Preface: You can use Citrix Hypervisor in an unlicensed state. However, you do not have access to some features. To access Citrix hypervisor is easy, go through XenCenter then input user ID and password.
Background: Citrix Hypervisor is a high-performance hypervisor optimized for virtual app and desktop workloads and based on the Xen Project hypervisor. Citrix Hypervisor is optimized for both Windows and Linux virtual servers. It functions lets you create VMs, take VM disk snapshots, and manage VM workloads.
What is Xen Project hypervisor? The Xen Project hypervisor is an open-source type-1 or bare-metal hypervisor. It allows many instances of an operating system or different operating systems to run in parallel on a single machine (or host).
Two components contribute to the memory footprint of the Citrix Hypervisor server. First, the memory consumed by the Xen hypervisor itself. Second, there is the memory consumed by the Control Domain of the host.
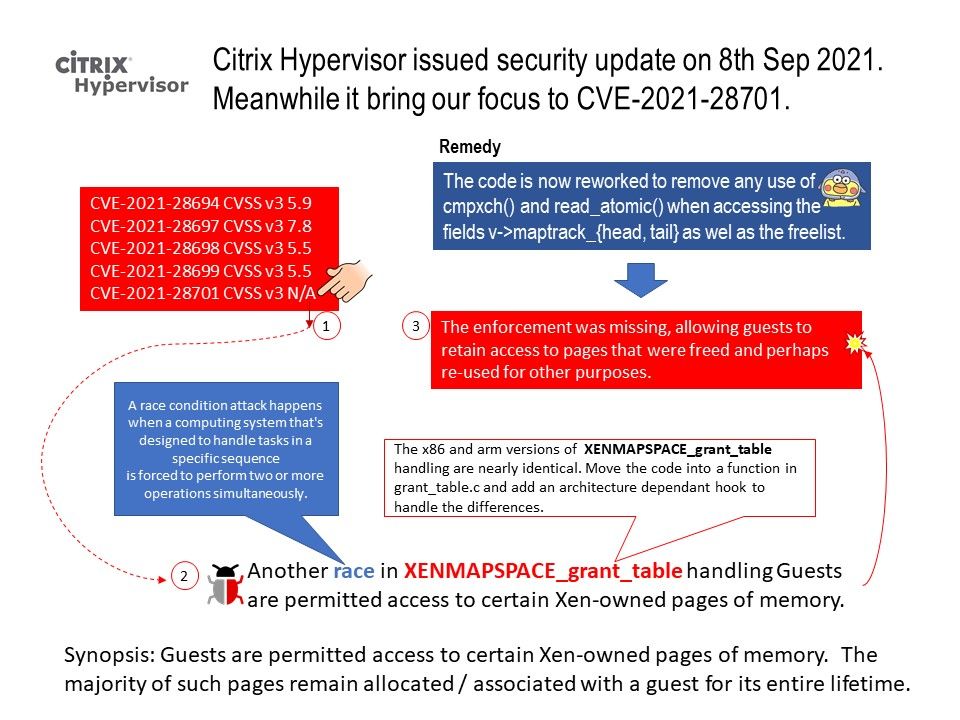
Vulnerability details: Guests are permitted access to certain Xen-owned pages of memory. The majority of such pages remain allocated / associated with a guest for its entire lifetime. Freeing such pages requires that the hypervisor enforce that no parallel request can result in the addition of a mapping of such a page to a guest. That enforcement was missing, allowing guests to retain access to pages that were freed and perhaps re-used for other purposes.
Mitigation: Running only PV guests will avoid this vulnerability. Suppressing use of grant table v2 interfaces for HVM or PVH guests will also avoid this vulnerability.
Citrix Hypervisor Security Update – https://support.citrix.com/article/CTX325319