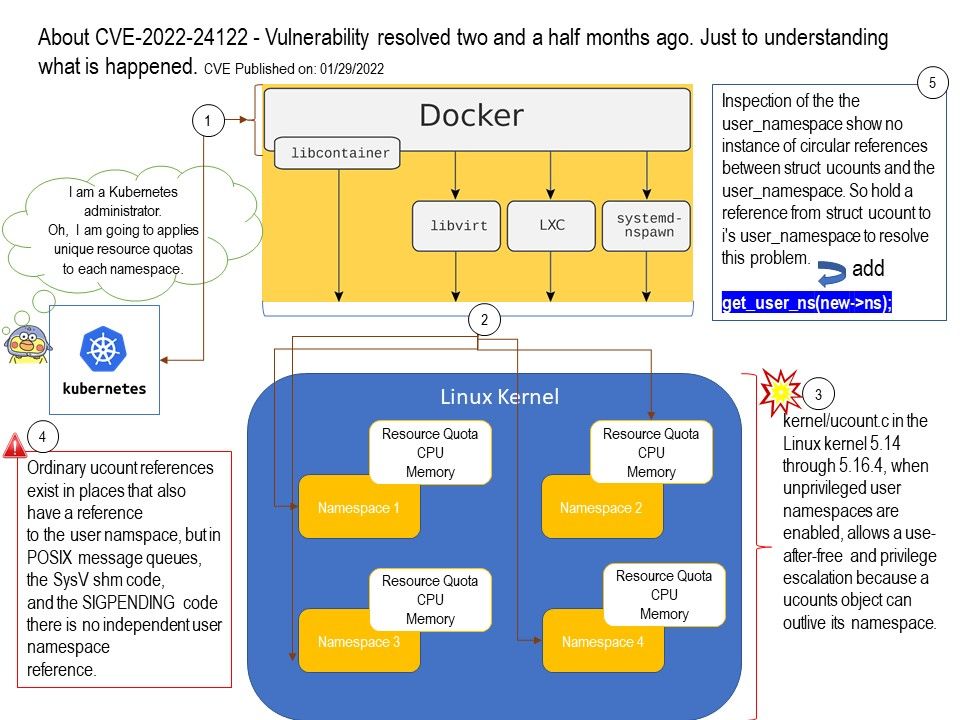
Preface: If you are a Kubernetes administrator, doing the resources distribution, may be it is a daily routine job. Regarding to this vulnerability, have you resolve yet?
Background: Namespaces are one of the main features of the Linux kernel – they carry out the distinction between kernel resources. It makes sure that a process can only see the specified set of resources. Examples of resources are process IDs, hostnames, files, usernames, network access names, and inter-process communications.
Vulnerability details: kernel/ucount[.]c in the Linux kernel 5.14 through 5.16.4, when unprivileged user namespaces are enabled, allows a use-after-free and privilege escalation because a ucounts object can outlive its namespace.
Ref: Ordinary ucount references exist in places that also have a reference to the user namspace, but in POSIX message queues, the SysV shm code,and the SIGPENDING code there is no independent user namespace reference.
Inspection of the the user_namespace show no instance of circular references between struct ucounts and the user_namespace. So hold a reference from struct ucount to i’s user_namespace to resolve this problem.
Remediation: Please refer to the link for details – https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=f9d87929d451d3e649699d0f1d74f71f77ad38f5