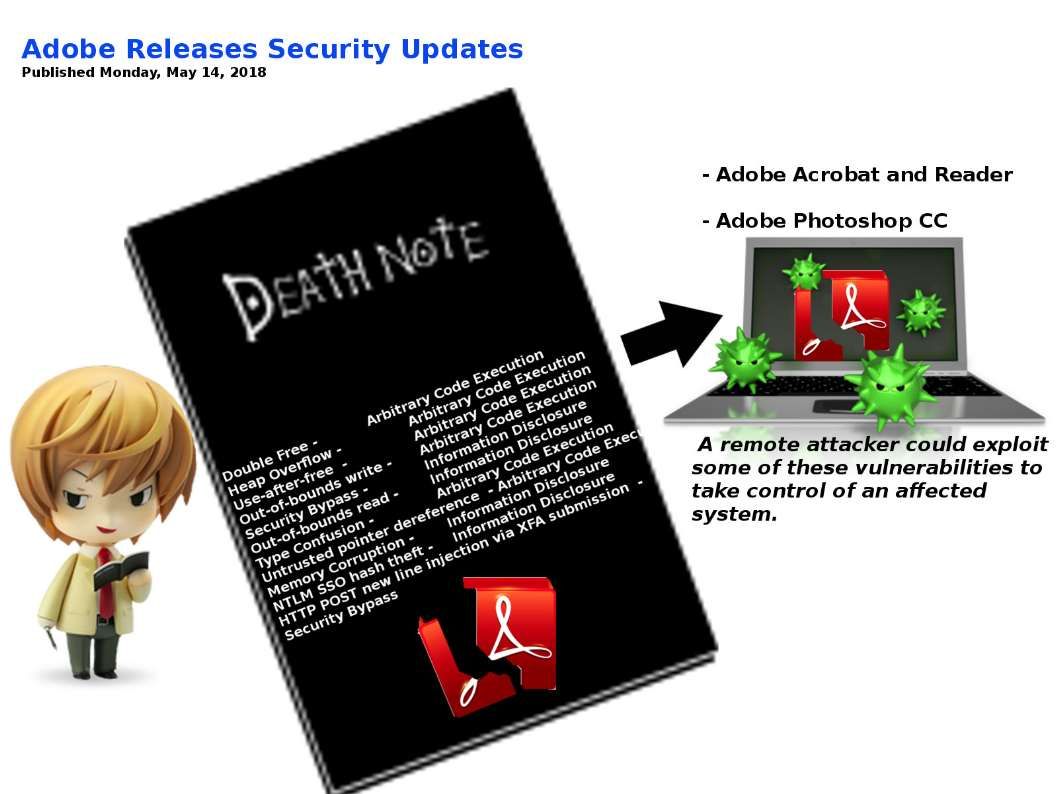
Death Note is a Japanese manga series. The story describ that if someone’s name is written on it while the writer imagines that person’s face, he or she will die. The computer and smartphone devices who installed adobe acrobat reader are in the similar situation. The vulnerabilities in Adobe Acrobat and Reader and Photoshop CC causes a remote attacker could exploit some of these vulnerabilities to take control of an affected system. As a result the system has been compromised. Please be reminded that the Adobe design flaw are critical level of vulnerabilities. IT admin must be staying extra alert.
See below security updates for reference.
Security updates available for Adobe Acrobat and Reader:
https://helpx.adobe.com/security/products/acrobat/apsb18-09.html
Security updates available for Adobe Photoshop CC:
https://helpx.adobe.com/security/products/photoshop/apsb18-17.html