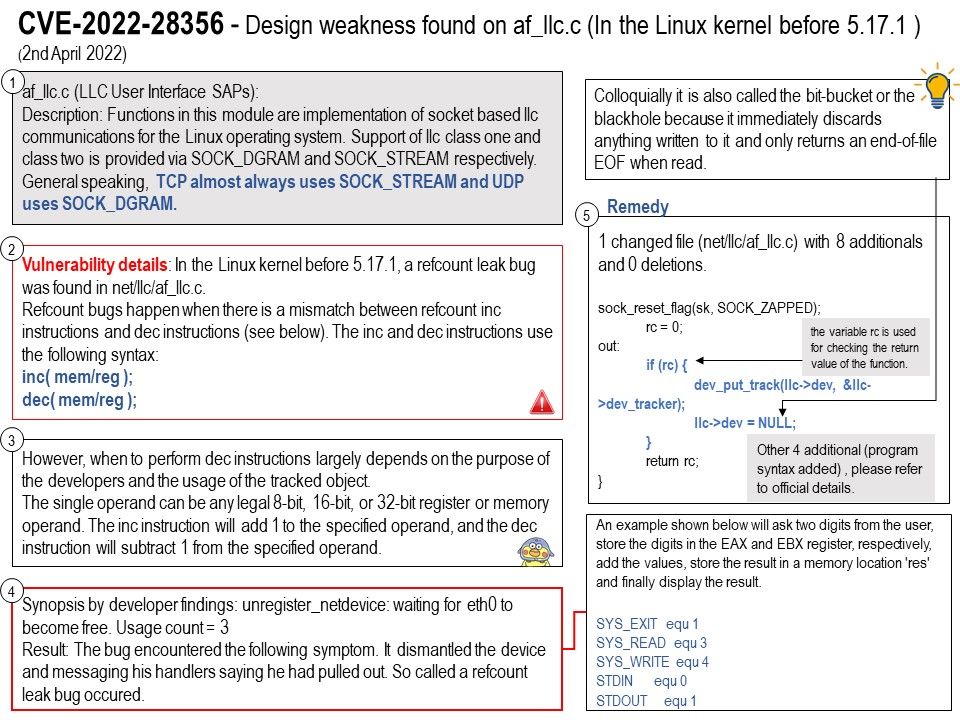
Background: af_llc[.]c (LLC User Interface SAPs):
Description: Functions in this module are implementation of socket based llc communications for the Linux operating system. Support of llc class one and class two is provided via SOCK_DGRAM and SOCK_STREAM respectively.
General speaking, TCP almost always uses SOCK_STREAM and UDP uses SOCK_DGRAM.
Vulnerability details: In the Linux kernel before 5.17.1, a refcount leak bug was found in net/llc/af_llc[.]c. Refcount bugs happen when there is a mismatch between refcount inc instructions and dec instructions (see below).
The inc and dec instructions use the following syntax:
– inc( mem/reg );
– dec( mem/reg );
However, when to perform dec instructions largely depends on the purpose of the developers and the usage of the tracked object.
The single operand can be any legal 8-bit, 16-bit, or 32-bit register or memory operand. The inc instruction will add 1 to the specified operand, and the dec instruction will subtract 1 from the specified operand.
Reminder: Whenever llc_ui_bind() and/or llc_ui_autobind() took a reference on a netdevice but subsequently fail, they must properly release their reference.
Synopsis by developer findings: unregister_netdevice: waiting for eth0 to become free. Usage count = 3
Result: The bug encountered the following symptom. It dismantled the device and messaging his handlers saying he had pulled out. So called a refcount leak bug occured.
Resolution: Upgrade to “Linux-2.6.12-rc2”