Preface: Why configure Secure Boot? This type of hardware restriction protects the operating system from rootkits and other attacks that may not be detected by antivirus software.
Background: Secure Boot is the process where the operating system boot images and code are authenticated against the hardware before they are authorized to be used in the boot process. The hardware is pre-configured to authenticate code using trusted security credentials. ARM architectures are the most common electronic design in the world, even though x86 is more common in the server market. ARM architectures are used in almost all smartphone designs, as well as in other small mobile devices and laptops.
Arm is the CPU architecture used by all modern smartphones in the Android and Apple ecosystems.
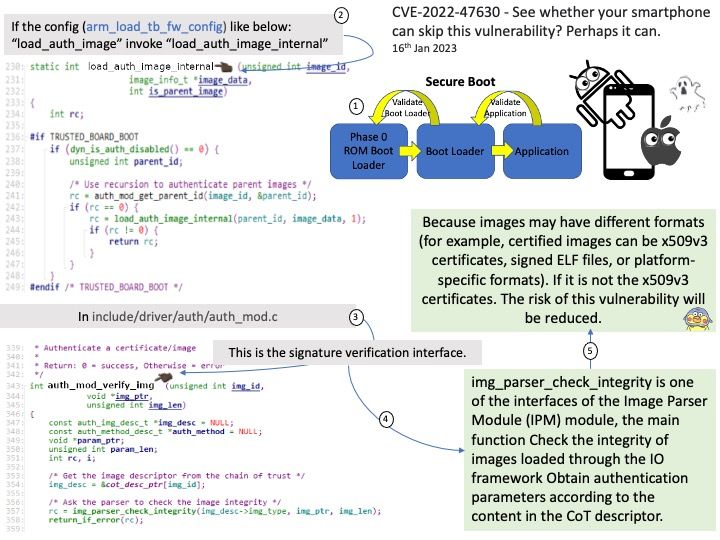
Vulnerability details: Trusted Firmware-A through 2.8 has an out-of-bounds read in the X.509 parser for parsing boot certificates. This affects downstream use of get_ext and auth_nvctr. Attackers might be able to trigger dangerous read side effects or obtain sensitive information about microarchitectural state.
Additional Details – One of its designs is not affected by this vulnerability:
If the config like below:
“load_auth_image” invoke “load_auth_image_internal” – See the attached picture for details
If the platform uses a custom image parser instead of the certificate
parser, the bug in the certificate parser is obviously not relevant. The
bug in auth_nvctr() may be relevant, but only if the returned data is:
- Taken from an untrusted source (meaning that it is read prior to
authentication). - Not already checked to be a primitively-encoded ASN.1 tag.
In particular, if the custom image parser implementation wraps a 32-bit integer in an ASN.1 INTEGER, it is not affected.
Official announcement : Official details, please refer to url – https://nvd.nist.gov/vuln/detail/CVE-2022-47630