Preface: Do you think Chinese meaning of intelligence and clever have similar meanings? if you ask me. Perhaps I would say that clever refers to the sensitivity of the ears and eyes. Intelligence is about your brain. Maybe you have other explanations. When you watch a sci-fi movie, the AI core sends out drones to detect and arrest people. Maybe the plot is not described in detail. Comprehensive artificial intelligence machine learning should include vision and hearing. The obvious thing about drones is the vision capabilities of AI.
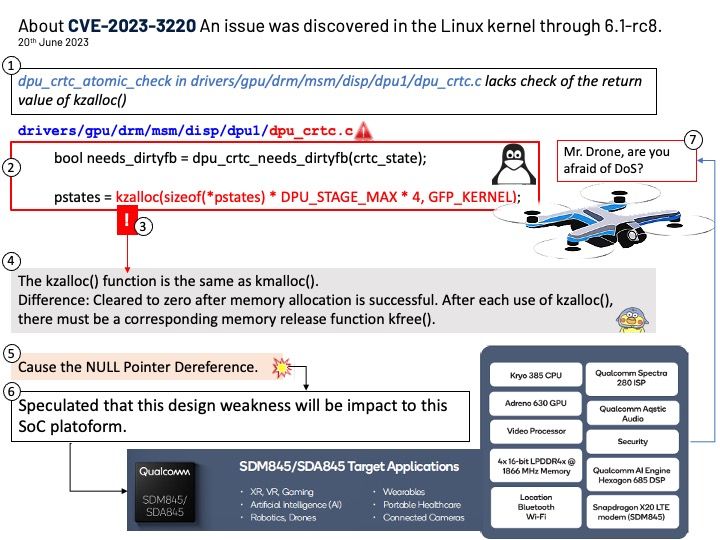
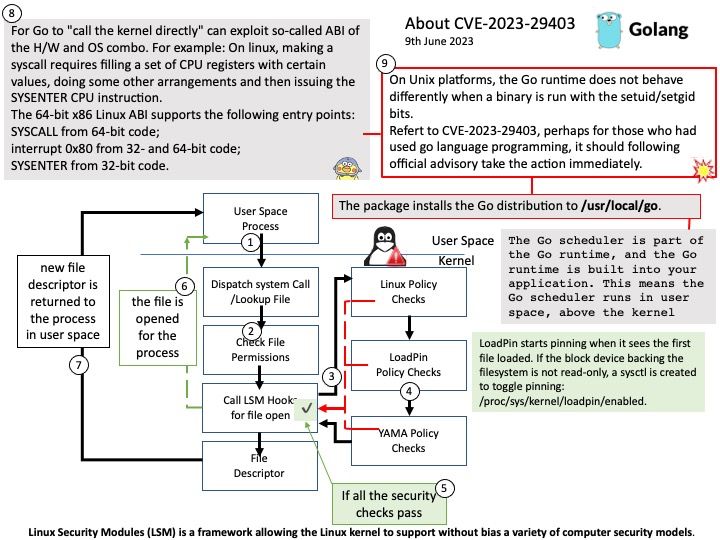
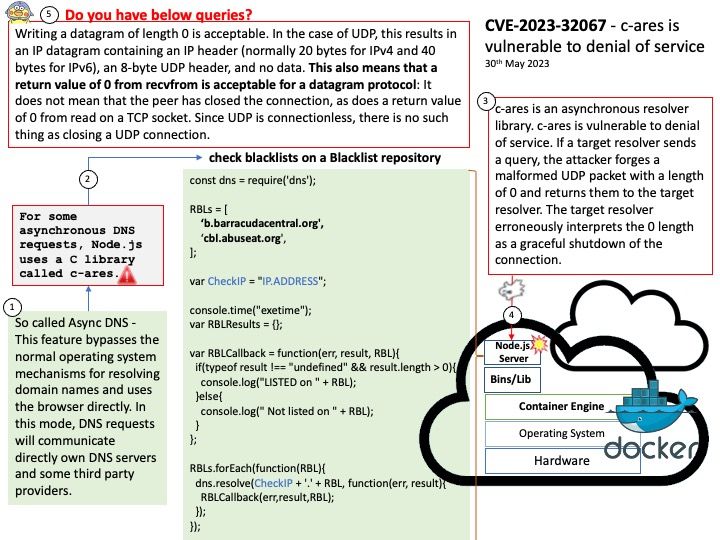
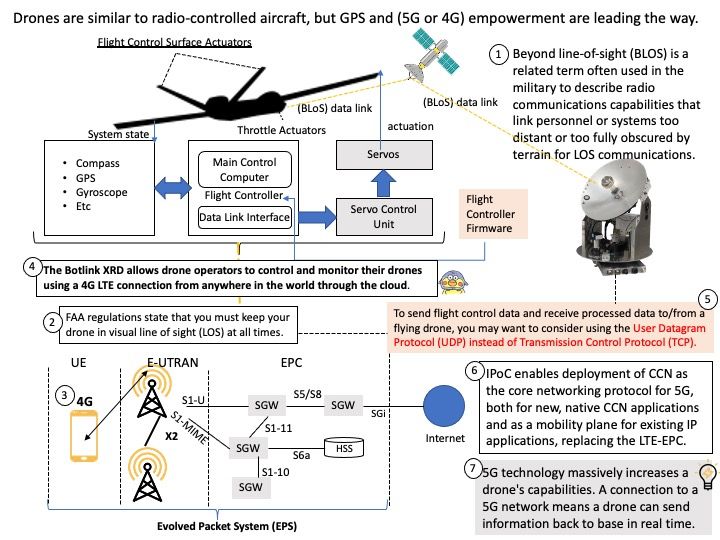
Background: It seems indisputable that 5G networks can enhance the performance capabilities of drones. Perhaps, it cannot be compared with the RF capabilities of the military type. If you’re interested in the subject, you’ll notice that many manufacturers are capable of designing drones and producing them. The reason is that chip manufacturers can provide flight control chips. Many open source firmwares can be easily downloaded on Github. Throttle actuators and flight control surface actuators are also available on the electronics market. The most commonly used languages in avionics software engineering are C, C++, Ada, and Python. In the main definition of network security, the TCP/IP protocol stack is one of the important trigger factors for network attacks. 5G or RF communication is exchanged in the communication gateway. Therefore, the IP protocol will be implemented after the 5G or RF signal exchange in the gateway. So cybersecurity will never leave this technology.
Ref: STM32 F4, G4, F7 and H7 are the popular microcontroller for drone. The flight controller unit (FCU) major component is the microcontroller.
The FCU consists of a processor and an Inertial Measurement Unit with a high precision accelerometer and gyroscope, necessary for stable flight.
Is the development of science and technology in opposition to the natural environment?
Humans can send probes to Mars and create and form artificial intelligence on Earth. Drone can do the real time monitroing even in extreme dangerous zone. Today’s medical technology enhances our healthcare. But when we look at the climate today, the Antarctic icebergs are melting, causing disaster and rising sea levels. So far, the situation has not improved!
See if artificial intelligence can provide solutions for humans soon?