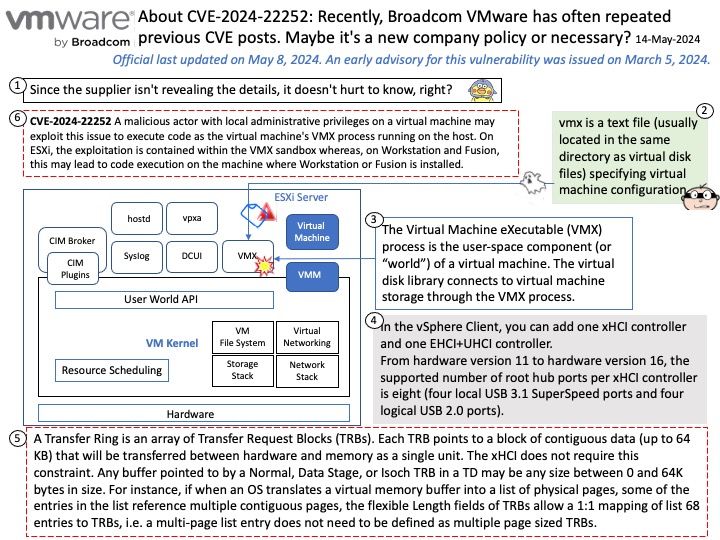
Preface: In computer security, arbitrary code execution (ACE) is an attacker’s ability to run any commands or code of the attacker’s choice on a target machine or in a target process. An arbitrary code execution vulnerability is a security flaw in software or hardware allowing arbitrary code execution.
Background: vCenter Server is the centralized management utility for VMware, and is used to manage virtual machines, multiple ESXi hosts, and all dependent components from a single centralized location. VMware vMotion and svMotion require the use of vCenter and ESXi hosts.
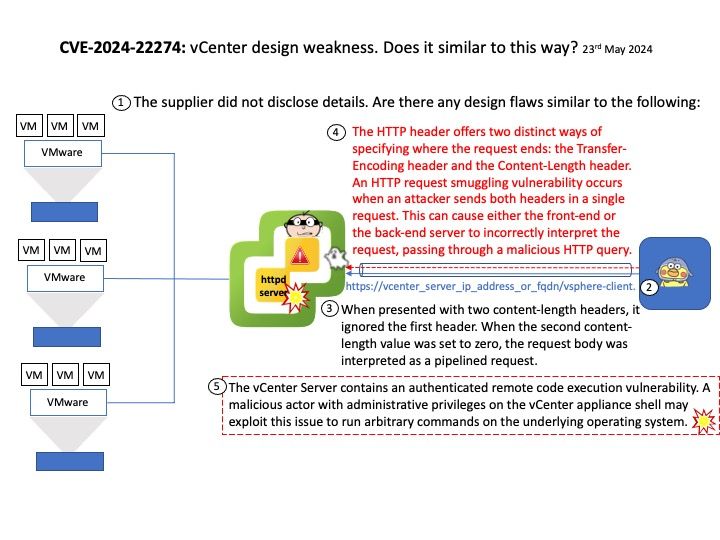
Vulnerability details: The vCenter Server contains an authenticated remote code execution vulnerability. A malicious actor with administrative privileges on the vCenter appliance shell may exploit this issue to run arbitrary commands on the underlying operating system.
The vendor did not disclose details. Are there any design flaws similar to the following:
Ref: The HTTP header offers two distinct ways of specifying where the request ends: the Transfer-Encoding header and the Content-Length header. An HTTP request smuggling vulnerability occurs when an attacker sends both headers in a single request. This can cause either the front-end or the back-end server to incorrectly interpret the request, passing through a malicious HTTP query.
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2024-22274