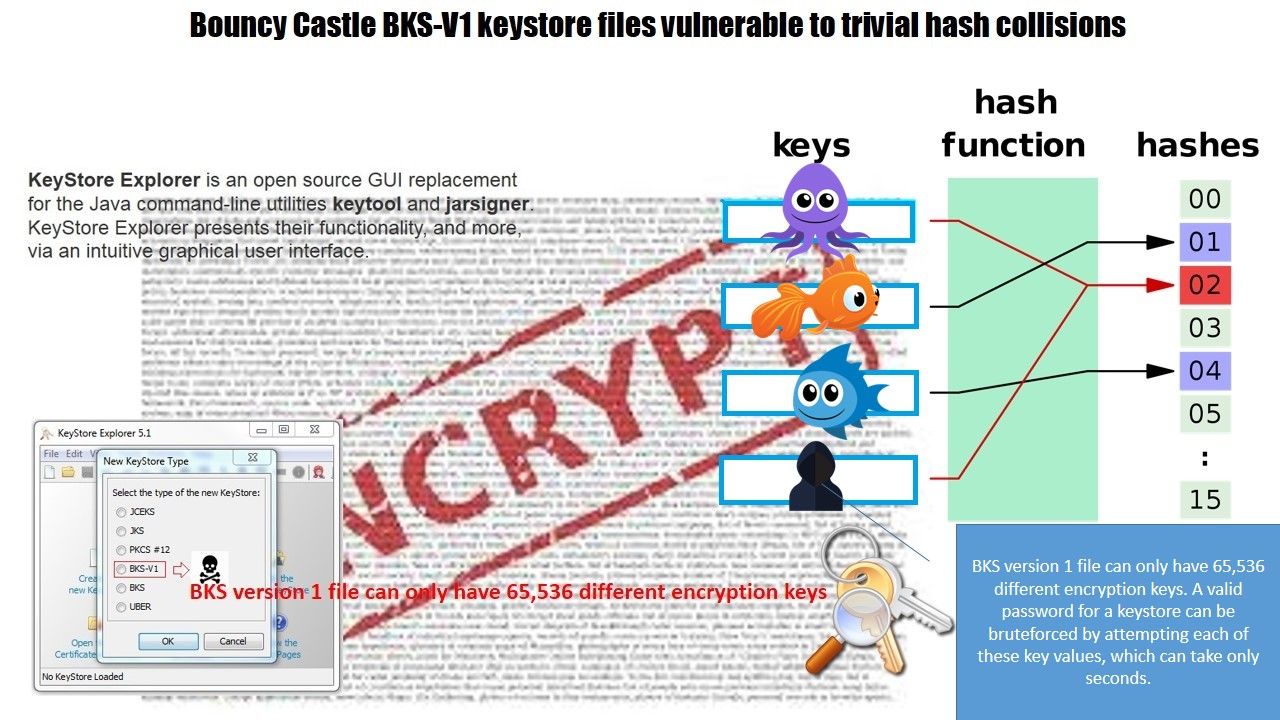
Computer technology world vulnerability exposure can’t slow down. A design weakness on Bouncy Castle BKS-V1 keystore files found. If you are a java program developer. It is a alert signal.
The Bouncy Castle APIs consist of the following:
- A lightweight cryptography API for Java and C#.
- A provider for the Java Cryptography Extension (JCE) and the Java Cryptography Architecture (JCA).
- A provider for the Java Secure Socket Extension (JSSE).
- A clean room implementation of the JCE 1.2.1.
- A library for reading and writing encoded ASN.1 objects. Lightweight APIs for TLS (RFC 2246, RFC 4346) and DTLS (RFC 6347/ RFC 4347).
Generators for Version 1 and Version 3 X.509 certificates, Version 2 CRLs, and PKCS12 files. Generators for Version 2 X.509 attribute certificates.
Generators/Processors for the following:
- S/MIME and CMS (PKCS7/RFC 3852)
- OCSP (RFC 2560) – TSP (RFC 3161 & RFC 5544)
- CMP and CRMF (RFC 4210 & RFC 4211).
- OpenPGP (RFC 4880) – Extended Access Control (EAC)
- Data Validation and Certification Server (DVCS)
- RFC 3029 – DNS-based Authentication of Named Entities (DANE).
- RFC 7030 Enrollment over Secure Transport (EST). A signed jar version suitable for JDK 1.4-1.7 and the Sun JCE.
The vulnerability note can be find here:
https://www.kb.cert.org/vuls/id/306792