Preface: What is backward compatibility in Linux?
Backward compatible (also known as downward compatible or backward compatibility) refers to a hardware or software system that can successfully use interfaces and data from earlier versions of the system or with other systems.
Background: Ansible Automation Platform provides an enterprise framework for building and operating IT automation at scale, from hybrid cloud to the edge. Ansible Automation Platform enables users across an organization to create, share, and manage automation—from development and operations to security and network teams.
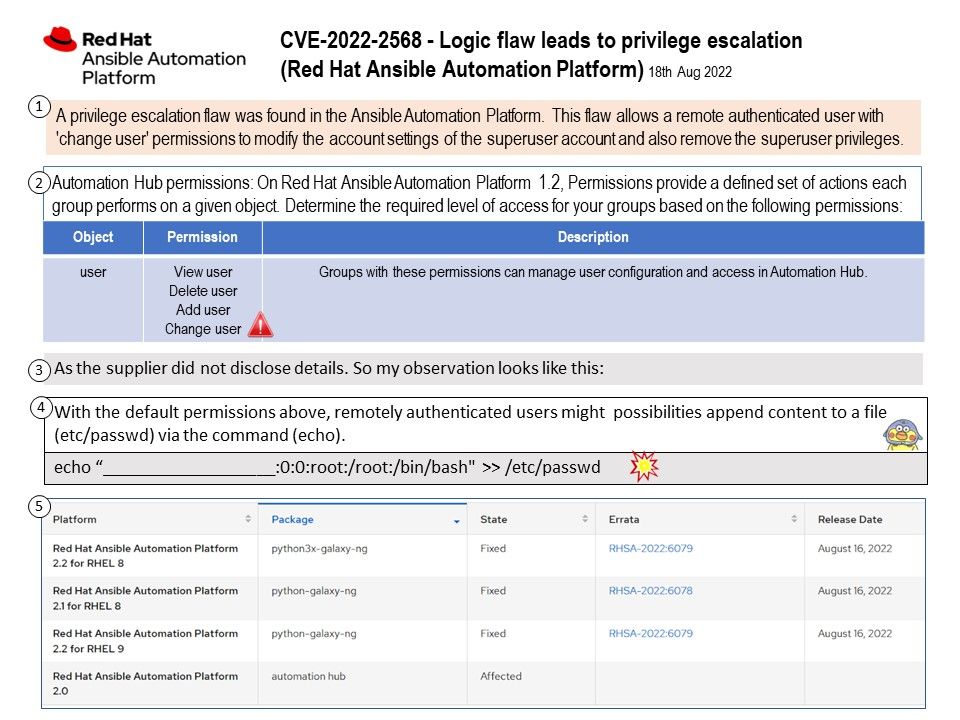
Configure Automation Hub to support your organization by creating groups for your users and providing them with the level of system access they require. For this design, system administrator will configure Automation Hub to support the operation structure by creating groups for users and providing them with the level of system access they require.
The relevant packages are as follows:
- python-galaxy-ng – A Pulp plugin to support hosting your very own Ansible Galaxy server.
- pulpcore-selinux – pulpcore-selinux is a set of SELinux policies for Pulp 3, with several plugins[0] installed.
- openshift-clients – With the OpenShift command-line interface (CLI), the oc command, you can create applications and manage OpenShift Container Platform projects from a terminal.
- automation-hub – The Red Hat Ansible Automation Automation Hub is the official location to discover and download supported Ansible content collections.
- automation-controller – The automation controller allows users of Red Hat® Ansible® Automation Platform to define, operate, scale, and delegate automation across their enterprise.
- ansible-core – Ansible core or ansible-core is the main building block and architecture for Ansible and includes: CLI tools such as ansible-playbook, ansible-doc. and others for driving and interacting with automation.
Vulnerability details: A privilege escalation flaw was found in the Ansible Automation Platform. This flaw allows a remote authenticated user with ‘change user’ permissions to modify the account settings of the superuser account and also remove the superuser privileges.
Official details – https://access.redhat.com/security/cve/cve-2022-2568