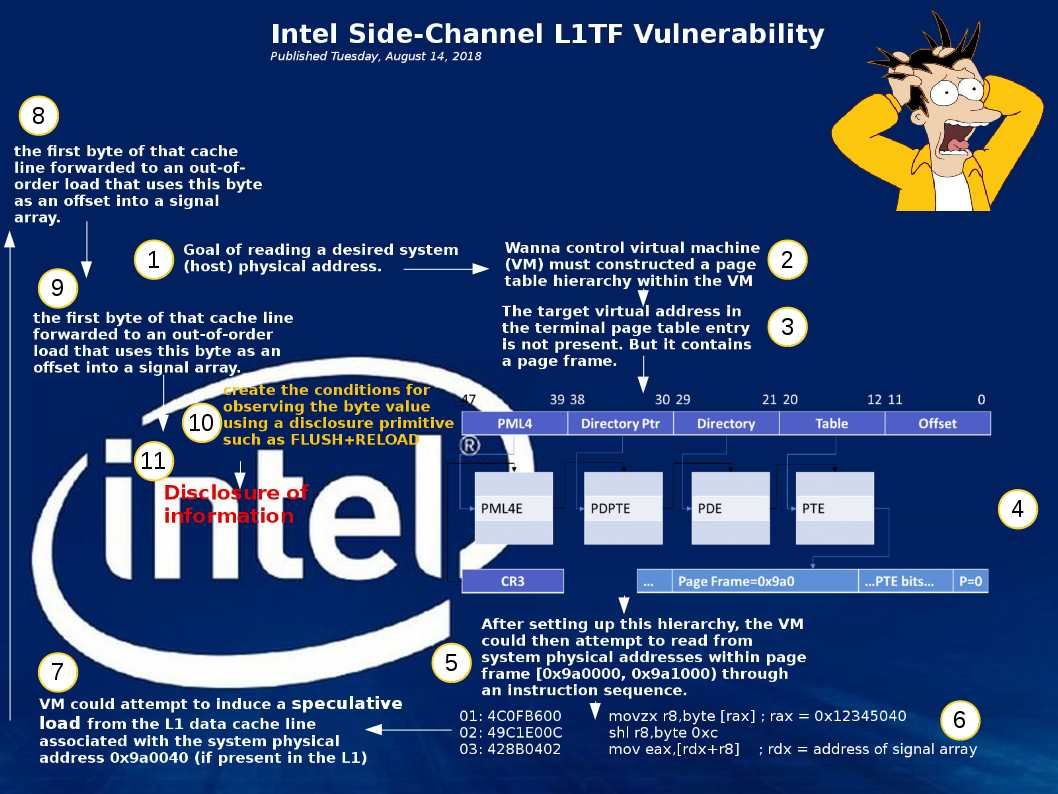
Since the popularity of VM machine. Software development team and IT operations team will do the testing on their own premises in the first. May be you would say, this is not compliance for best practice. But the fact is that this is one of the way. VMware alert to public last week (14th Aug 2018 -CVE-2018-6973). In high level point of view, this vulnerability only occurs in VMware Workstation and Fusion products. VMware workstation is a solution for running virtual machines on Windows and Linux, while Fusion is used for running virtual machines on macOS. So the popularity and volume of usage will be much high than VM server in public. But do not contempt this bug, if such vulnerabilities occurs in your local workstation. It will jeopardizes your infrastructure because you workstation will become vulnerable. Wishing that the attached pictures can tell you the story.
Official reference details shown as below:
https://www.vmware.com/security/advisories/VMSA-2018-0022.html