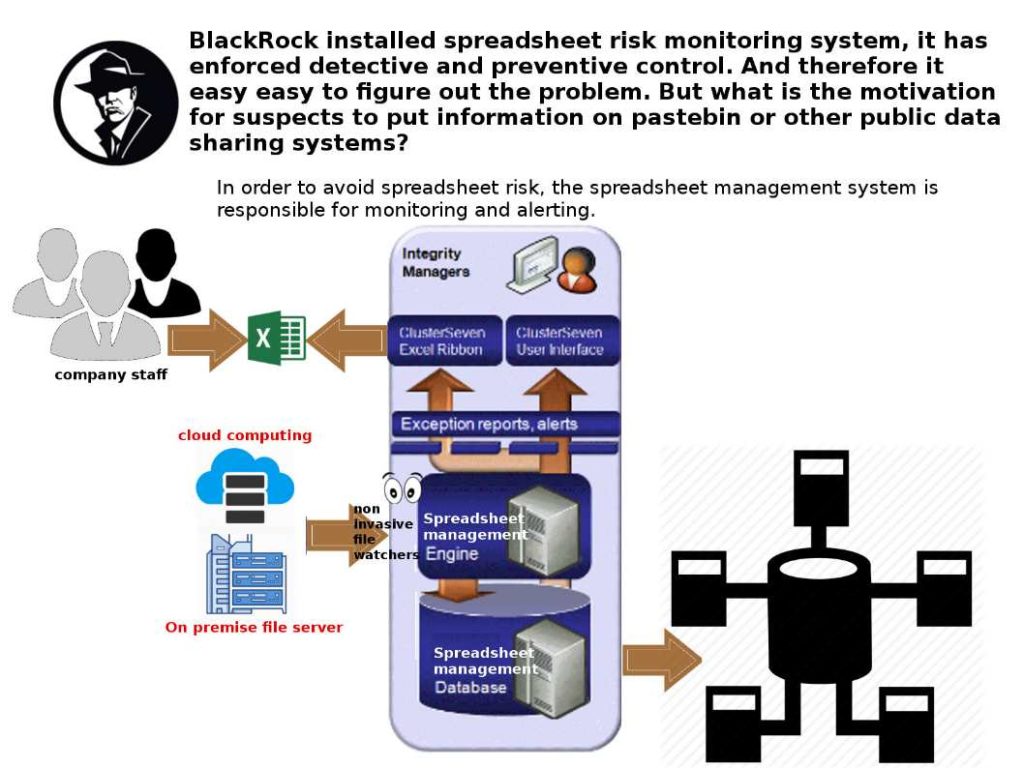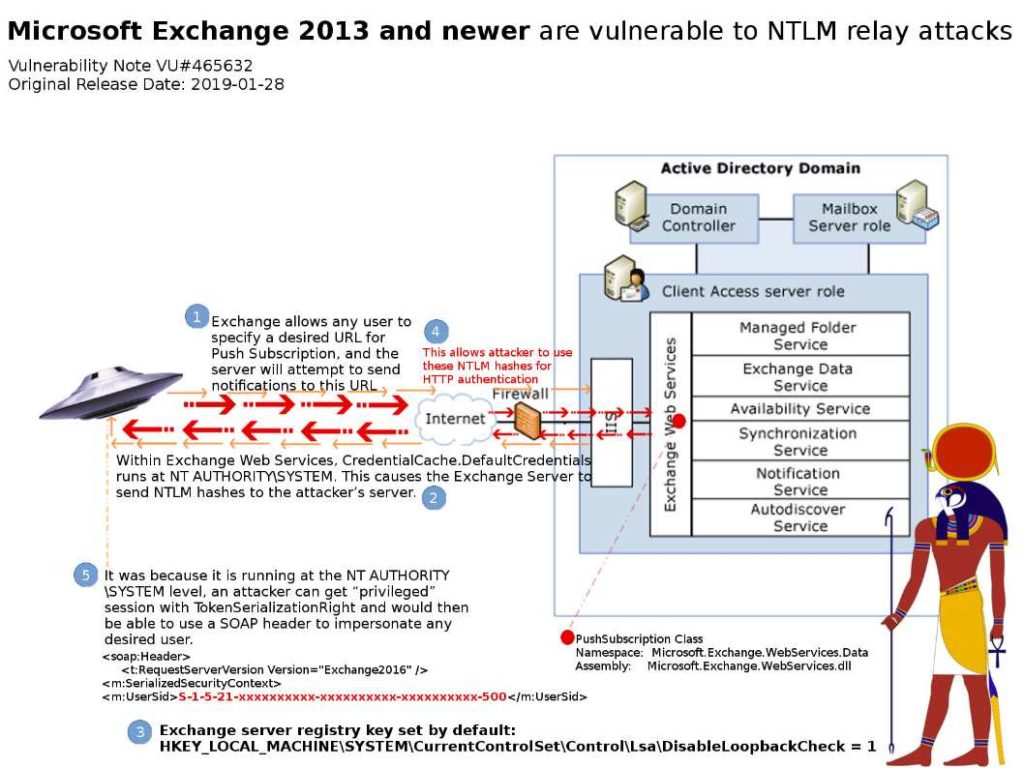
Preface: EWS Push Subscription, you will get notifications as long as you respond to the server and acknowledge that you received the notification.
The CERT Coordination Center (CERT/CC) announcement – 29th Jan 2019: Microsoft Exchange 2013 and newer are vulnerable to NTLM relay attacks
Vulnerability detail: Exchange allows any user to specify a desired URL for Push Subscription, and the server will attempt to send notifications to this URL….. For more detail, please refer to attached diagram for reference.
Remedy:
- Disable EWS push/pull subscriptions.
- Remove privileges that Exchange has on the domain object.
Technical article for reference: https://www.kb.cert.org/vuls/id/465632/