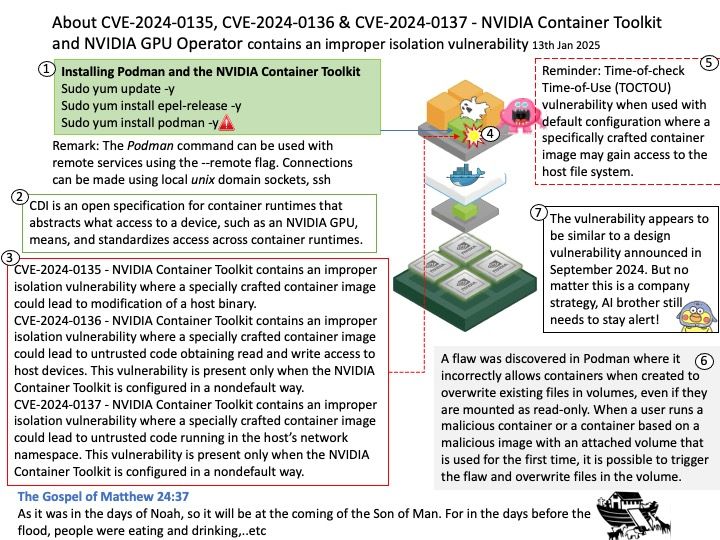
Preface: In software development, time-of-check to time-of-use (TOCTOU, TOCTTOU or TOC/TOU) is a class of software bugs caused by a race condition involving the checking of the state of a part of a system (such as a security credential) and the use of the results of that check.
Background: The NVIDIA container stack is architected so that it can be targeted to support any container runtime in the ecosystem. The components of the stack include:
-The NVIDIA Container Runtime (nvidia-container-runtime)
-The NVIDIA Container Runtime Hook (nvidia-container-toolkit / nvidia-container-runtime-hook)
-The NVIDIA Container Library and CLI (libnvidia-container1, nvidia-container-cli)
The components of the NVIDIA container stack are packaged as the NVIDIA Container Toolkit.
The NVIDIA Container Toolkit is a key component in enabling Docker containers to leverage the raw power of NVIDIA GPUs. This toolkit allows for the integration of GPU resources into your Docker containers.
Remark: The Podman command can be used with remote services using the –remote flag. Connections can be made using local unix domain sockets, ssh
Vulnerability details:
CVE-2024-0135 – NVIDIA Container Toolkit contains an improper isolation vulnerability where a specially crafted container image could lead to modification of a host binary. A successful exploit of this vulnerability may lead to code execution, denial of service, escalation of privileges, information disclosure, and data tampering.
CVE-2024-0136 – NVIDIA Container Toolkit contains an improper isolation vulnerability where a specially crafted container image could lead to untrusted code obtaining read and write access to host devices. This vulnerability is present only when the NVIDIA Container Toolkit is configured in a nondefault way. A successful exploit of this vulnerability may lead to code execution, denial of service, escalation of privileges, information disclosure, and data tampering.
CVE-2024-0137 – NVIDIA Container Toolkit contains an improper isolation vulnerability where a specially crafted container image could lead to untrusted code running in the host’s network namespace. This vulnerability is present only when the NVIDIA Container Toolkit is configured in a nondefault way. A successful exploit of this vulnerability may lead to denial of service and escalation of privileges.
Official announcement: Please refer to the vendor announcement for detail – https://nvidia.custhelp.com/app/answers/detail/a_id/5599