In the view of cryptocurrency supporter, Ethereum is the best. The cyber incident occured in cryptocurrency world so far shift the security focus to e-wallet (end point). Perhaps the cyrpto platform itself contains design limitation. However the end point design of crypto currency platform looks have more space for improvement.
If you install the MetaMask browser plugin, you can manage your accounts in your browser. The keys are stored only on your browser, so you are the only one who has access to your account and the private key. But when the web browser encounter vulnerability. It may jeopardize your private key. So security urge the crypto currency owner make use of hardware token instead of software.
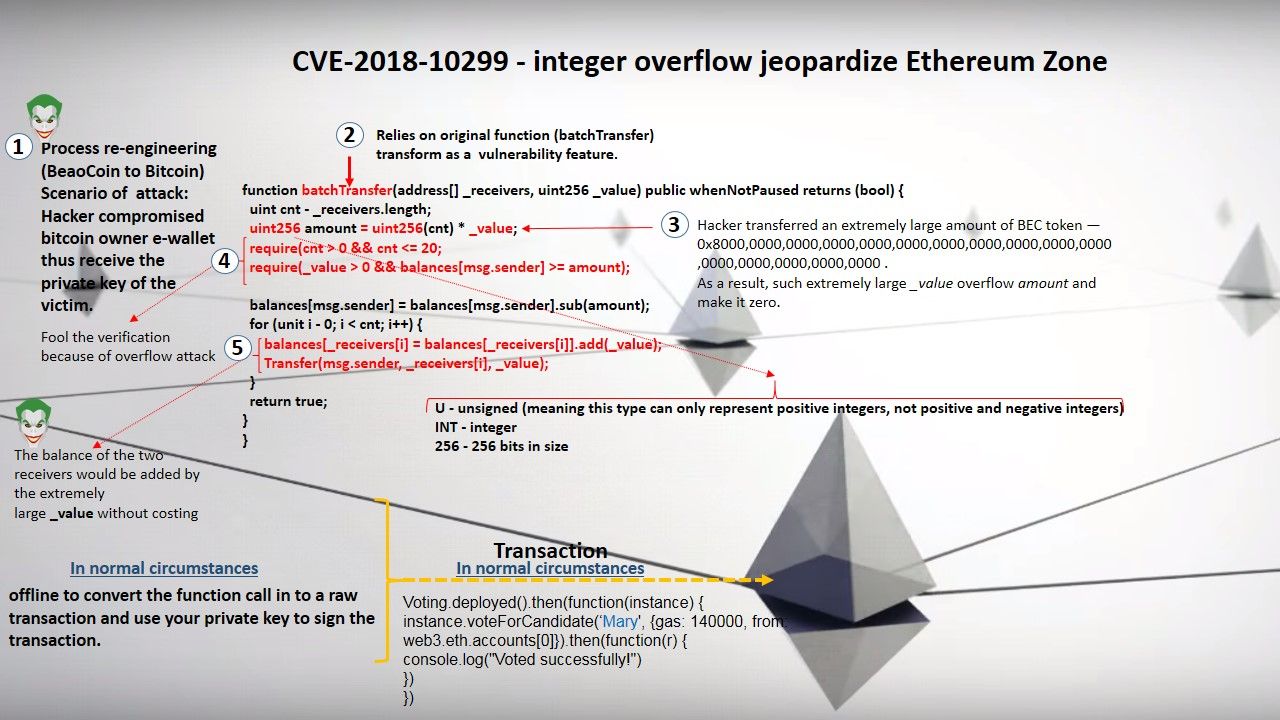
We understand that web3.js is a collection of libraries which allow you to interact with a local or remote Ethereum node, using a HTTP or IPC connection. Java application encounter vulnerabilities caused end user encounter cyber attack is not a news. Above informative diagram shown the integer overflow vulnerability of Ethereum case study involves java applet on the client side. As a front end application, Java application may not aware that he is the accomplice with the cryptocurrency cyber security incident.
Return to reality. Below headline news shown the vulnerabilities occurred in Ethereum (see below for reference). I am wishing that above details can provides hints to you for reference. Let’s us awaken the design weakness of Ethereum cypto currency platform.
Critical EOS Smart Contract Vulnerability Discovered By Auditing Firm
I think this is one of the most significant information for
me. And i am glad reading your article. But should
remark on some general things, The web site style is ideal, the articles is really nice : D.
Good job, cheers
Awesome post .
I don’teven know the way I finished up here, but I believed this post
was once good. I don’t realize who you’re however definitely you are going to a famous bloger if you
happen to are nott already. Cheers!
A fascinating discussion is worth comment. There’s no doubt that that you need to write more
on this issue, it may not be a taboo matter but typically people do not talk about these
subjects. To the next! Cheers!!
Hello there, just became aware of your blog through
Google, and found that it’s truly informative.
I’m gonna watch out for brussels. I will appreciate if you continue this in future.
A lot of people will be benefited from your writing.
Cheers!
If you desire to grow your experience only keep visiting this website
and be updated with the hottest information posted here.
Hi there, I found your site via Google while looking for
a related subject, your site came up, it appears great.
I’ve bookmarked it in my google bookmarks.
Hello there, just was alert to your blog thru Google, and located
that it is truly informative. I am going to watch out for brussels.
I will appreciate in case you proceed this in future.
Numerous other people might be benefited from your writing.
Cheers!
I blog quite often and I really appreciate your information.
Your article has truly peaked my interest. I’m going to book mark your
site and keep checking for new information about once per
week. I opted in for your RSS feed as well.
We’re a bunch of volunteers and opening a
new scheme in our community. Your website offered us with useful info to work on. You have performed a formidable job and our entire neighborhood might be thankful
to you.
Fine way of describing, and nice piece of writing to get data about my presentation subject, which i am going to deliver in institution of
higher education.
Hello to every body, it’s my first visit of this blog; this webpage contains awesome and genuinely good stuff for readers.
It’s really very complicated in this full of activity life to listen news on TV,
therefore I simply use internet for that reason, and take the latest news.
Hi, I read your new stuff regularly. Your humoristic style
is witty, keep it up!
I couldn’t refrain from commenting. Well written!
I can’t believe how great this site is. You keep up the good work. That’s my advice pal.
Awesome things here. I am very happy to peer
your post. Thanks so much and I am taking a look
ahead to touch you. Will you kindly drop me a e-mail?
An interesting discussion is definitely worth comment.
I think that you should publish more on this issue, it might not be a taboo
matter but usually people don’t speak about these subjects.
To the next! All the best!!
Hello there! This is my first visit to your blog! We are a group of
volunteers and starting a new initiative in a community in the same niche.
Your blog provided us valuable information to
work on. You have done a wonderful job!