Preface: The Databricks Platform is the world’s first data intelligence platform powered by generative AI. Infuse AI into every facet of your business.
Generative artificial intelligence, also known as generative AI or gen AI for short, is a type of AI that can create new content and ideas, including conversations, stories, images, videos, and music. It can learn human language, programming languages, art, chemistry, biology, or any complex subject matter.
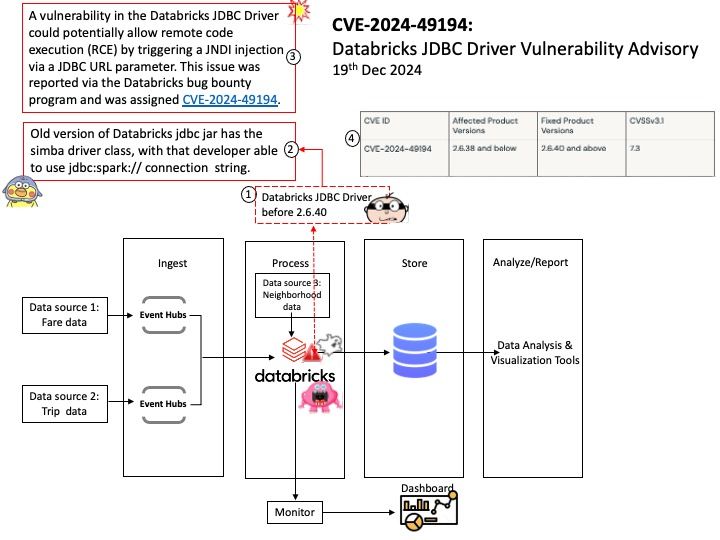
Background: Databricks JDBC, the first version of the driver, is a Simba driver developed by insightsoftware. It enables you to connect participating apps, tools, clients, SDKs, and APIs to Azure Databricks through Java Database Connectivity (JDBC), an industry-standard specification for accessing database management systems.
Vulnerability details: Databricks JDBC Driver before 2.6.40 could potentially allow remote code execution (RCE) by triggering a JNDI injection via a JDBC URL parameter. The vulnerability is rooted in the improper handling of the krbJAASFile parameter. An attacker could potentially exploit this vulnerability to achieve Remote Code Execution in the context of the driver by tricking a victim into using a crafted connection URL that uses the property krbJAASFile.
Official announcement: Please refer to the link for details –https://kb.databricks.com/en_US/data-sources/security-bulletin-databricks-jdbc-driver-vulnerability-advisory-cve-2024-49194