Preface: This design flaw has attracted me. Perhaps the supplier has no formal remediation solution yet. But the impact of this vulnerability seems to be broad!
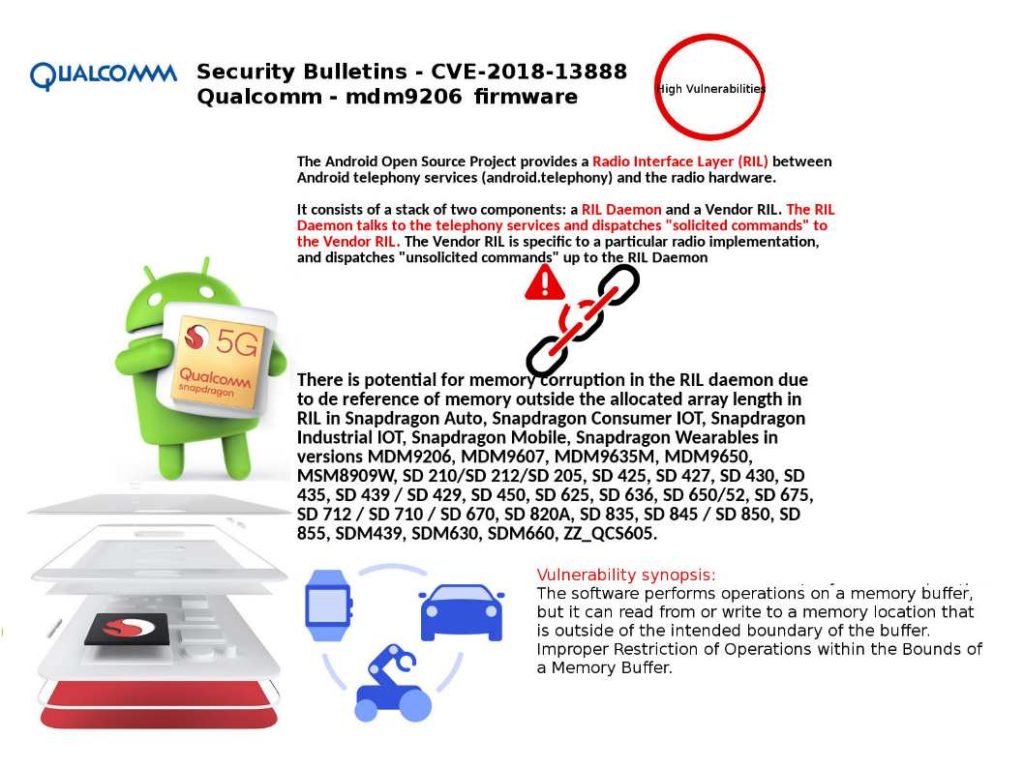
Vulnerability detail: There is potential for memory corruption in the RIL daemon due to the following reason.
The location of dereference of memory is outside the allocated array length in RIL.
Meaning of “dereference” (common criteria):
The dereference operator or indirection operator, sometimes denoted by “*” (i.e. an asterisk), is a unary operator (i.e. one with a single operand) found in C-like languages that include pointer variables.
Affected products: Snapdragon Auto, Snapdragon Consumer IOT, Snapdragon Industrial IOT, Snapdragon Mobile, Snapdragon Wearables in versions MDM9206, MDM9607, MDM9635M, MDM9650, MSM8909W, SD 210/SD 212/SD 205, SD 425, SD 427, SD 430, SD 435, SD 439 / SD 429, SD 450, SD 625, SD 636, SD 650/52, SD 675, SD 712 / SD 710 / SD 670, SD 820A, SD 835, SD 845 / SD 850, SD 855, SDM439, SDM630, SDM660, ZZ_QCS605.
Official announcement – Not found in the bulletins yet : https://www.qualcomm.com/company/product-security/bulletins