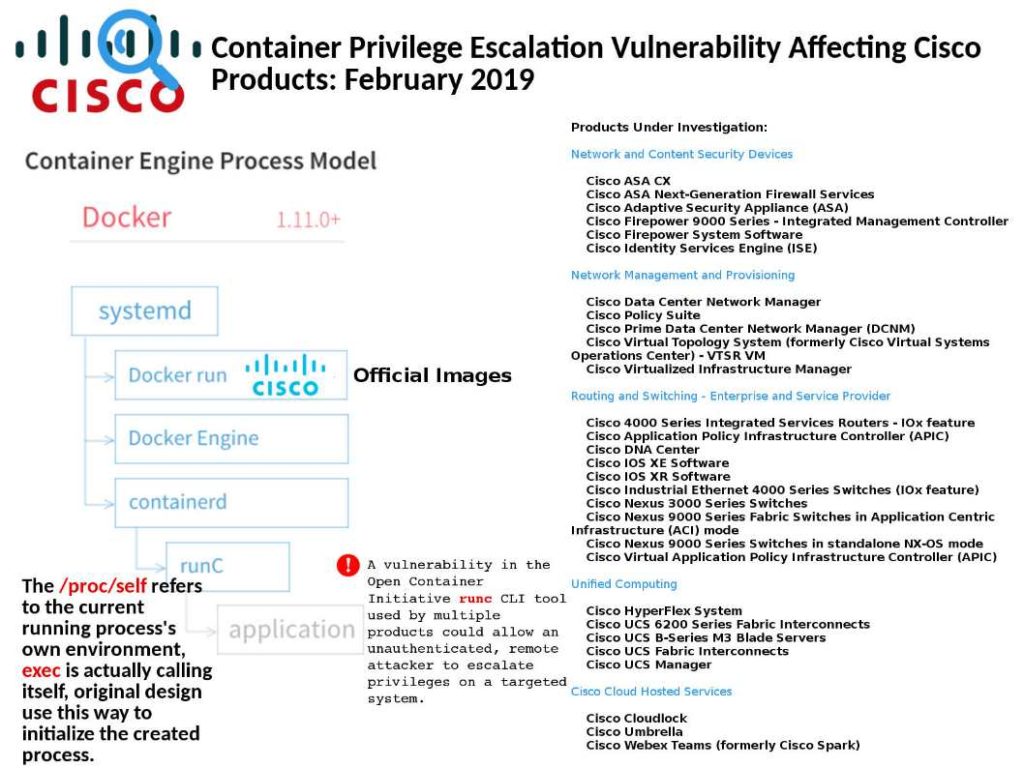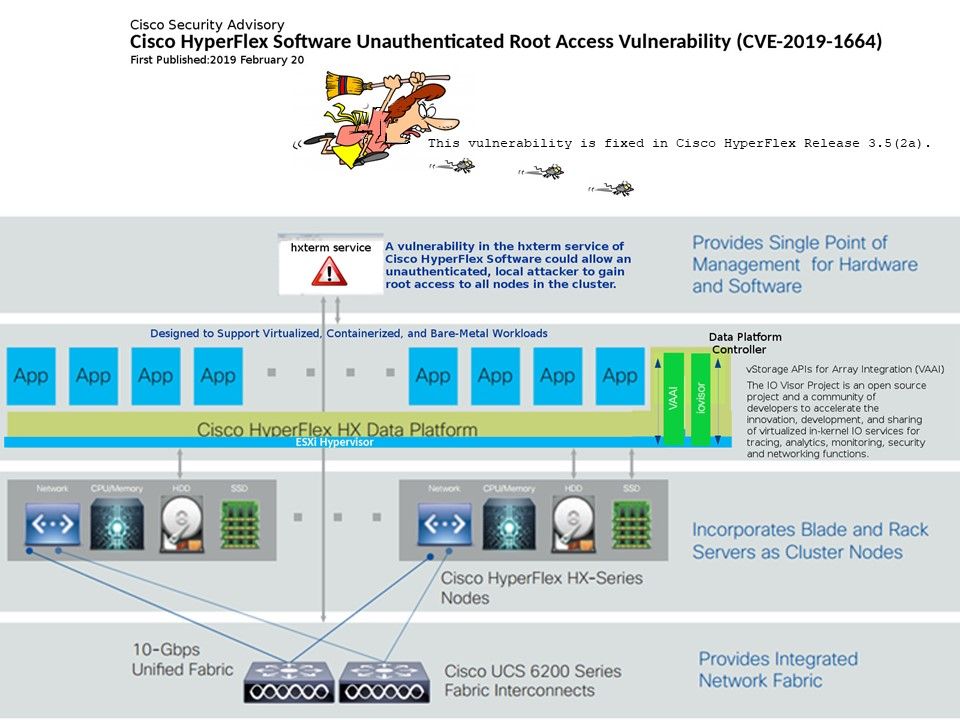
Preface: HyperFlex is Cisco’s hyper-converged infrastructure (HCI) platform. It enable centralized management and enhanced operation efficiency.
Vulnerability detail:
The vulnerability resides in the hxterm service of the Cisco HyperFlex software package and it can “allow an unauthenticated, local attacker to gain root access to all nodes in the cluster, said Cisco.
If the following occurs:
You may login to the HX Data Platform command line interface in the Storage Controller VM in the following ways:
From a browser, a CLI terminal (SSH) and HX Connect Web CLI page.
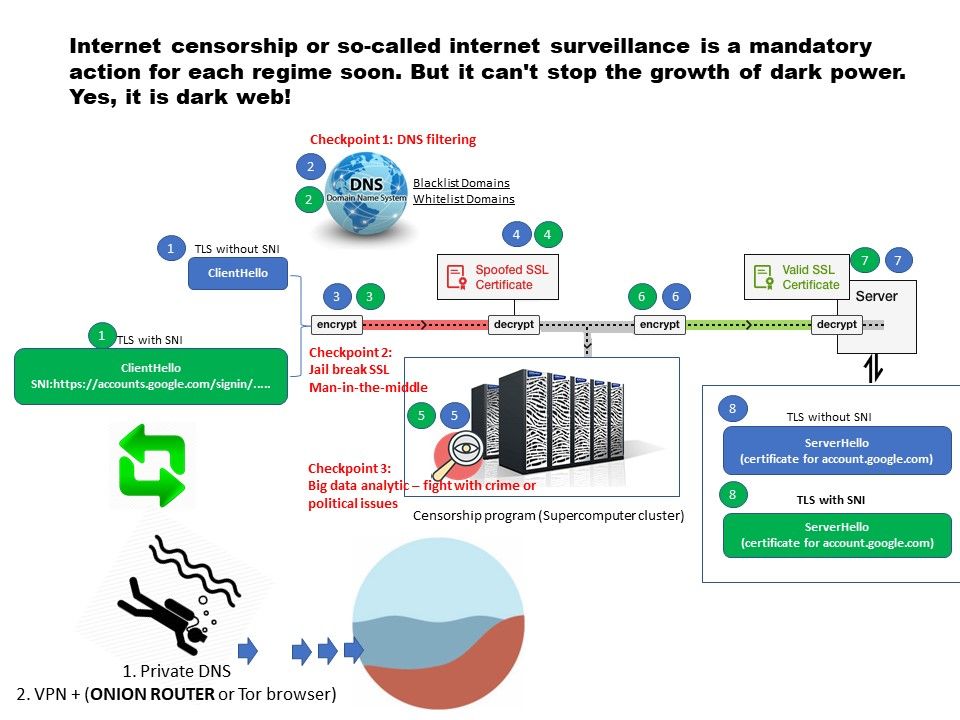
OpenSSH can forward TCP sockets and UNIX domain sockets. If privilege separation is disabled, then on the server side, the forwarding is handled by a child of sshd that has root privileges. If an attacker who is permitted to log in as a normal user over SSH (using “ssh -L”). It can effectively connect to non-abstract unix domain sockets with root privileges.