Preface: What if you need to decide to buy remote meeting software? In front of you, Microsoft Teams, Zoom, and Cisco WebEx. What is your final decision? Or you decide to buy all, because all three items have design weakness but it is under enhancement.
Background: What is H.323 suite H.323 is a standard developed by the ITU. It specifies packet-based multimedia communications systems across networks, which might not provide any Qos guarantees. H.323 suite is family of standards that includes many other ITU standards (See attached diagram for details).
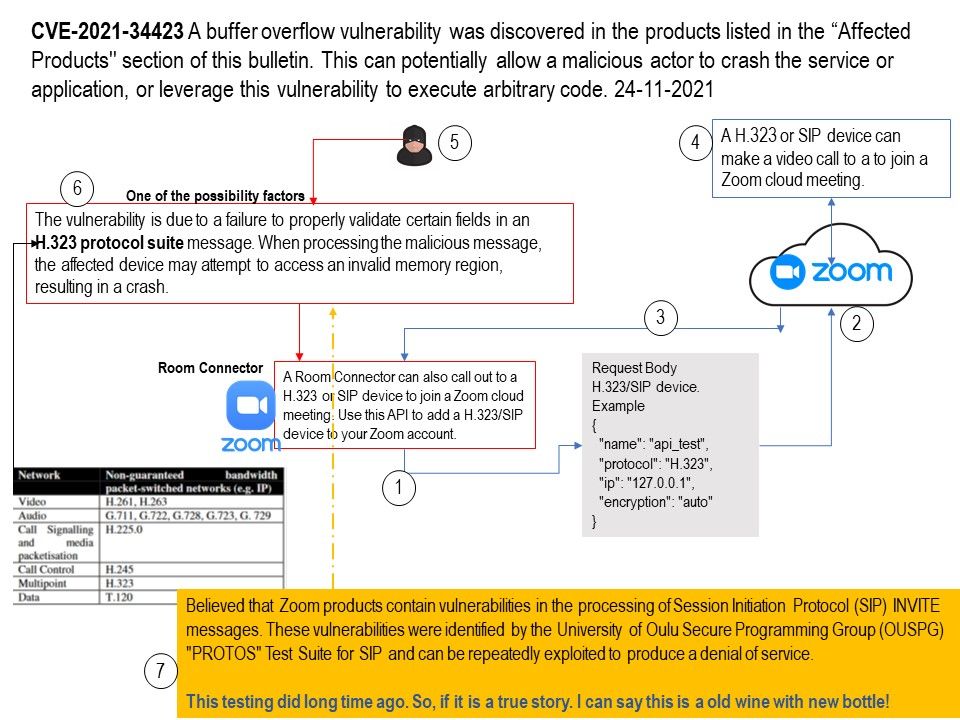
A Room Connector (Zoom) can also call out to a H.323 or SIP device to join a Zoom cloud meeting. Use this API to add a H.323/SIP device to your Zoom account.
A H.323 or SIP device can make a video call to a to join a Zoom cloud meeting.
Vulnerability details: A buffer overflow vulnerability was discovered in the products listed in the “Affected Products” section of this bulletin. This can potentially allow a malicious actor to crash the service or application, or leverage this vulnerability to execute arbitrary code.
Observation 1: The vulnerability is due to a failure to properly validate certain fields in an H.323 protocol suite message. When processing the malicious message, the affected device may attempt to access an invalid memory region, resulting in a crash. An attacker who can submit an H.323 packet designed to trigger the vulnerability could cause the affected device to crash and restart.
Observation 2: Believed that Zoom products contain vulnerabilities in the processing of Session Initiation Protocol (SIP) INVITE messages. These vulnerabilities were identified by the University of Oulu Secure Programming Group (OUSPG) “PROTOS” Test Suite for SIP and can be repeatedly exploited to produce a denial of service.
Official announcement: https://explore.zoom.us/en/trust/security/security-bulletin/