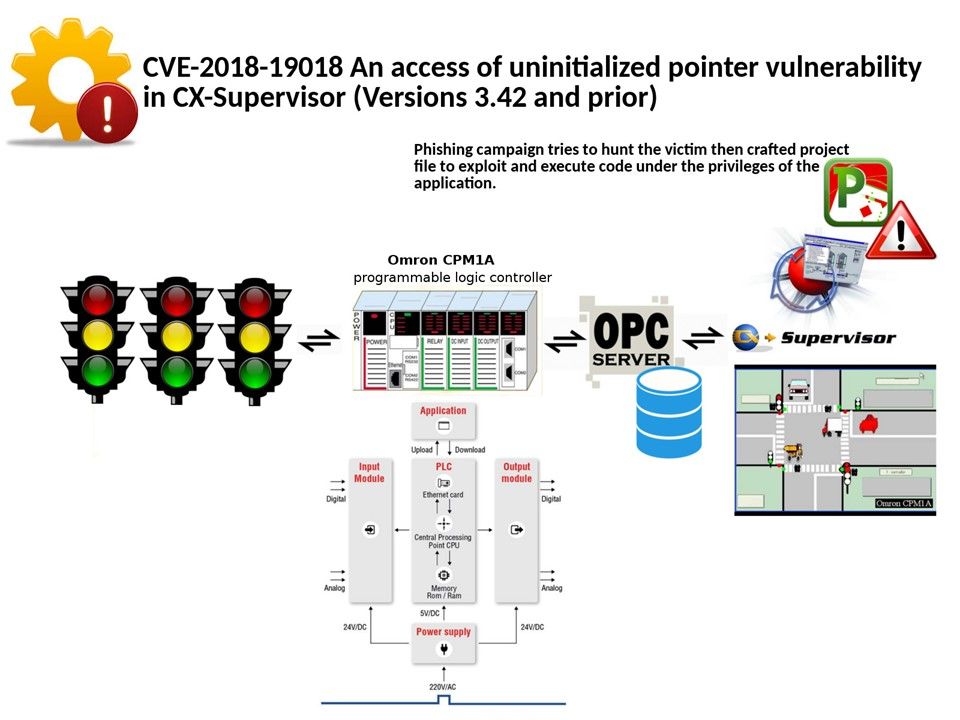
Preface: CX-Supervisor is dedicated to the design and operation of PC visualization and machine control in Omron controller applications.
Technical background: Configuring CX supervisor in OPC and DDE is extremely simple if you have your DDE and OPC server with the SCADA package. CX supervisor contains a large number of predefined functions and libraries, and even very complex applications can be generated with a powerful programming language or VBScript.
Vulnerability detail: CX-Supervisor (Versions 3.42 and prior) has an vulnerability occurs. In technical aspect, we so called access of uninitialized pointer.
That is if the uninitialized pointer is used as a function call, then arbitrary functions could be invoked. If an attacker can influence the portion of uninitialized memory that is contained in the pointer, this weakness could be leveraged to execute code or perform other attacks.
What is the best practice for an pointer?
The best way is setting it to NULL if it doesn’t point to anything.
Vendor announcement (see below url). But it did not mentioned this CVE yet! http://iotsecuritynews.com/omron-cx-supervisor-update-a/