Preface: From logical point of view, if input only relies on a standalone source (sensor). The integrity of the result all relies on the total amount of variable factors. Perhaps sensor install on airplane is a IoT device. So it lure my interest.
Background: Traditionally the older (NG) 737 variants did not have fly-by-wire technology, and autopilot could be overridden and turned off simply by putting manual pressure on the yoke.
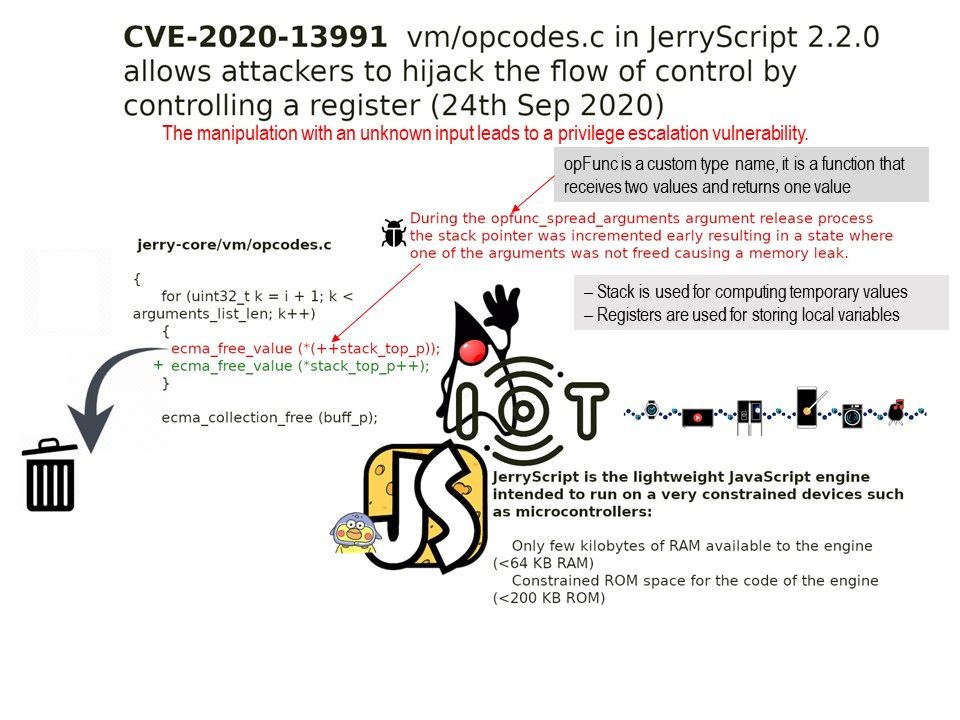
Software that talks to computer like airplanes equipment is often written in a programming language called C. The names of files written in C code usually have .c at the end. This assumes that the MCAS software is contained a file called mcas.c. But this time there was no cyber attack. This is a problem caused by human error.
For the 737 Max crashes (congressional report). Please refer to headline news – https://www.cbc.ca/news/world/us-congress-boeing-crash-report-1.5725876
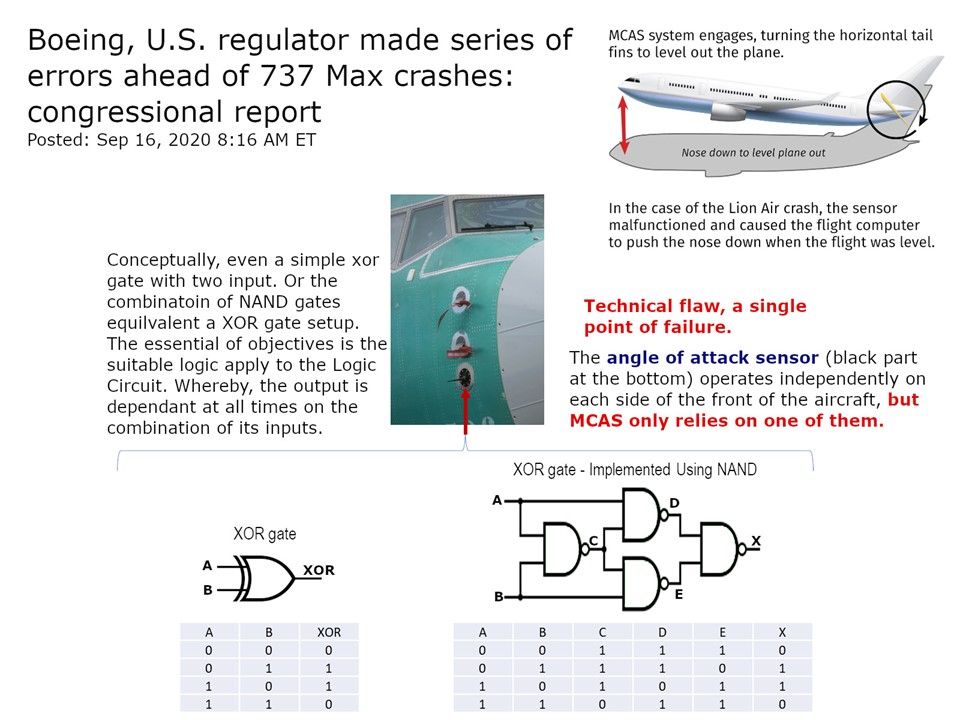
Cause of incident: In the case of the Lion Air crash, the sensor malfunctioned and caused the flight computer to push the nose down when the flight was level.
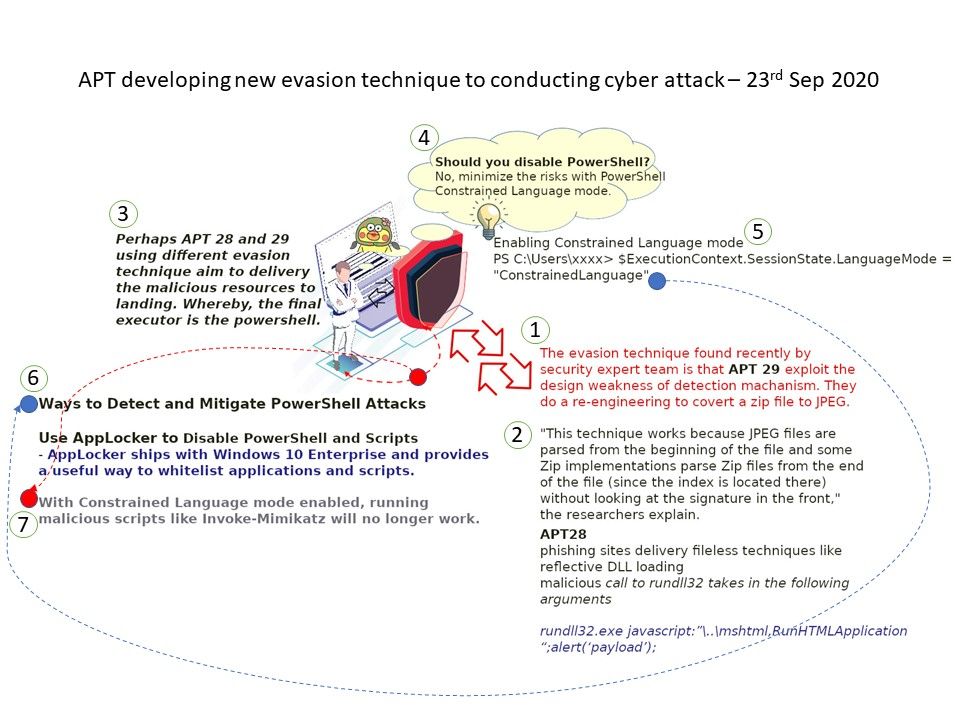
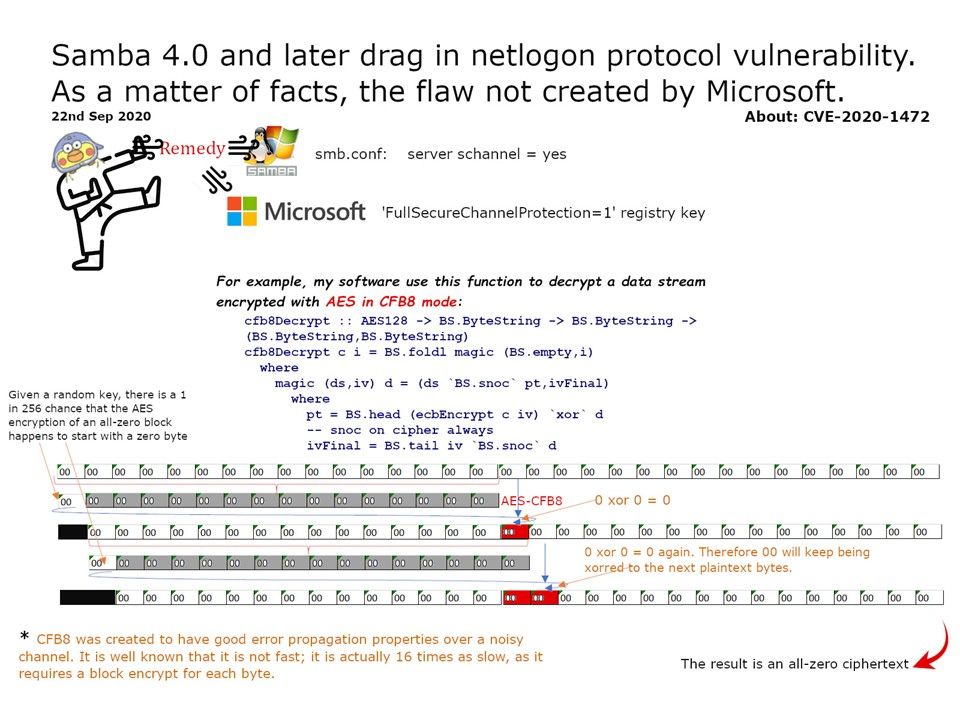
From technical point of view, the sensor is IoT device. There are facilities can avoid such disaster happen. Conceptually, even a simple xor gate with two input. Or the combination of NAND gates equivalent a XOR gate setup. The essential of objectives is the suitable logic apply to the Logic Circuit. Whereby, the output is dependant at all times on the combination of its inputs. It simple to say it is the logic design.