_Security_Update.jpg?width=1920&height=1080&fit=bounds)
Preface: The Improper Access Control weakness describes a case where software fails to restrict access to an object properly.
Background: Citrix Workspace ensures corporate data is safe and malicious activities are spotted quickly. If the installation is user-based, Citrix Workspace app must be installed for each user who logs on to the local machine.
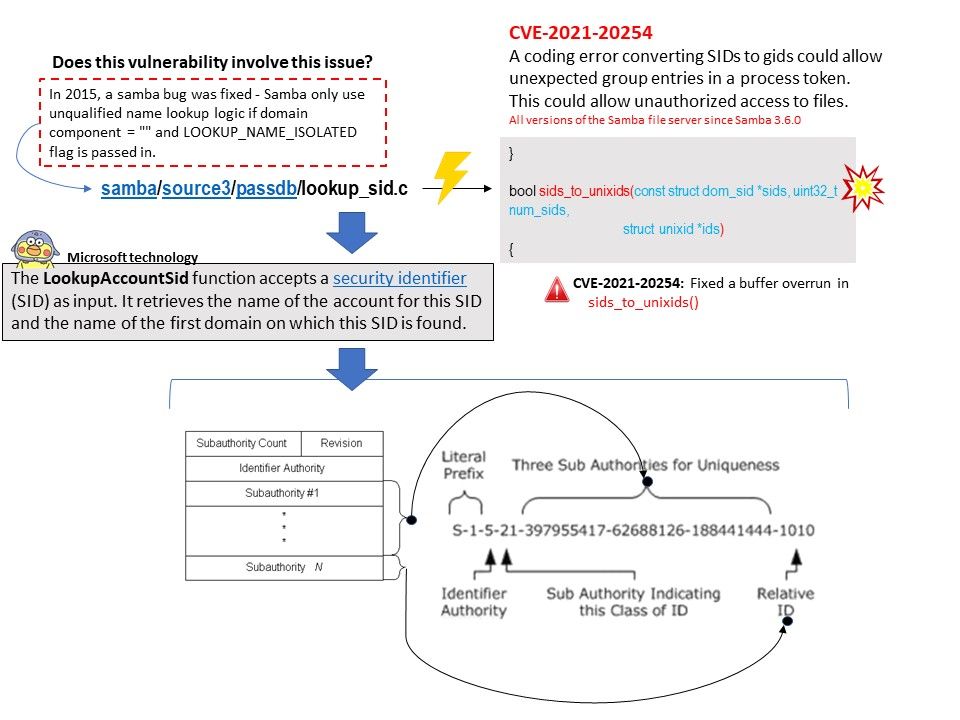
Vulnerability details: Citrix has released security updates to address a vulnerability in Citrix Workspace App for Windows. An attacker could exploit this vulnerability to take control of an affected system. This vulnerability affects all supported versions of Citrix Workspace app for Windows but does not affect Citrix Workspace app on any other platforms. Since vendor do not mentioned explicitly what is the actual flaw. However , whether does it encounter former design weakness again (Refer to diagram for details).
Official announcement: CTX307794 (Citrix Workspace App Security Update) – https://support.citrix.com/article/CTX307794
.jpg?width=1920&height=1080&fit=bounds)
.jpg)