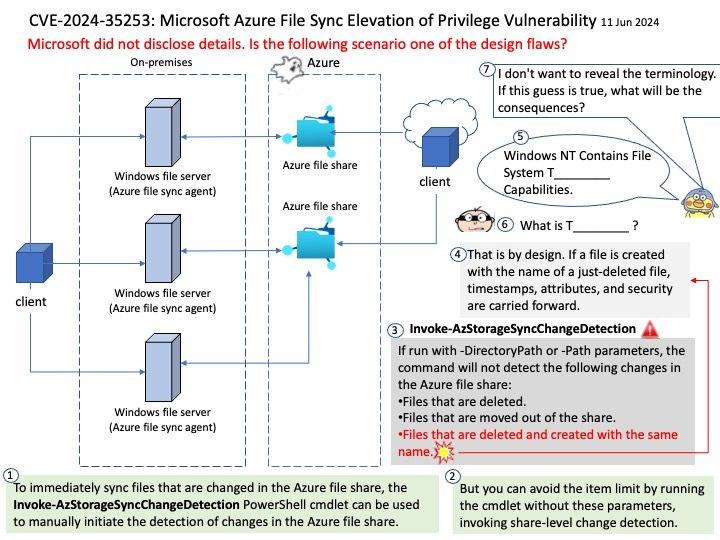
Preface: That is by design. If a file is created with the name of a just-deleted file, timestamps, attributes, and security are carried forward.
Background: To immediately sync files that are changed in the Azure file share, the Invoke-AzStorageSyncChangeDetection PowerShell cmdlet can be used to manually initiate the detection of changes in the Azure file share.
This cmdlet is intended for scenarios where some type of automated process is making changes in the Azure file share or the changes are done by an administrator (like moving files and directories into the share). For end user changes, the recommendation is to install the Azure File Sync agent in an IaaS VM and have end users access the file share through the IaaS VM. This way all changes will quickly sync to other agents without the need to use the Invoke-AzStorageSyncChangeDetection cmdlet.
Vulnerability details: Microsoft Azure File Sync Elevation of Privilege Vulnerability
Official announcement: For detail, please refer to link – https://nvd.nist.gov/vuln/detail/CVE-2024-35253