Preface:
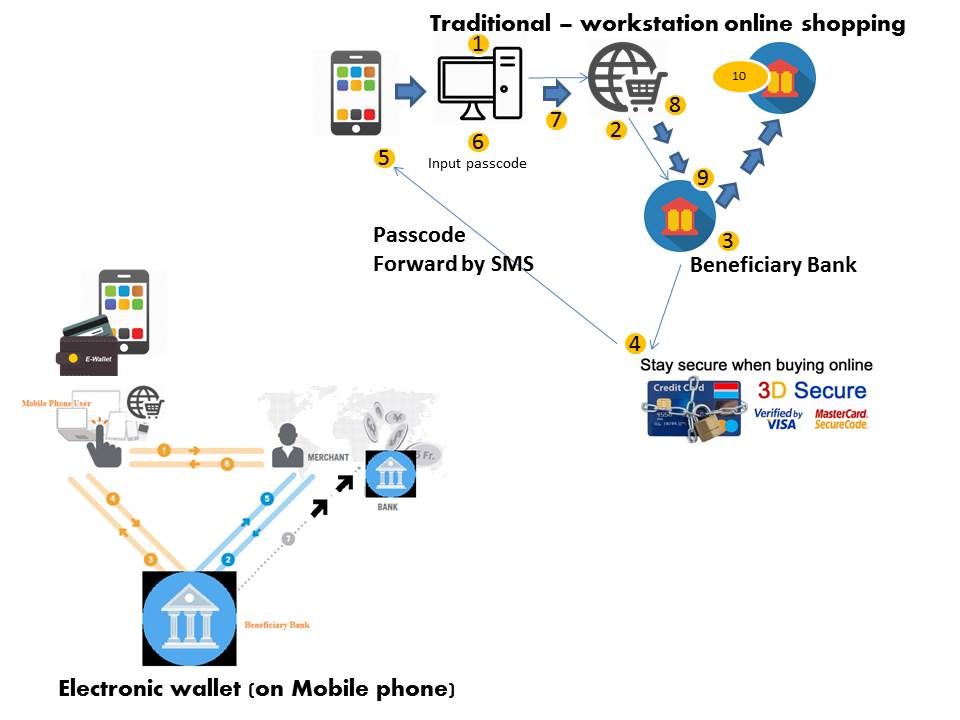
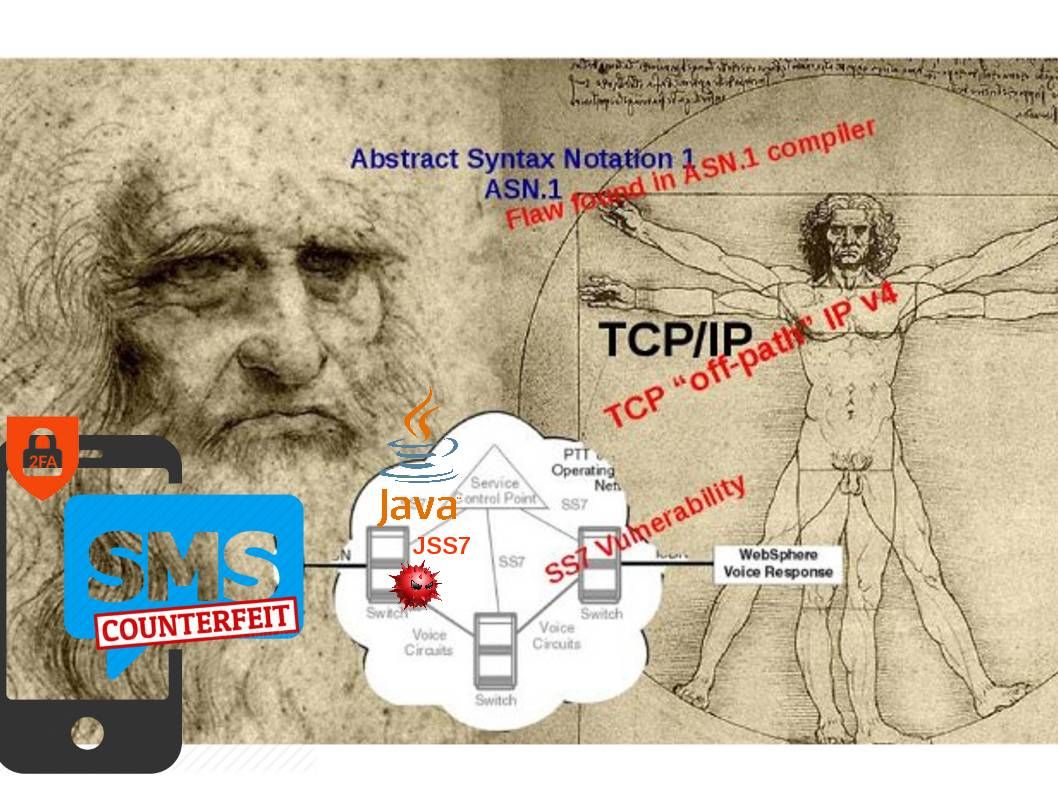
Two factor authentications claimed itself that it is a prefect security solution. No matter online banking transaction, Bitcoin wallet, e-trading business system and application system which concern the data privacy are willing to apply two factors authentication.
The overall comments for two factor authentication on the market
Let’s take a review in below cyber security incident records
- Cyber Criminals stolen Bitcoin in electronic Wallets by counterfeit two factor authentication SMS messages.A investment trader so called night owl. He was notified the passwords had been reset on two of his email addresses on 11th Aug 2016. He losses among the largest in his bitcoin investment. The venture capitalists (Bo Shen) he had value of US$300,000 electronic money (Augur REP tokens) stolen by hacker, plus an undisclosed amount of bitcoin and other cryptocurrencies lost. Coinbase (US base world biggest bitcoin exchange) observed that a double growth of cyber heist among it customers during November to December 2016.
- Criminals carried out an attack from a network of a foreign mobile network operator in the middle of January 2017. Meanwhile the attackers use SS7 vulnerability to intercept and redirect mTANs ( mobile transaction authentication numbers) sent by banks in Germany to authorize transfers payment out of victim accounts.
The clarification of two factor authentication criteria
Two factor authentication (2FA) definition is based on providing two of the following three “somethings”: (1) something you know, which is your username and password combination or a pin, (2) something you have, which can be a bank card, mobile device, smartwatch, or another device you’ve flagged as safe, and in more advanced scenarios, (3) something you are, which includes biometrics like fingerprints, retina scans, or voice recognition. By requiring a user to verify their identity with two or more of these unique ways, 2FA is effectively extending security beyond the password. The final step of the authentication process is send one-time authorization code to a device via an SMS, which you then enter to prove your identity.
My doubt on above matter?
What if my situation in regards to key terms “something you are” function replace by a hardware token. In this scenario, my hardware authentication token will be synchronized in the 1st round of registration to RSA ACE server. Thereafter the dependence of the hardware token depends on a element (timing). This setup compliance to 2FA definition. In the sense that it did not involve SMS message. So the 2FA still trustworthy, right?
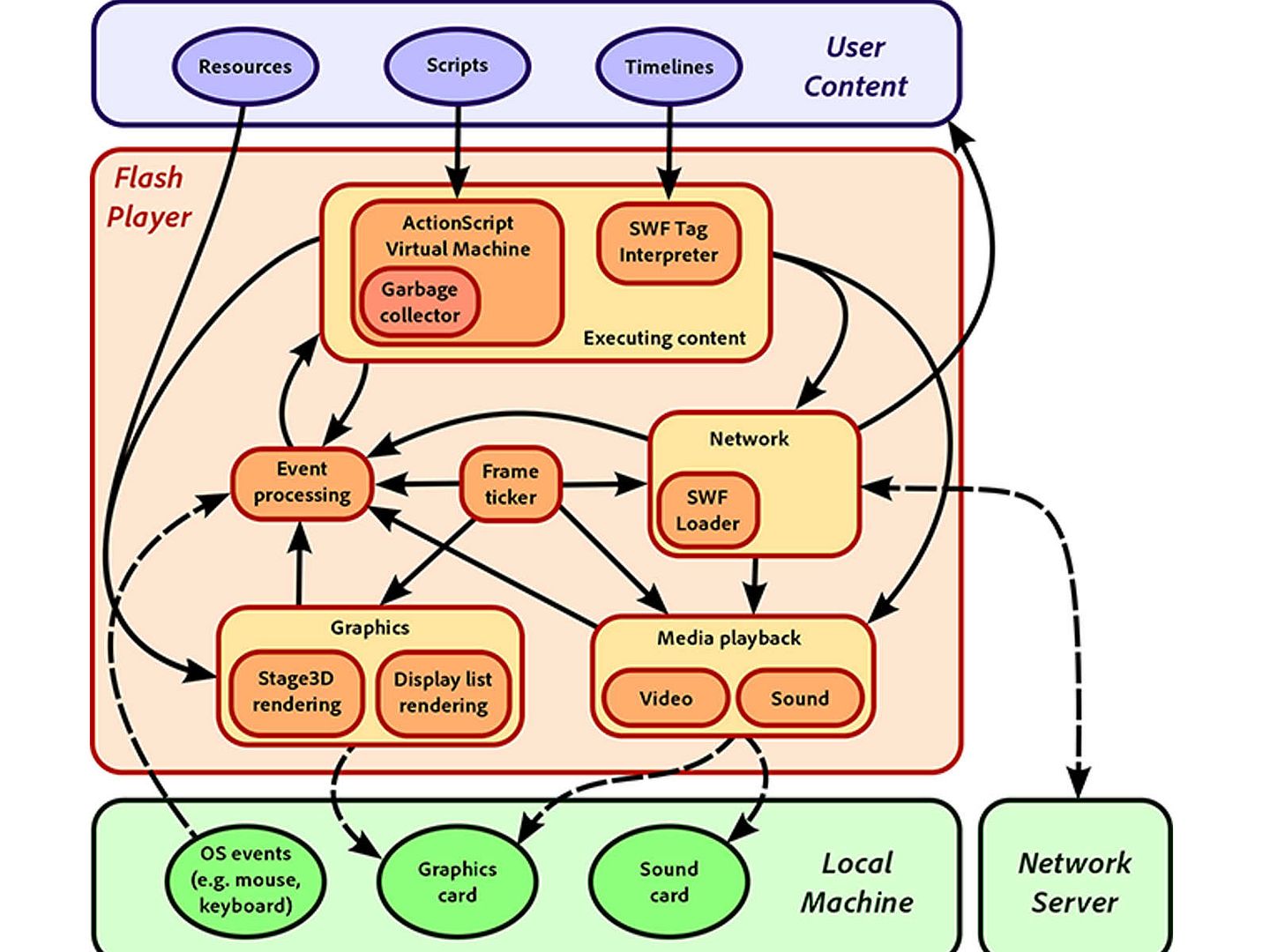
SS7 Vulnerability
A proof of concept shown that attacker could use the telephone network to access the voice data of a mobile phone, find its location and collect other information. Hacker able to manipulating USSD commands to spoof financial transactions such as the authorization of purchases or the transfer of funds between accounts.
The hacks exploit the SS7 vulnerability by tricking the telecom network believing the attacker’s phone has the same number as the victim’s phone. We know that hackers can hijack whatsApp and telegram via ss7. A vulnerability found on 2008.
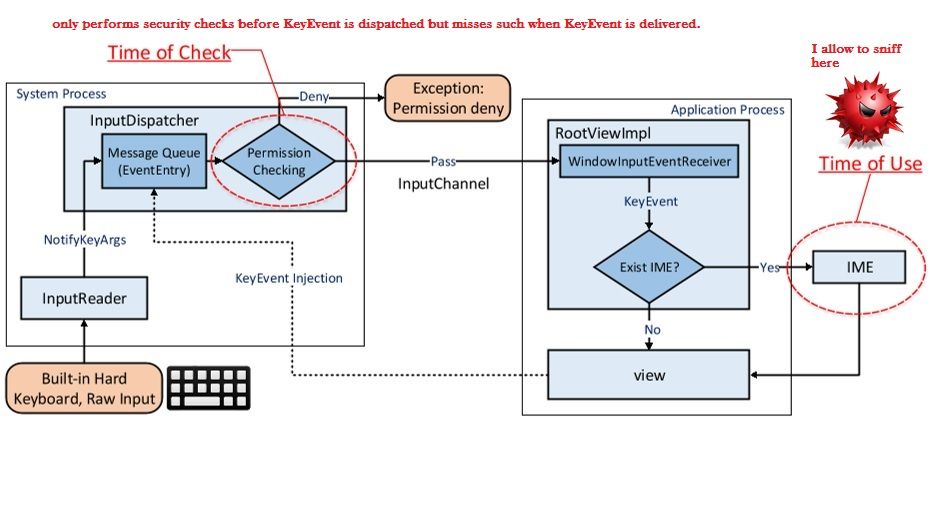
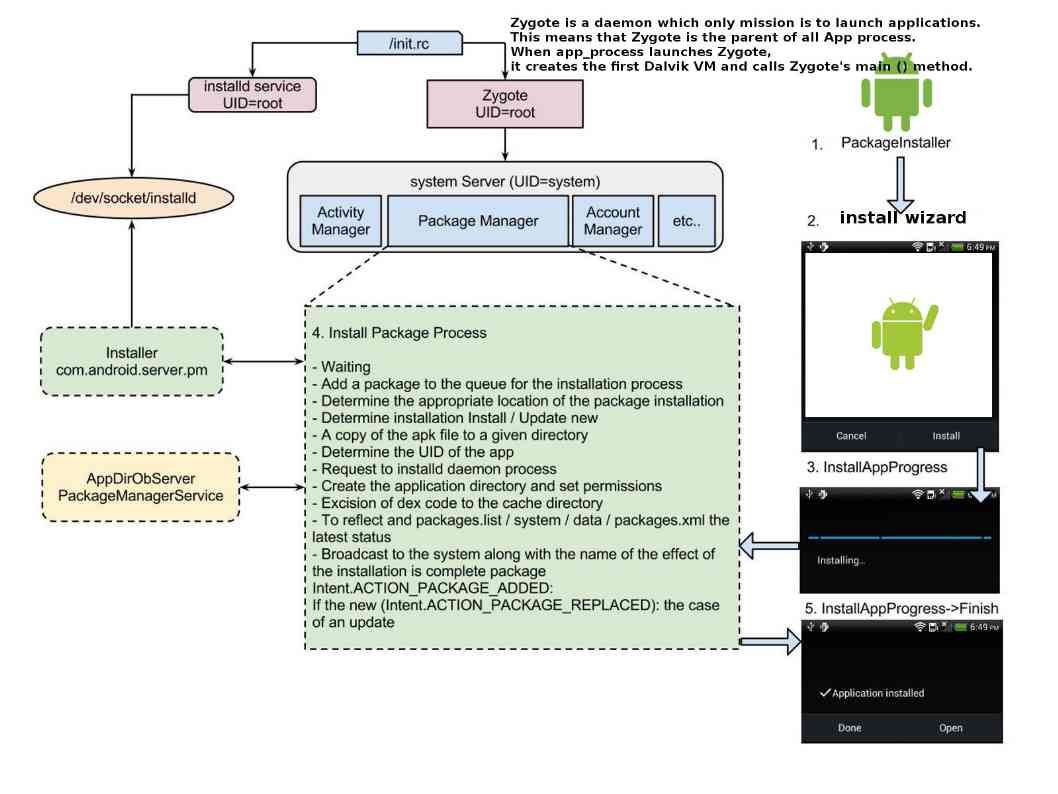
SS7 design fundamental is going to trust any request. We known that JSS7 is an implementation of SS7 telephony protocol in Java, aims to create an open source, multiplatform, SS7 protocol stack. And therefore counterfeit SMS message will more easier (see below information supplement 1 at the bottom of this page for reference). Carriers often “ask” one another for the whereabouts of a certain device so they can calculate the nearest cell tower to route a call. These sorts of automated interactions happen all the time. Nokia safeguards network operations with new security features in Sep 2015. The features consisting of Signaling Guard and Security Assessment service, detects and prevents attacks that exploit vulnerabilities in the SS7 protocol. It looks that such remediation step not effective to avoid insider threats.
Nokia safeguard network operation effectiveness
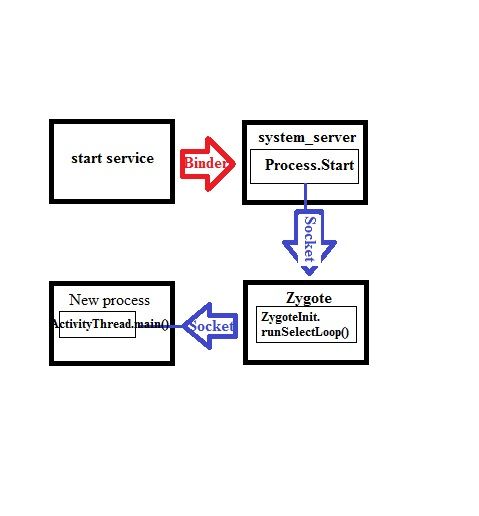
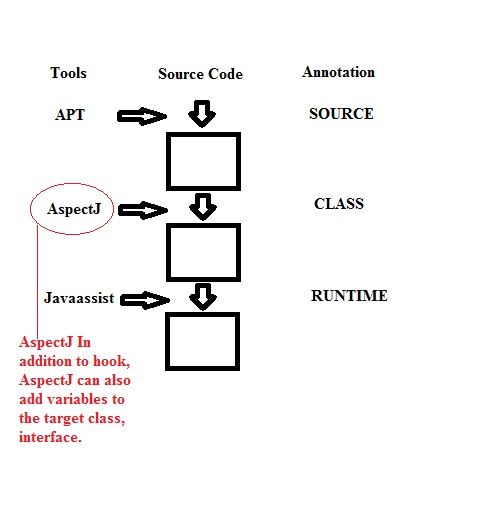
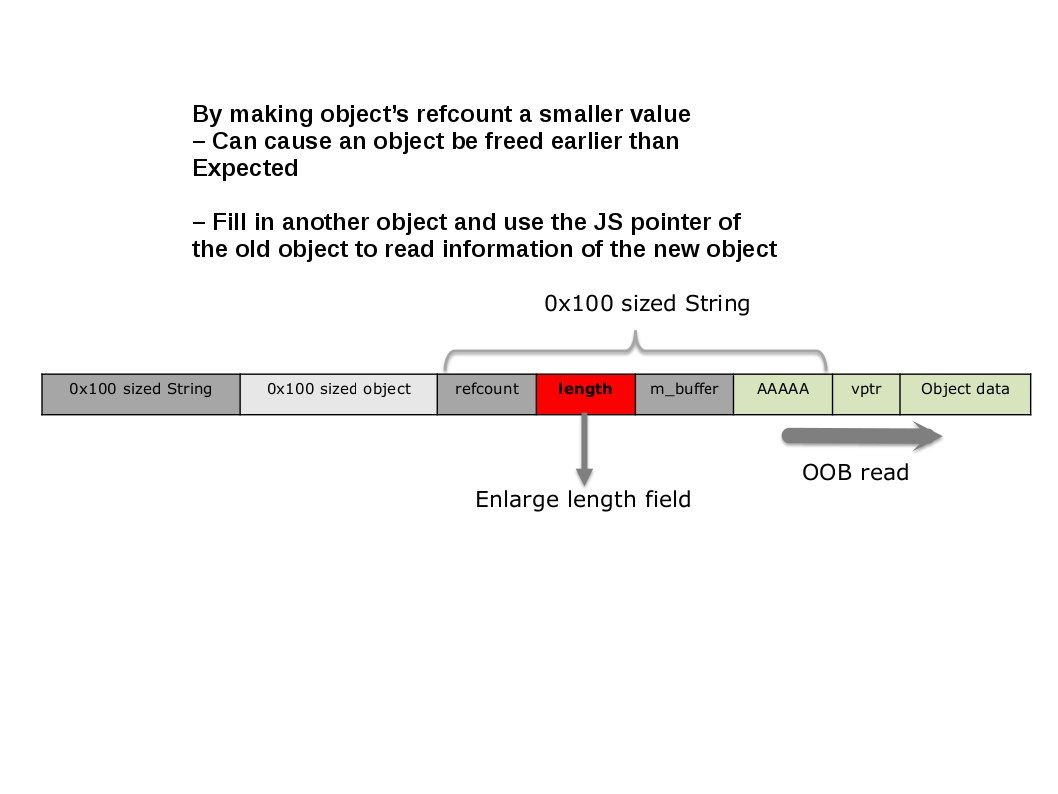
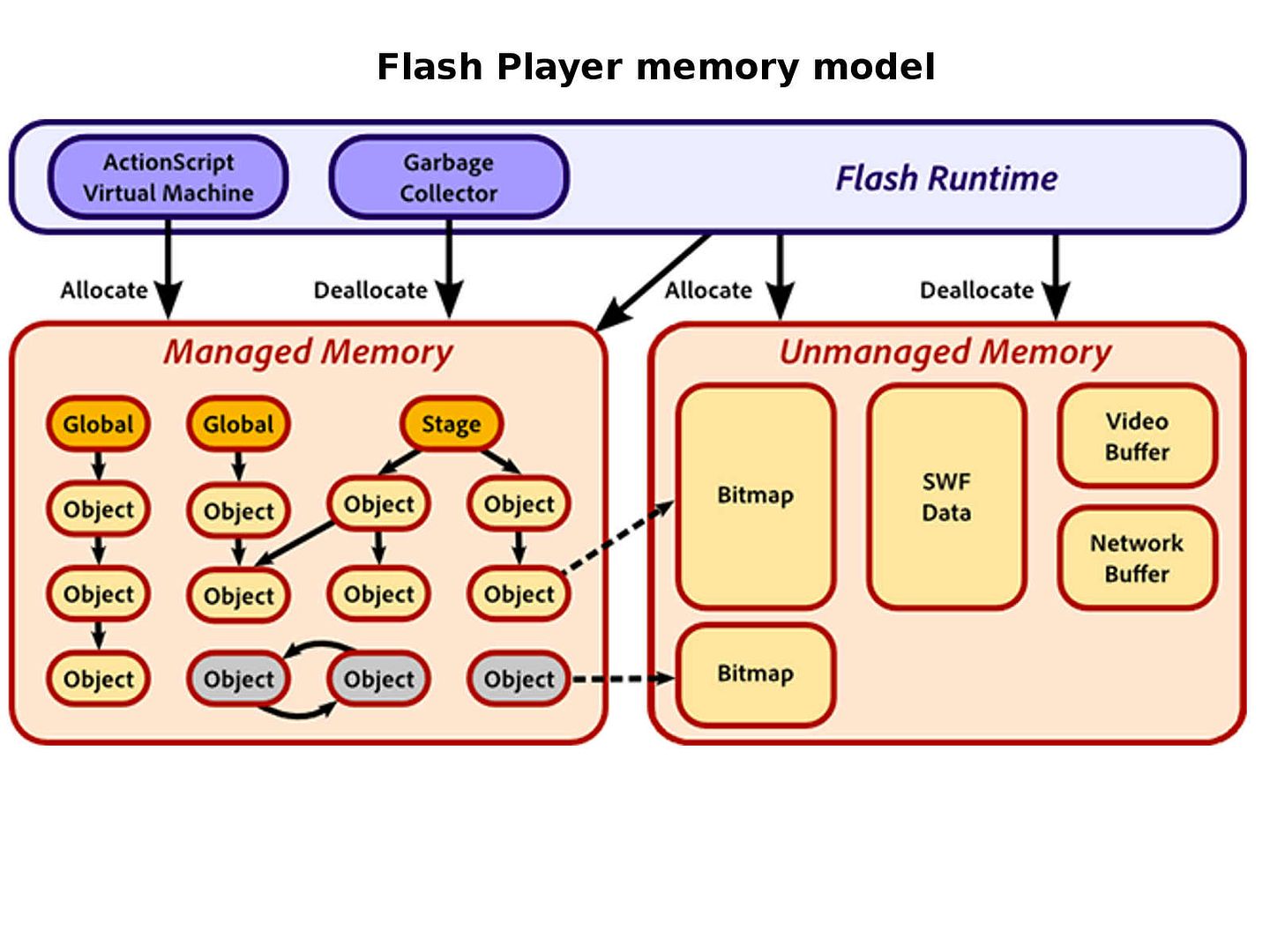
The fundamental of SS7 signal system is operate in a private network, meaning that cyber criminals have to hack it to gain entry—or find a telecom insider willing to offer illicit access.However there is another vulnerability on ASN.1. That is ASN.1 Compiler flaw leads to Network vulnerability. As such , hacker explore the back door on SS7 not only targeting to their internal staff. It might have possibility allow attackers to remotely execute unknown and unauthorized code inside the firmware of devices that use the compiled ASN1C code from within C and C++. Meanwhile java language fully compatible with SS7 protocol stack and platform. Oops! Do you think a design weakness will be happen in this place?
Hacker might reading shared memory data using Java . Program source that is written by C++.
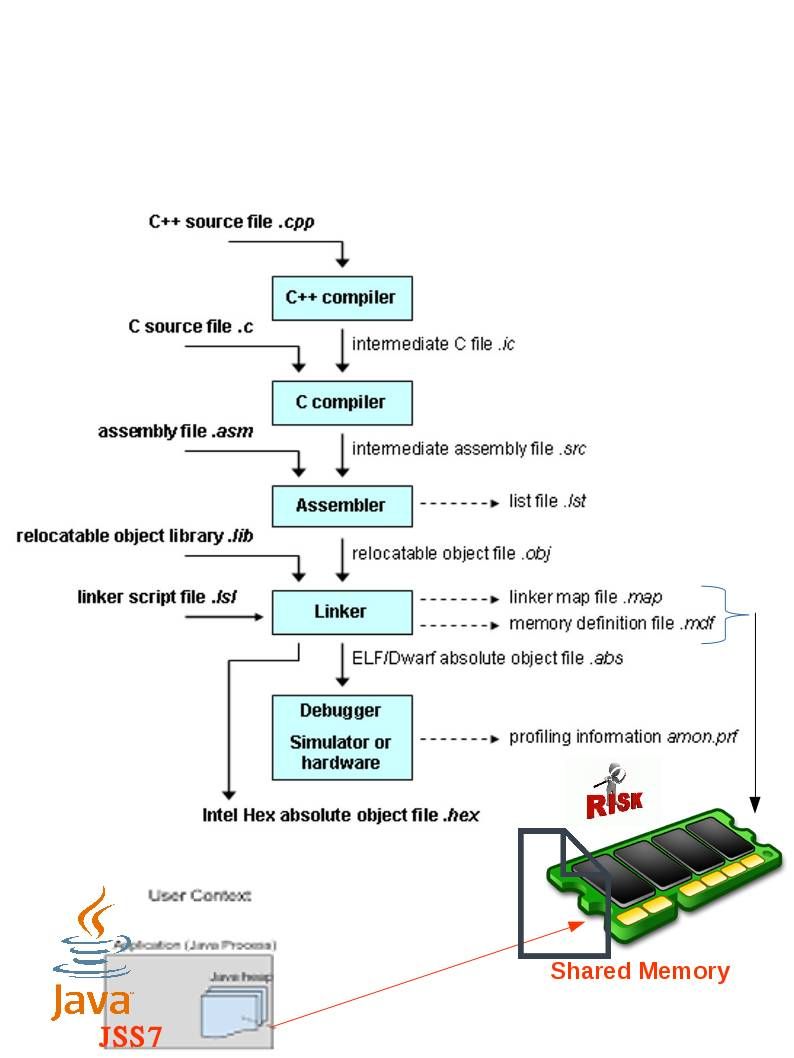
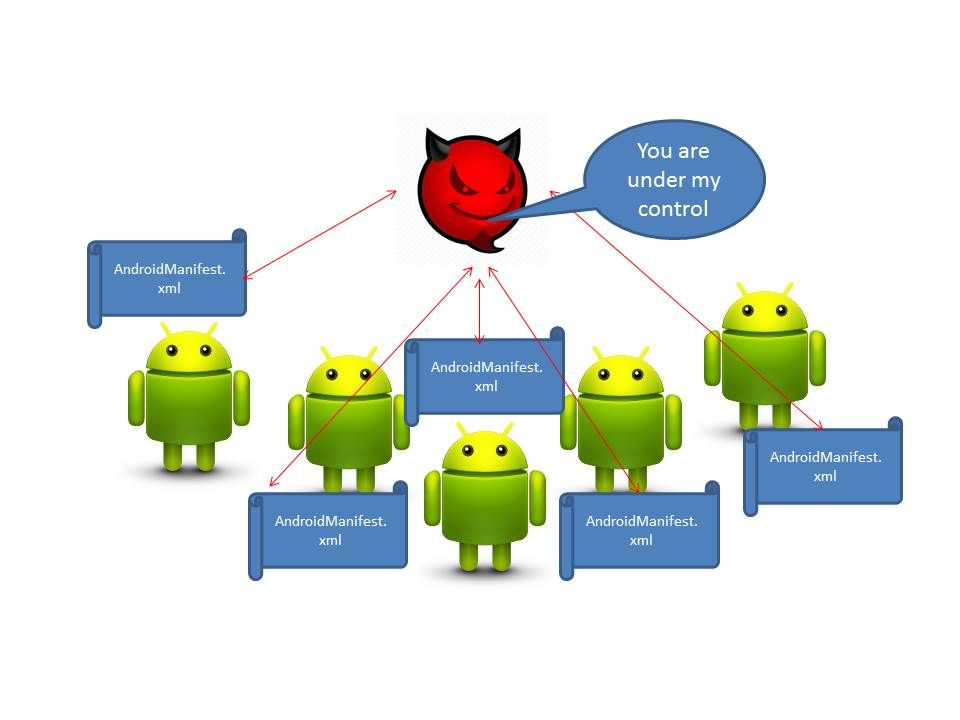
Hacker can create a method in Java to read or write on shared memory. Hacker might have way relies on Java SS7 benefits hook to sharing memory process. As a result, it compromise the machine. It can send SMS to anyone or anywhere includes communicate with other Telco vendor. It is the most concern and dangerous way.
Conclusion:
From technical point of view, 2FA (Two factor authentication) still a secure method for authentication. It looks that the flaw given by SS7 signaling system instead of 2FA itself. Since 2FA not limit to SS7 to conduct authentication. You are allow to use other alternative. Guys do not worry too much.
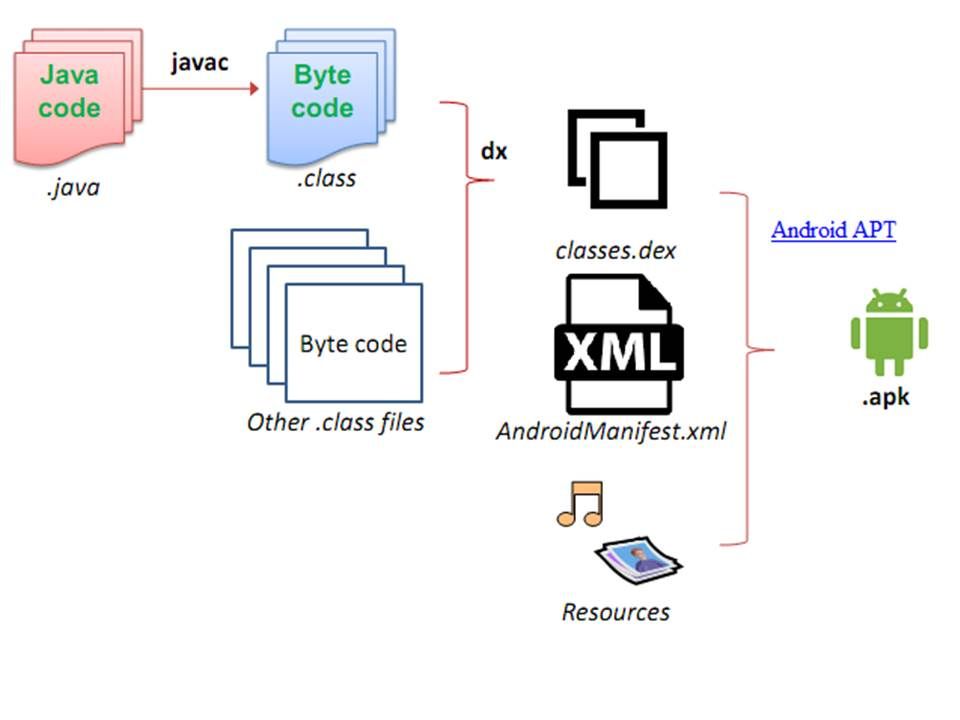
Information supplement 1: Open Source Java SS7 stack that allows Java apps to communicate with legacy SS7 communications equipment. JSS7 is an implementation of SS7 telephony protocol in Java, aims to create an open source, multiplatform, SS7 protocol stack. Below javascript sample is the pass along message implementation programming syntax for reference.
package org.mobicents.protocols.ss7.isup.impl.message;
import java.io.ByteArrayOutputStream;
import org.mobicents.protocols.ss7.isup.ISUPMessageFactory;
import org.mobicents.protocols.ss7.isup.ISUPParameterFactory;
import org.mobicents.protocols.ss7.isup.ParameterException;
import org.mobicents.protocols.ss7.isup.impl.message.parameter.MessageTypeImpl;
import org.mobicents.protocols.ss7.isup.message.ISUPMessage;
import org.mobicents.protocols.ss7.isup.message.PassAlongMessage;
import org.mobicents.protocols.ss7.isup.message.parameter.MessageName;
import org.mobicents.protocols.ss7.isup.message.parameter.MessageType;
/**
* Start time:xx<br>
* Project: xx<br>
*
* @author <a href="mailto:xx@xx.com">xx </a>
*/
public class PassAlongMessageImpl extends ISUPMessageImpl implements PassAlongMessage {
public static final MessageType _MESSAGE_TYPE = new MessageTypeImpl(MessageName.PassAlong);
static final int _INDEX_F_MessageType = 0;
private ISUPMessage embedded;
/**
*
* @param source
* @throws ParameterException
*/
public PassAlongMessageImpl() {
super.f_Parameters.put(_INDEX_F_MessageType, this.getMessageType());
}
public MessageType getMessageType() {
return _MESSAGE_TYPE;
}
@Override
public void setEmbeddedMessage(ISUPMessage msg) {
this.embedded = msg;
}
@Override
public ISUPMessage getEmbeddedMessage() {
return embedded;
}
public boolean hasAllMandatoryParameters() {
return this.embedded == null ? false: this.embedded.hasAllMandatoryParameters();
}
@Override
public int encode(ByteArrayOutputStream bos) throws ParameterException {
if(this.embedded!=null){
throw new ParameterException("No embedded message");
}
//encode CIC and message type
this.encodeMandatoryParameters(f_Parameters, bos);
final byte[] embeddedBody = ((AbstractISUPMessage)this.embedded).encode();
// 2 - for CIC
bos.write(embeddedBody, 2, embeddedBody.length - 2);
return bos.size();
}
@Override
public int decode(byte[] b, ISUPMessageFactory messageFactory,ISUPParameterFactory parameterFactory) throws ParameterException {
int index = 0;
//decode CIC and PAM message type.
index += this.decodeMandatoryParameters(parameterFactory, b, index);
byte targetMessageType = b[index];
this.embedded = messageFactory.createCommand(targetMessageType, this.getCircuitIdentificationCode().getCIC());
//create fake msg body
byte[] fakeBody = new byte[b.length-1];
System.arraycopy(b, 1, fakeBody, 0, fakeBody.length);
index+=((AbstractISUPMessage)this.embedded).decode(fakeBody, messageFactory, parameterFactory)-2;
return index;
}
// Not used, PAM contains body of another message. Since it overrides decode, those methods are not called.
protected void decodeMandatoryVariableBody(ISUPParameterFactory parameterFactory, byte[] parameterBody, int parameterIndex)
throws ParameterException {
// TODO Auto-generated method stub
}
protected void decodeOptionalBody(ISUPParameterFactory parameterFactory, byte[] parameterBody, byte parameterCode)
throws ParameterException {
// TODO Auto-generated method stub
}
protected int getNumberOfMandatoryVariableLengthParameters() {
// TODO Auto-generated method stub
return 0;
}
protected boolean optionalPartIsPossible() {
throw new UnsupportedOperationException();
}
}
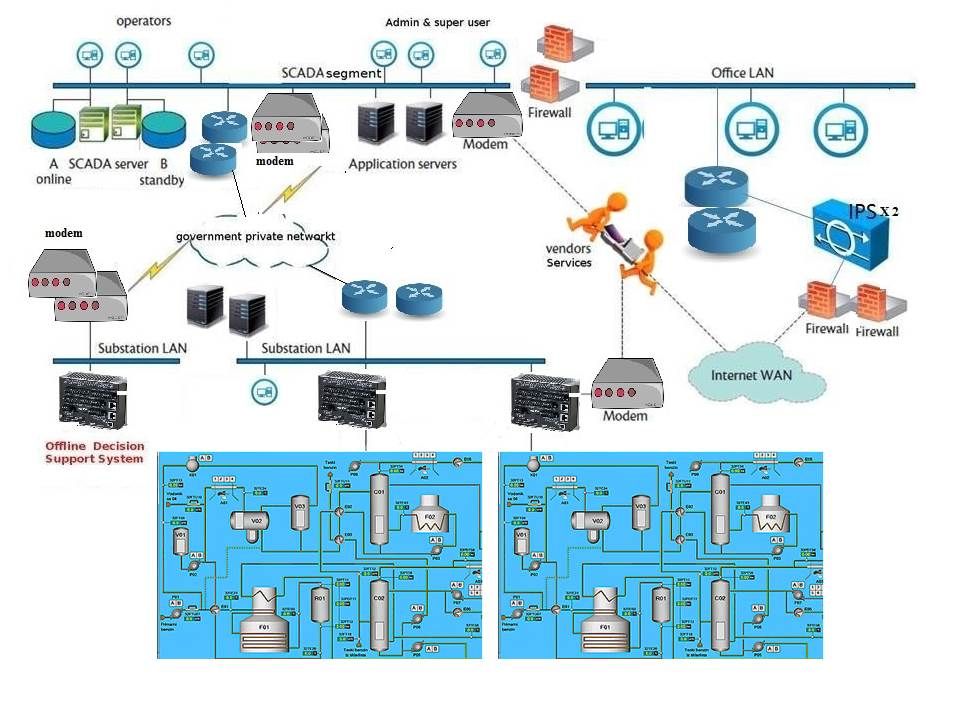
Information supplement 2: How to protect your IT premises? Found vulnerability sometimes isn’t a flaw.This is the original design! For more detail, please refer below: