Preface: On macOS, dynamic-link libraries are known as dylib files. This is the equivalent to a DLL on Windows and
a shared library (or .so library) on Linux.
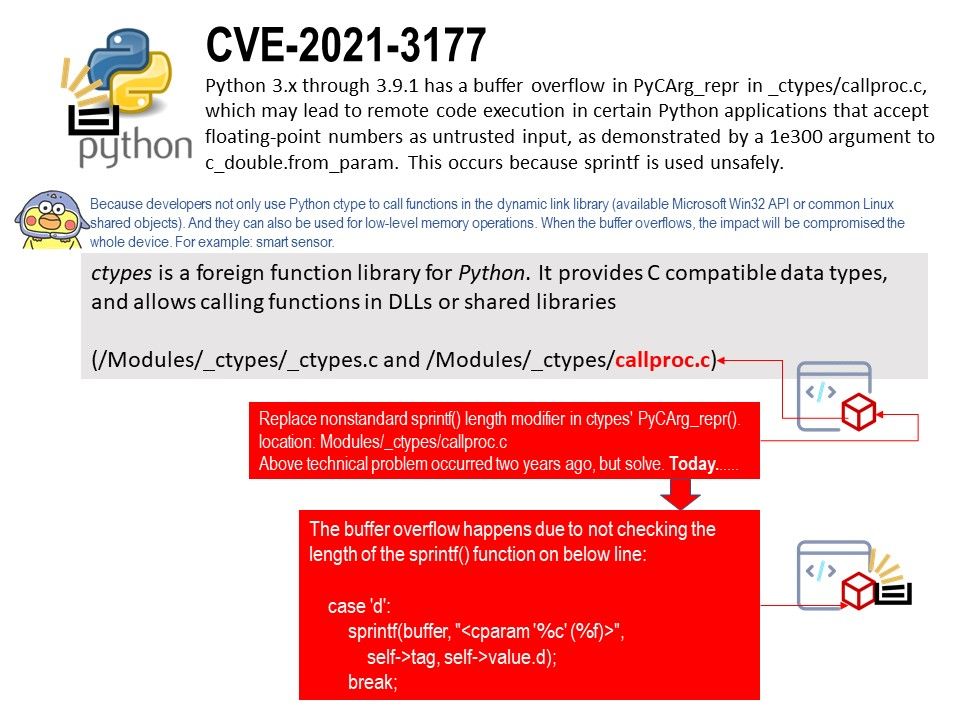
Background: ctypes is a foreign function library for Python. It provides C compatible data types, and allows calling functions in DLLs or shared libraries. It can be used to wrap these libraries in pure Python.
Design objective: Calling C++ libraries from Python allows the developer to build an application that takes advantage of the best of Python and C++. The result is an application that combines both speed and simplicity.
Vulnerability details: There’s a buffer overflow in the ctypes PyCArg_repr() function. (Disclosure date: 2021-01-16)
Design weakness: There’s a buffer overflow in the PyCArg_repr() function in _ctypes/callproc.c.
The buffer overflow happens due to not checking the length of specify sprintf() function.
CVE Details: https://nvd.nist.gov/vuln/detail/CVE-2021-3177