Preface: Snapdragon 8 Gen 2 SoC comes with many new features and technologies such as new tri-cluster architecture, AI improvements, ray tracing support, and more. However, one largely overlooked feature is dual Bluetooth. Now, it’s not going to revolutionize the Bluetooth experience on mobile devices, but it will actually solve some of the fundamental problems we face when using Bluetooth technology on mobile devices.
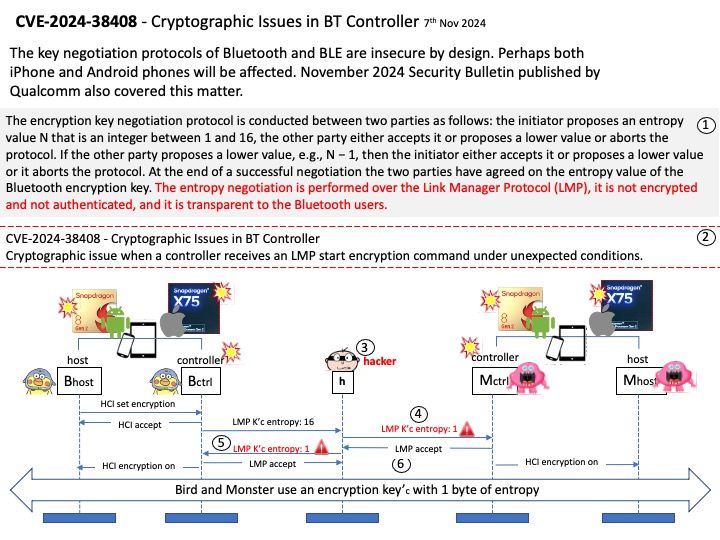
Background: The encryption key negotiation protocol is conducted between two parties as follows: the initiator proposes an entropy value N that is an integer between 1 and 16, the other party either accepts it or proposes a lower value or aborts the protocol. If the other party proposes a lower value, e.g., N − 1, then the initiator either accepts it or proposes a lower value or it aborts the protocol. At the end of a successful negotiation the two parties have agreed on the entropy value of the Bluetooth encryption key. The entropy negotiation is performed over the Link Manager Protocol (LMP), it is not encrypted and not authenticated, and it is transparent to the Bluetooth.
Vulnerability details: Cryptographic issue when a controller receives an LMP start encryption command under unexpected conditions.
Official announcement: Please refer to the vendor announcement for details – https://docs.qualcomm.com/product/publicresources/securitybulletin/november-2024-bulletin.html