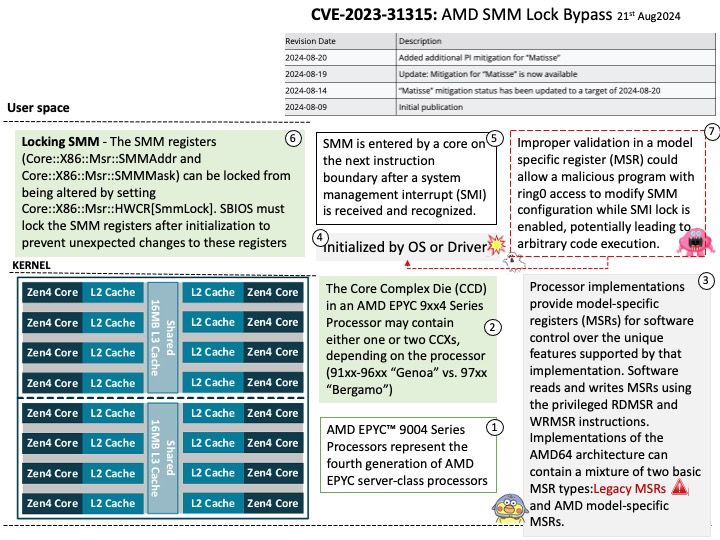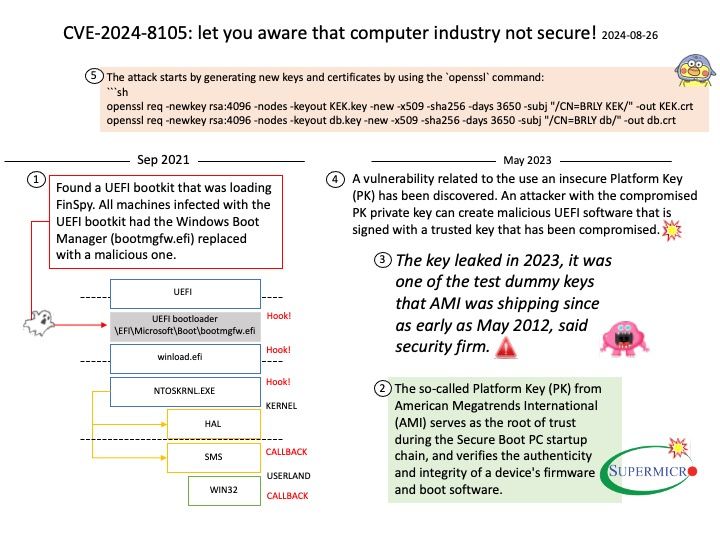
Preface: The key leaked in 2023, it was one of the test dummy keys that AMI was shipping since as early as May 2012, said security firm.
The so-called Platform Key (PK) from American Megatrends International (AMI) serves as the root of trust during the Secure Boot PC startup chain, and verifies the authenticity and integrity of a device’s firmware and boot software.
Background: The so-called Platform Key (PK) from American Megatrends International (AMI) serves as the root of trust during the Secure Boot PC startup chain, and verifies the authenticity and integrity of a device’s firmware and boot software.
Vulnerability details: A vulnerability related to the use an insecure Platform Key (PK) has been discovered. An attacker with the compromised PK private key can create malicious UEFI software that is signed with a trusted key that has been compromised.
Official announcement: Please refer to the link for details – https://www.tenable.com/cve/CVE-2024-8105
https://www.supermicro.com/en/support/security_PKFAIL_Jul_2024