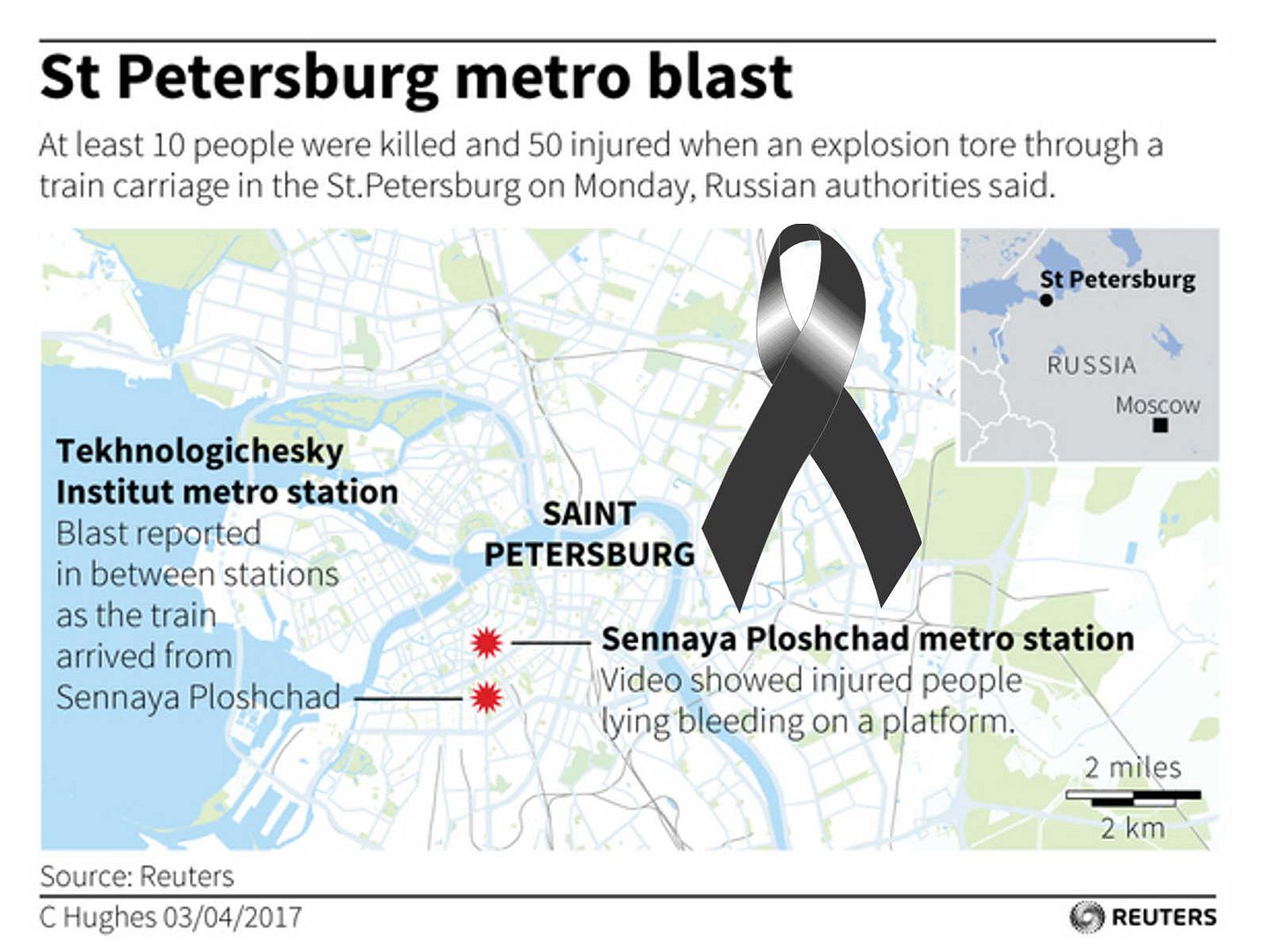
A moment of silence, prayer for the dead (Terrorist attack on the streets attack near U.K. Parliament 22nd Mar 2017)

A moment of silence, prayer for the dead Tragedy in Russia - Explosion in the St. Petersburg metro 3rd Apr 2017
Part 2: Blockchain technology situation – Malware join to bitcoin mining
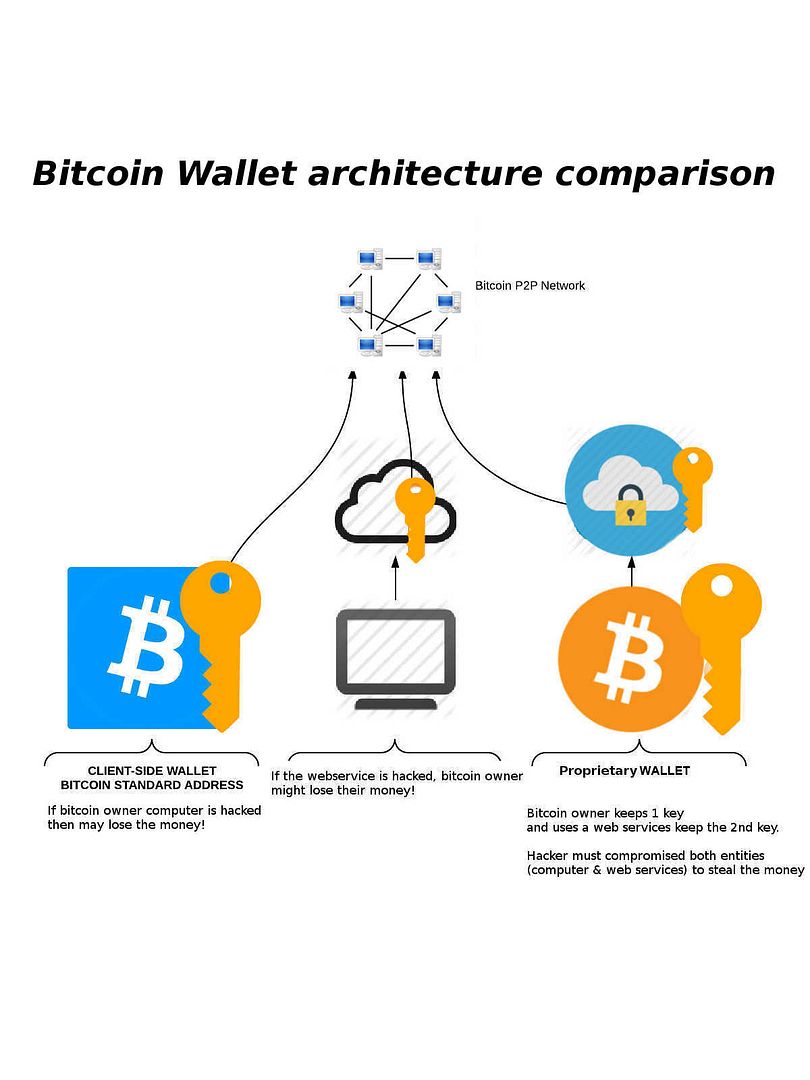
We continuous the discussion topic on blockchain technology situation. Part 1:Blockchain technology situation – A Tales of Two Cities The discussion on part 2 mainly focus on malware threats to bitcoin industry. We understand that Bitcoin was designed to be uncensorable digital cash that could operate outside the existing financial system. As mentioned last time, it looks that the blockchain technology contained weakness on end point device (bitcoin owner workstation or mobile phone). Even though you deploy a proprietary wallet, the overall setup will become weakness once malware compromise your end point device. Below picture diagram bring an idea to reader of bitcoin wallet architecture, see whether you have different idea in this regard?
Bitfinex incident wakes up concern on endpoint security
More than US$60m worth of bitcoin was stolen from one of the world’s largest digital currency exchanges (Bitfinex) on 2nd Aug 2017. Nearly 120,000 units of digital currency bitcoin worth about US$72 million was stolen from the exchange platform Bitfinex in Hong Kong, said Reuters Technology News. Director of Community & Product Development for Bitfinex stated that the bitcoin was stolen from users’ segregated wallets. The investigation has found no evidence of a breach to any BitGo servers, said the representative of BitGo.
Since no evidence proof that security breach happened in that place but what is the possible cause?
An announcement posted by official group (Bitfinex), the company informed that there are going to secure the environment and bring down the web site and the maintenance page will be left up. From technical point of view, if API and signing keys reside on servers. Hacker might have access with legitemate credential once a bitcoin wallet user workstation compromised.As a matter of fact if the webservice is hacked, bitcoin owner will lost the money (see above bitcoin wallet architecture comparison diagram for reference).
Our Observation
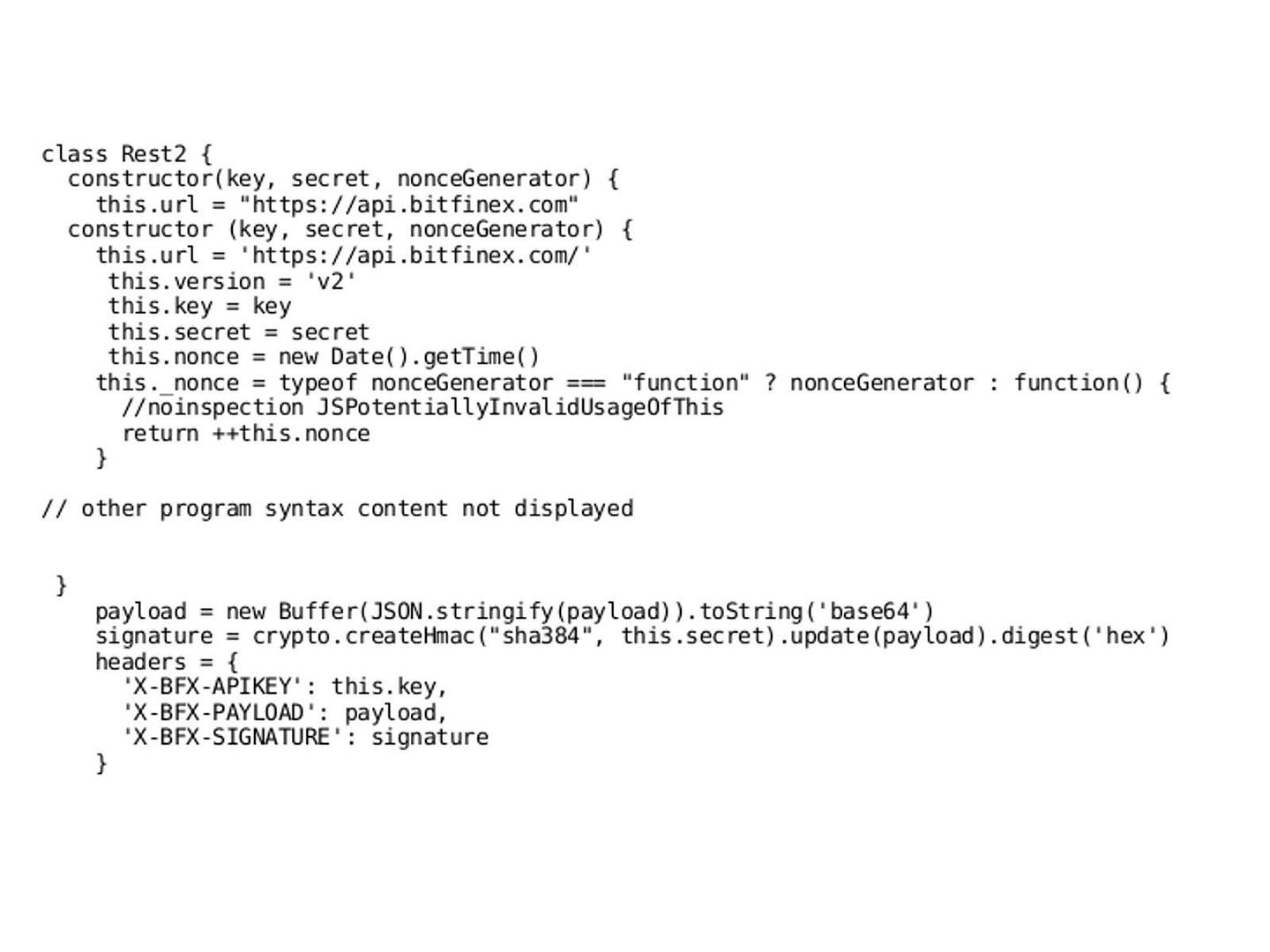
The weakness of Node.J.S trading API Framework.
The java script contain security weakness. It benefits hacker to understand the operation path. For instance
Client send his payload, his key, and the hmac of his payload with his secret key. Server retrieve user with his pk, recompute the hmac with the retrieved sk and then check if the computed hmac is equal to the retrieved hmac. (see below program syntax for reference).
From technical point of view, malware which contains steal private key or digital certificate function, they have capability transform to bitcoin malware. As usual, the infection technique relies on Spear phishing. The emails contained a malicious attachment with the file which contained a zero-day exploit. The exploit attacked multimedia software platform used for production of animations especially Adobe Flash to install a malware onto the victim’s computer.
Then malware obtained bitfinex private key and one of the following item.
i) bitgo’s private key
ii) bitfinex bitgo’s username and password and authy’s credentials (that allows the hacker to create new api access tokens and remove daily limits)
iii) bitfinex bitgo’s api access token
Or apply new keys gave to bitgo as new 2-3 internal bitfinex address. signed tx with bfx key, and “new key” that was just given. Meanwhile bypassing bitgo’s security checks.
Summary:
Above information detail is one of the example. It looks that quote a real incident can increase the visibility of the understanding. Apart from that, discussion looks never ending. I believed that part 3 will be coming soon.
You can certainly see your enthusiasm within the work you write. The sector hopes for more passionate writers such as you who are not afraid to mention how they believe. All the time follow your heart.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how could we communicate?
Im thankful for the blog.Really looking forward to read more. Really Great.
Oh my goodness! Amazing article dude! Thank you so much, However I am experiencing issues with your RSS. I don’t understand the reason why I can’t join it. Is there anybody else having the same RSS problems? Anybody who knows the solution can you kindly respond? Thanx!!
It’sIt is in point of factactuallyreallyin realitytruly a nicegreat and helpfuluseful piece of informationinfo. I’mI am satisfiedgladhappy that youthat you simplythat you just shared this helpfuluseful infoinformation with us. Please staykeep us informedup to date like this. ThanksThank you for sharing.
Hi, I do believe this is a great web site. I stumbledupon it 😉 I may come back yet again since I book marked it. Money and freedom is the best way to change, may you be rich and continue to guide others.
What i don’t realize is in reality how you’re not really a lot more well-preferred than you might be now. You are so intelligent. You realize thus considerably in relation to this subject, made me in my opinion imagine it from a lot of varied angles. Its like men and women don’t seem to be involved until it’s something to accomplish with Girl gaga! Your personal stuffs nice. Always deal with it up!
Thanks for helping out, wonderful info. “Courage comes and goes. Hold on for the next supply.” by Vicki Baum.
Thanks, I’ve recently been searching for information about this topic for ages and yours is the best I’ve discovered till now. However, what in regards to the conclusion? Are you sure about the source?
Only wanna input on few general things, The website style is perfect, the articles is real excellent : D.
Very nice post. I just stumbled upon your blog and wanted to say that I have truly enjoyed surfing around your blog posts. After all I will be subscribing to your rss feed and I hope you write again very soon!
I dugg some of you post as I cogitated they were very beneficial very beneficial
I am always looking online for ideas that can benefit me. Thx!
I simply couldn’t leave your site before suggesting that I really loved the usual information a person provide for your guests? Is gonna be back often to check up on new posts.
hi!,I like your writing very a lot! percentage we keep in touch more approximately your post on AOL? I require a specialist on this house to solve my problem. May be that is you! Looking ahead to see you.
magnificent publish, very informative. I wonder why the opposite experts of this sector do not realize this. You must continue your writing. I am sure, you’ve a great readers’ base already!
I like this web site very much, Its a very nice berth to read and incur information. “‘Taint’t worthwhile to wear a day all out before it comes.” by Sarah Orne Jewett.
Hello there, I discovered your web site by way of Google at the same time as looking for a comparable topic, your web site came up, it appears good. I’ve bookmarked it in my google bookmarks.
I really wanted to type a quick note to say thanks to you for those great techniques you are giving at this website. My long internet look up has at the end been paid with excellent strategies to go over with my family. I ‘d suppose that we website visitors are very lucky to be in a perfect place with so many awesome professionals with great methods. I feel extremely happy to have come across your web pages and look forward to really more pleasurable times reading here. Thanks a lot once more for a lot of things.
I got what you intend, thanks for putting up.Woh I am happy to find this website through google. “Money is the most egalitarian force in society. It confers power on whoever holds it.” by Roger Starr.
Dead composed articles, thanks for entropy. “Life is God’s novel. Let him write it.” by Isaac Bashevis Singer.
I really like reading an article that can make people think. Also, thanks for allowing for me to comment!
Hiya, I’m really glad I’ve found this information. Nowadays bloggers publish just about gossips and web and this is really irritating. A good blog with exciting content, that’s what I need. Thanks for keeping this site, I will be visiting it. Do you do newsletters? Cant find it.
This is the right website for anyone who hopes to understand this topic. You realize a whole lot its almost hard to argue with you (not that I actually will need to…HaHa). You definitely put a fresh spin on a subject that has been written about for years. Great stuff, just great!
My wife and i ended up being lucky when Raymond could round up his researching through the precious recommendations he was given in your web page. It’s not at all simplistic just to choose to be making a gift of hints that many other people have been making money from. And now we fully grasp we have got the writer to be grateful to for this. The most important explanations you made, the easy blog navigation, the friendships you will help to engender – it is everything impressive, and it’s really helping our son and our family know that that concept is cool, and that is extraordinarily fundamental. Thank you for the whole thing!
I like what you guys are up also. Such intelligent work and reporting! Keep up the superb works guys I’ve incorporated you guys to my blogroll. I think it’ll improve the value of my web site :).
Regards for helping out, good information. “The laws of probability, so true in general, so fallacious in particular.” by Edward Gibbon.
Excellent goods from you, man. I’ve understand your stuff previous to and you are just too great. I actually like what you have acquired here, really like what you’re stating and the way in which you say it. You make it entertaining and you still take care of to keep it wise. I can’t wait to read far more from you. This is actually a tremendous site.
Simply wish to say your article is as surprising. The clearness in your post is just spectacular and i could assume you are an expert on this subject. Fine with your permission let me to grab your RSS feed to keep up to date with forthcoming post. Thanks a million and please carry on the gratifying work.
I think this is one of the most important info for me. And i am glad reading your article. But should remark on some general things, The website style is great, the articles is really excellent : D. Good job, cheers
Say, you got a nice blog article. Awesome.
Excellent write-up. I absolutely appreciate this site. Thanks!
What i don’t realize is if truth be told how you are not actually much more smartly-preferred than you might be right now. You’re very intelligent. You realize thus considerably when it comes to this matter, made me in my opinion consider it from so many various angles. Its like women and men don’t seem to be fascinated until it is one thing to do with Woman gaga! Your own stuffs outstanding. At all times take care of it up!
Greetings! Very helpful advice within this article! It is the little changes that produce the greatest changes. Many thanks for sharing!
I like what you guys are up also. Such clever work and reporting! Carry on the excellent works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
I don’t even know how I ended up here, but I thought this post was great. I don’t know who you are but definitely you are going to a famous blogger if you are not already 😉 Cheers!
Way cool! Some very valid points! I appreciate you penning this article and also the rest of the site is really good.
Hello There. I found your blog using msn. This is a very well written article. I’ll be sure to bookmark it and come back to read more of your useful info. Thanks for the post. I will definitely return.
I like what you guys are up also. Such smart work and reporting! Keep up the excellent works guys I’ve incorporated you guys to my blogroll. I think it will improve the value of my site :).
I simply needed to appreciate you yet again. I’m not certain what I might have done in the absence of the entire thoughts provided by you about this area of interest. It has been a distressing difficulty for me, nevertheless witnessing a new skilled way you processed the issue took me to cry over happiness. Extremely happy for this service and even wish you are aware of a great job you happen to be accomplishing teaching most people with the aid of your site. I am sure you’ve never got to know all of us.
Just wish to say your article is as astonishing. The clearness in your post is just excellent and i can assume you are an expert on this subject. Well with your permission let me to grab your feed to keep up to date with forthcoming post. Thanks a million and please keep up the rewarding work.
Someone essentially lend a hand to make severely posts I might state. This is the first time I frequented your web page and so far? I amazed with the research you made to make this particular publish extraordinary. Great job!
I like this site so much, saved to my bookmarks. “Nostalgia isn’t what it used to be.” by Peter De Vries.
Some really nice and utilitarian information on this website, besides I think the layout holds great features.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research on this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such excellent info being shared freely out there.
Hello. magnificent job. I did not anticipate this. This is a excellent story. Thanks!
Pretty section of content. I just stumbled upon your blog and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Anyway I will be subscribing to your augment and even I achievement you access consistently fast.
Hello, i think that i saw you visited my site so i came to “return the favor”.I am trying to find things to improve my web site!I suppose its ok to use a few of your ideas!!
hello!,I really like your writing so much! percentage we keep in touch more approximately your post on AOL? I require a specialist in this area to unravel my problem. May be that is you! Having a look forward to see you.
I actually wanted to write a comment to be able to thank you for these pleasant solutions you are placing on this website. My rather long internet investigation has at the end been compensated with beneficial insight to exchange with my friends and classmates. I would admit that many of us readers are quite fortunate to live in a really good site with very many awesome individuals with beneficial opinions. I feel truly fortunate to have come across your weblog and look forward to some more awesome minutes reading here. Thanks a lot once again for all the details.
As a Newbie, I am always browsing online for articles that can aid me. Thank you
My husband and i ended up being quite satisfied that Chris could finish off his preliminary research out of the ideas he had out of your weblog. It is now and again perplexing to simply happen to be handing out helpful tips people have been trying to sell. We really fully grasp we now have the blog owner to be grateful to because of that. The specific explanations you made, the straightforward site menu, the relationships your site aid to create – it’s got everything overwhelming, and it’s aiding our son in addition to the family consider that this issue is excellent, which is certainly extremely mandatory. Many thanks for all!
My brother recommended I might like this blog. He was entirely right. This post truly made my day. You can not imagine just how much time I had spent for this info! Thanks!
Wow! This could be one particular of the most beneficial blogs We have ever arrive across on this subject. Basically Fantastic. I’m also an expert in this topic so I can understand your hard work.
I savor, lead to I discovered exactly what I was taking a look for. You have ended my 4 day lengthy hunt! God Bless you man. Have a great day. Bye
Hi there, You’ve done an incredible job. I’ll certainly digg it and personally suggest to my friends. I’m sure they will be benefited from this website.
Hi, Neat post. There is an issue along with your website in internet explorer, could test this… IE still is the market chief and a good portion of folks will pass over your great writing because of this problem.
Dead pent subject material, Really enjoyed studying.
hey there and thank you for your information – I’ve definitely picked up anything new from right here. I did however expertise some technical points using this site, since I experienced to reload the site many times previous to I could get it to load properly. I had been wondering if your web hosting is OK? Not that I am complaining, but sluggish loading instances times will often affect your placement in google and can damage your high-quality score if ads and marketing with Adwords. Anyway I am adding this RSS to my e-mail and can look out for much more of your respective intriguing content. Make sure you update this again very soon..
Heya i’m for the first time here. I found this board and I find It really useful & it helped me out a lot. I hope to give something back and help others like you helped me.
I am continuously invstigating online for articles that can assist me. Thank you!
Definitely, what a great site and educative posts, I definitely will bookmark your blog.Best Regards!
Hello. fantastic job. I did not expect this. This is a remarkable story. Thanks!
Awsome article and right to the point. I don’t know if this is really the best place to ask but do you folks have any ideea where to get some professional writers? Thx 🙂
I will right away grab your rss feed as I can’t find your e-mail subscription link or e-newsletter service. Do you’ve any? Please let me recognise in order that I may subscribe. Thanks.
I got what you mean , thanks for posting .Woh I am pleased to find this website through google. “You must pray that the way be long, full of adventures and experiences.” by Constantine Peter Cavafy.
You have noted very interesting details ! ps nice site. “Recompense injury with justice, and recompense kindness with kindness.” by Confucius.
naturally like your web-site however you need to check the spelling on quite a few of your posts. Many of them are rife with spelling issues and I in finding it very bothersome to tell the truth then again I will certainly come again again.
I love the efforts you have put in this, thanks for all the great articles.
Wow! This can be one particular of the most useful blogs We have ever arrive across on this subject. Actually Great. I am also an expert in this topic so I can understand your hard work.
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out much. I hope to give something back and aid others like you aided me.
Some truly prime articles on this site, bookmarked .
I am also commenting to make you know what a really good discovery my princess found reading through your site. She mastered a wide variety of details, most notably what it’s like to possess a marvelous giving heart to let a number of people completely understand a variety of multifaceted subject matter. You truly did more than our own desires. Thanks for producing those essential, trusted, informative and as well as easy thoughts on your topic to Emily.
It’s actually a nice and helpful piece of information. I am happy that you just shared this helpful info with us. Please keep us informed like this. Thank you for sharing.
I really appreciate this post. I¡¦ve been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again
Merely a smiling visitor here to share the love (:, btw outstanding layout. “Reading well is one of the great pleasures that solitude can afford you.” by Harold Bloom.
I have been browsing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. Personally, if all site owners and bloggers made good content as you did, the net will be much more useful than ever before.
I precisely wanted to thank you very much once again. I do not know the things I would have handled in the absence of the actual ways contributed by you directly on that area of interest. It was actually the hard concern in my position, nevertheless considering your professional way you resolved that made me to leap with contentment. Now i’m thankful for your service and even sincerely hope you comprehend what a powerful job your are providing instructing many others thru a site. I am certain you haven’t come across any of us.
Nice blog right here! Also your website lots up very fast! What host are you using? Can I get your affiliate hyperlink for your host? I want my web site loaded up as quickly as yours lol
Whats Happening i’m new to this, I stumbled upon this I have discovered It positively useful and it has aided me out loads. I hope to give a contribution & assist different customers like its aided me. Great job.
I like the helpful info you provide on your articles. I’ll bookmark your blog and check once more right here frequently. I’m somewhat certain I will be informed many new stuff right here! Good luck for the next!
Hey just wanted to give you a quick heads up. The words in your article seem to be running off the screen in Ie. I’m not sure if this is a format issue or something to do with web browser compatibility but I figured I’d post to let you know. The layout look great though! Hope you get the problem solved soon. Thanks
Do you have a spam problem on this blog; I also am a blogger, and I was wanting to know your situation; we have developed some nice practices and we are looking to trade techniques with others, why not shoot me an email if interested.
I and my friends have been examining the excellent tips and hints located on the blog and so instantly I had a terrible suspicion I had not thanked the blog owner for them. Most of the ladies appeared to be for that reason excited to see all of them and already have pretty much been tapping into those things. Many thanks for getting so kind and for making a choice on this sort of very good ideas millions of individuals are really wanting to understand about. My very own sincere apologies for not expressing appreciation to you sooner.
I keep listening to the news update lecture about getting boundless online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i get some?
Usually I don’t learn post on blogs, however I wish to say that this write-up very compelled me to check out and do it! Your writing taste has been surprised me. Thanks, very great article.
This is very interesting, You are a very skilled blogger. I have joined your feed and look forward to seeking more of your excellent post. Also, I have shared your web site in my social networks!
One more issue is that video gaming became one of the all-time main forms of fun for people spanning various ages. Kids participate in video games, and also adults do, too. The particular XBox 360 is amongst the favorite gaming systems for individuals that love to have hundreds of video games available to them, as well as who like to experiment with live with other people all over the world. Many thanks for sharing your notions.
Thanks for the new stuff you have exposed in your post. One thing I want to discuss is that FSBO relationships are built after a while. By introducing yourself to owners the first weekend their FSBO can be announced, prior to masses get started calling on Wednesday, you generate a good link. By giving them equipment, educational supplies, free accounts, and forms, you become a strong ally. By taking a personal desire for them as well as their circumstances, you develop a solid interconnection that, most of the time, pays off if the owners opt with a real estate agent they know along with trust – preferably you actually.
The things i have often told people is that when you are evaluating a good online electronics shop, there are a few aspects that you have to factor in. First and foremost, you would like to make sure to find a reputable and reliable retail store that has received great assessments and classification from other customers and business sector experts. This will ensure that you are handling a well-known store that can offer good assistance and aid to their patrons. Thanks for sharing your opinions on this web site.
I simply want to say I’m beginner to weblog and definitely savored this web-site. Probably I’m planning to bookmark your blog . You really have beneficial stories. Regards for revealing your website page.
I am so grateful for your article post. Great.
Hello my friend! I want to say that this post is awesome, nice written and come with approximately all vital infos. I¡¦d like to see extra posts like this .
I am continually searching online for posts that can help me. Thanks!
It’s a shame you don’t have a donate button! I’d without a doubt donate to this superb blog! I suppose for now i’ll settle for book-marking and adding your RSS feed to my Google account. I look forward to new updates and will share this site with my Facebook group. Chat soon!
I value the blog post.Thanks Again. Great.
I like what you guys are up too. Such clever work and reporting! Keep up the excellent works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my site 🙂
Really appreciate you sharing this article.Really thank you! Will read on…
Really appreciate you sharing this article.Much thanks again. Will read on…
You truly did more than visitors’ expectations. Thank you for rendering these helpful, trusted, edifying and also cool thoughts on the topic to Kate.
Valuable information. Fortunate me I discovered your web site by accident, and I am stunned why this accident didn’t took place in advance! I bookmarked it.
Great, thanks for sharing this blog article.Much thanks again. Cool.
Wow, marvelous blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your website is wonderful, as well as the content!
Major thankies for the blog article.Really looking forward to read more. Keep writing.
Hey, thanks for the article.Really looking forward to read more.
Valuable info. Fortunate me I discovered your website unintentionally, and I am stunned why this twist of fate did not took place earlier! I bookmarked it.
obviously like your website but you need to test the spelling on several of your posts. Many of them are rife with spelling issues and I find it very troublesome to tell the reality then again I will definitely come back again.
My husband and i were contented that Peter managed to carry out his investigations from the ideas he discovered from your own web pages. It is now and again perplexing to simply find yourself offering instructions that many a number of people may have been making money from. We acknowledge we’ve got the website owner to be grateful to for that. All of the explanations you’ve made, the straightforward website menu, the relationships you make it easier to create – it’s got everything astounding, and it’s aiding our son and us consider that the matter is exciting, which is certainly pretty essential. Thank you for the whole lot!
Hello, Neat post. There is an issue with your website in internet explorer, could check this¡K IE nonetheless is the marketplace chief and a big component to people will omit your excellent writing because of this problem.
I have been surfing online more than 3 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all webmasters and bloggers made good content as you did, the web will be much more useful than ever before.
I appreciate you sharing this blog article.Thanks Again. Will read on…
I’ve been surfing on-line more than 3 hours nowadays, but I by no means found any attention-grabbing article like yours. It is pretty value sufficient for me. In my view, if all webmasters and bloggers made just right content as you did, the internet can be a lot more helpful than ever before.
Thanks for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more clear from this post. I’m very glad to see such wonderful info being shared freely out there.
Hey just wanted to give you a quick heads up. The text in your article seem to be running off the screen in Chrome. I’m not sure if this is a format issue or something to do with web browser compatibility but I figured I’d post to let you know. The layout look great though! Hope you get the problem resolved soon. Thanks
You completed several good points there. I did a search on the subject and found the majority of folks will agree with your blog.
Great awesome things here. I am very happy to peer your post. Thank you so much and i’m taking a look ahead to contact you. Will you please drop me a e-mail?
Hey, thanks for the article.Really thank you! Fantastic.
I appreciate you sharing this blog post.Much thanks again.
Do you mind if I quote a couple of your posts as long as I provide credit and sources back to your blog? My blog is in the same niche as yours, and my users would benefit from some of the information you provide here. Please let me know if this ok with you. Thank you.
Enjoyed every bit of your article.Thanks Again. Will read on…
A round of applause for your blog post. Awesome.
Useful information. Lucky me I found your site accidentally, and I’m surprised why this accident did not came about in advance! I bookmarked it.|
When someone writes an paragraph he/she keeps the thought of a user in his/her mind that how a user can understand it. Therefore that’s why this post is great. Thanks!|
Looking forward to reading more. Great blog post.Thanks Again. Really Great.
Im grateful for the article.Thanks Again. Really Great.
wow, awesome article post.Thanks Again. Want more.
Wonderful information on your website
Thank you ever so for you blog.Thanks Again. Great.
I simply want to say I am beginner to blogging and actually liked you’re web page. More than likely I’m going to bookmark your site . You definitely come with fantastic posts. Thanks a bunch for sharing with us your website.
This is interesting!
Awesome blog post. Awesome.
I really like your writing style, good information, regards for putting up befkddcddgek
Inspiring story, where did you quote it from? fedcgackgckeaded
I like this weblog very much so much good info. It’s a poor sort of memory that only works backward. by Lewis Carroll. kkdgecegfgce
Informative Site Hello guys here are some links that contains information which you might find useful yourselves. It is Worth Checking out. bddfeaddfcfcddak
I really appreciate this post. I’ve been looking all over for this! Thank goodness I found it on Bing. You’ve made my day! Thanks again! eakdebdfdacf
whoah this weblog is wonderful i really like studying your posts. Keep up the great paintings! You already know, lots of individuals are searching around for this information, you can help them greatly. akdfebecdefdfgde
Pretty nice post. Ι jᥙѕt stumbled ulon үoսr blog аnd wwished tto
ѕay that I’ve trly enjoyed browsing үour blog posts.
In any case Ӏ will be subscribing tto your rss feed and I hope you
write agaіn very soon!
I simply want to mention I am newbie to blogging and site-building and honestly enjoyed you’re web blog. More than likely I’m likely to bookmark your blog post . You really come with amazing articles. Appreciate it for sharing your blog.
The next time I read a blog post from here I’m going to do so while eating some deep fried goodies.
I’ve never seen a scene which do that before.
I really liked reading this while eating a sandwich.
You shouldYou ought toYou need to take part inbe a part of a contest for one of the bestof the greatestof the finestof the highest qualityof the most useful blogssiteswebsites on the webon the interneton the netonline. I willI am going toI most certainly willI’m going to recommendhighly recommend this sitethis websitethis blogthis web site!
I love reading blogs like this while enjoying an ice cold beverage.
HowdyHi thereHey thereHiHelloHey! Someone in my MyspaceFacebook group shared this sitewebsite with us so I came to give it a looklook it overtake a lookcheck it out. I’m definitely enjoyingloving the information. I’m book-markingbookmarking and will be tweeting this to my followers! TerrificWonderfulGreatFantasticOutstandingExceptionalSuperbExcellent blog and wonderfulterrificbrilliantamazinggreatexcellentfantasticoutstandingsuperb style and designdesign and styledesign.
Hey are using WordPress for your blog platform? I’m new to the blog world but I’m trying to get started and set up my own. Do you require any html coding expertise to make your own blog? Any help would be really appreciated!
Good read, enjoyed it!
“Really appreciate you sharing this article.Really looking forward to read more. Fantastic.”
I genuinely enjoy reading on this website , it has great posts . “Something unpredictable but in the end it’s right, I hope you have the time of your life.” by Greenday.
Someone essentially help to make significantly posts I’d state. This is the first time I frequented your website page and to this point? I amazed with the analysis you made to create this particular submit incredible. Excellent activity!
Merely wanna remark that you have a very nice site, I the design and style it really stands out.
Keep up the excellent piece of work, I read few blog posts on this site and I think that your web site is really interesting and holds lots of superb information.
Considering Using Vitamins? Read This Article Now!
Your blog provided us with valuable information to work with. Each & every tips of your post are awesome. Thanks a lot for sharing.
I wanted to thank you for this excellent read!! I definitely loved every little bit of it. I have you bookmarked your site to check out the new stuff you post.
I just want to mention I am new to blogging and absolutely liked your web page. Almost certainly I’m want to bookmark your blog . You really have good articles. With thanks for sharing with us your website page.
(
I loveI really likeI likeEveryone loves it when peoplewhen individualswhen folkswhenever people come togetherget together and share opinionsthoughtsviewsideas. Great blogwebsitesite, keep it upcontinue the good workstick with it!
GreatExcellentGood blogweb sitesite you haveyou’ve gotyou have got here.. It’s hard to finddifficult to find qualityhigh qualitygood qualityhigh-qualityexcellent writing like yours these daysnowadays. I reallyI trulyI seriouslyI honestly appreciate people like youindividuals like you! Take care!!
very nice post, i certainly love this web site, keep on it bdagbeeddgdf
Someone essentially help to make significantly posts I might state. This is the first time I frequented your web page and so far? I surprised with the research you made to create this actual submit amazing. Magnificent activity! dgggfdbegbbdeegd
Nice article, i like it!
Hi, i think that i saw you visited my web site thus i came to return the favor.I am trying to find things to enhance my website!I suppose its ok to use some of your ideas!!
It’s actually a great and useful piece of info. I am glad that you shared this helpful information with us. Please keep us up to date like this. Thanks for sharing.
I have been checking out many of your stories and i can state pretty
With thanks! Valuable information!
Please let me know whether you’re looking for an author for your site. You have some great articles, and I think I’d be a good asset. Should you ever wish to take some of the load off, then I’d like to write some material to your site in exchange for a link back to mine. Please shoot me an email if interested. Thanks. {
Can I just say such a relief to get a person that actually knows what theyre talking about on the web. You actually know how to bring an issue to light and produce it critical. Lots more people really need to check out this and can see this side from the story. I cant believe youre no more popular since you undoubtedly contain the gift.
Needed to compose you a very little word to thank you yet again regarding the nice suggestions you’ve contributed here.
that’s why I bookmarked this page for get news feed with perfectly information in the next coming post ,
Thumb up for this post.