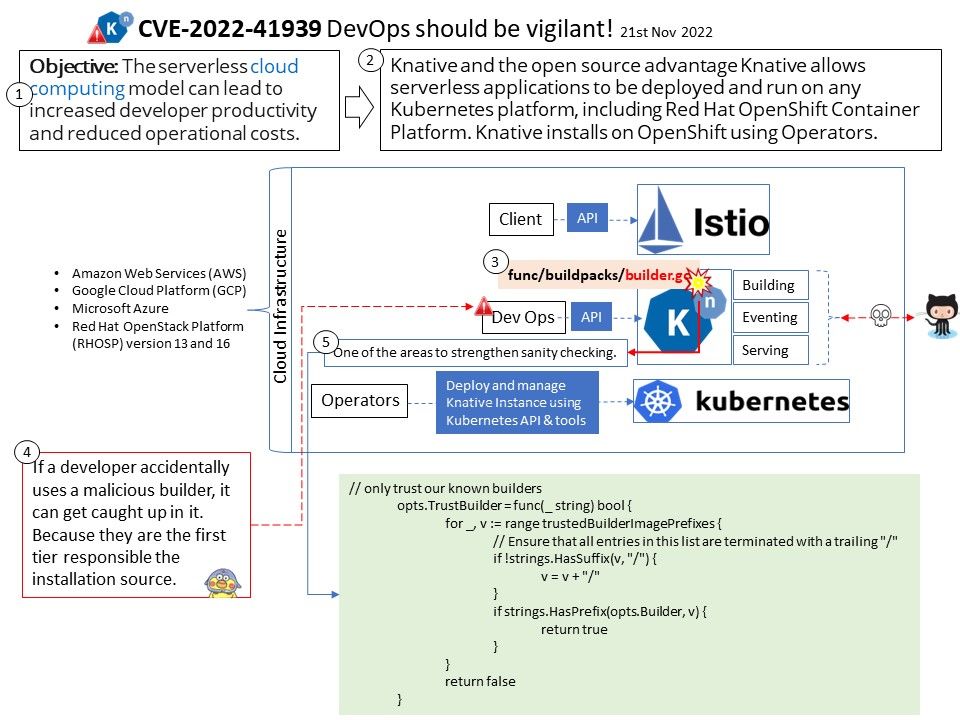
Preface:Serverless functions not only make the deployment of new code quicker, simpler, and easy to automate — they also significantly decrease the possibility of downtime during a deploy.To those already familiar with the concepts of Serverless functions, they known Knative introduces some new cyber security challenges.
Background: Knative and the open source advantage Knative allows serverless applications to be deployed and run on any Kubernetes platform, including Red Hat OpenShift Container Platform. Knative installs on OpenShift using Operators. Knative offers features like scale-to-zero, autoscaling, in-cluster builds, and eventing framework for cloud-native applications on Kubernetes. Whether on-premises, in the cloud, or in a third-party data center, Knative codifies the best practices shared by successful real-world Kubernetes-based frameworks.
Knative fall into below categories:
- A simple process that watched a message queue and called other services based on the message payload (in a similar fashion to the classic Message Router EIP)
- Creating an API aggregation or request batching
Service that exposed a single API endpoint that returned data via the internal orchestration of multiple batched requests to additional upstream services, the aggregated responses.
Vulnerability details: A vulnerability has been found in knative func (knative[.]dev/func) up to 1.8.0. This vulnerability affects an unknown code block. knative[.]dev/func is is a client library and CLI enabling the development and deployment of Kubernetes functions. Developers using a malicious or compromised third-party buildpack could expose their registry credentials or local docker socket to a malicious lifecycle container.
Solution: Upgrading to version 1.8.1 eliminates this vulnerability.
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2022-41939