Preface: Graphics card not detected in Device Manager, BIOS – It’s possible that your graphics card isn’t properly connected, or this is usually caused by incompatible drivers.
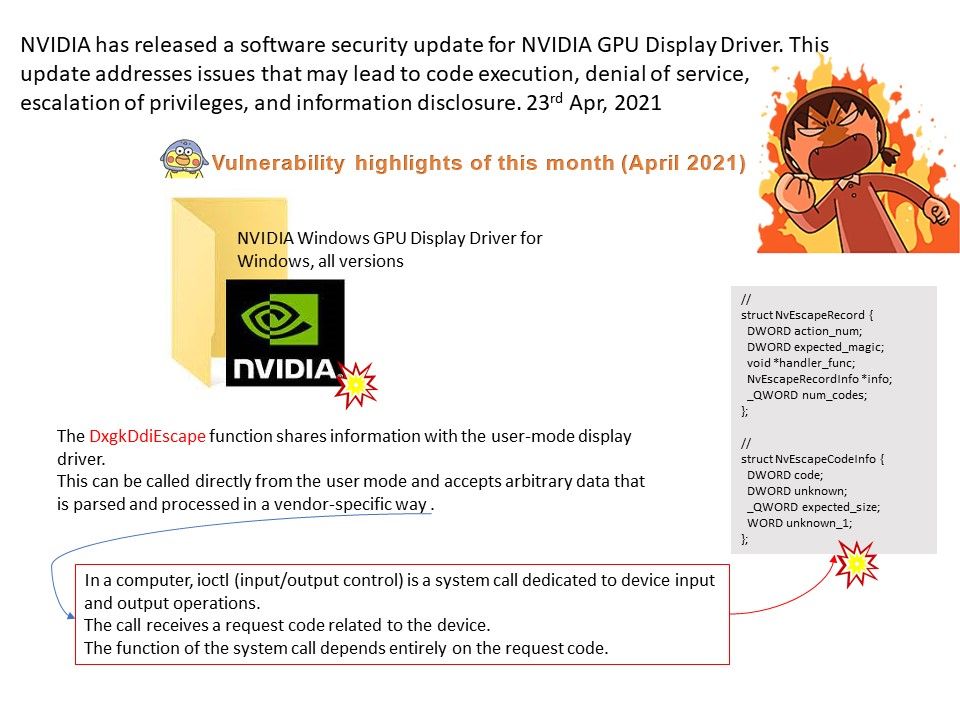
Background: The DxgkDdiEscape function shares information with the user-mode display driver. This can be called directly from the user mode and accepts arbitrary data that is parsed and processed in a vendor-specific way. This design weakness found by Google project Zero team long time ago.
The GPU manufacturer had official announcement this month.
Vulnerability details: NVIDIA Windows GPU Display Driver for Windows, all versions, contains a vulnerability in the kernel mode layer (nvlddmkm.sys) handler for DxgkDdiEscape where the program dereferences a pointer that contains a location for memory that is no longer valid, which may lead to code execution, denial of service, or escalation of privileges.
Remedy: Security Bulletin: NVIDIA GPU Display Driver – April 2021 – https://nvidia.custhelp.com/app/answers/detail/a_id/5172