The cyber attack hot topic we focus retail payment system (Fastcash campaign) and adobe product vulnerabilities this week. However an additional cyber security alert announced by DHS. Yes, it is a APT cyber attack activities.
APT processes require a high degree of covertness over a long period of time. If you habit to observe the online real time cyber attack statis map. It looks that cyber attack vector in north korea not in high volume. As far as we know, an APT usually targets either private organizations, states or both for business or political motives. Do you experience below malware actvities?
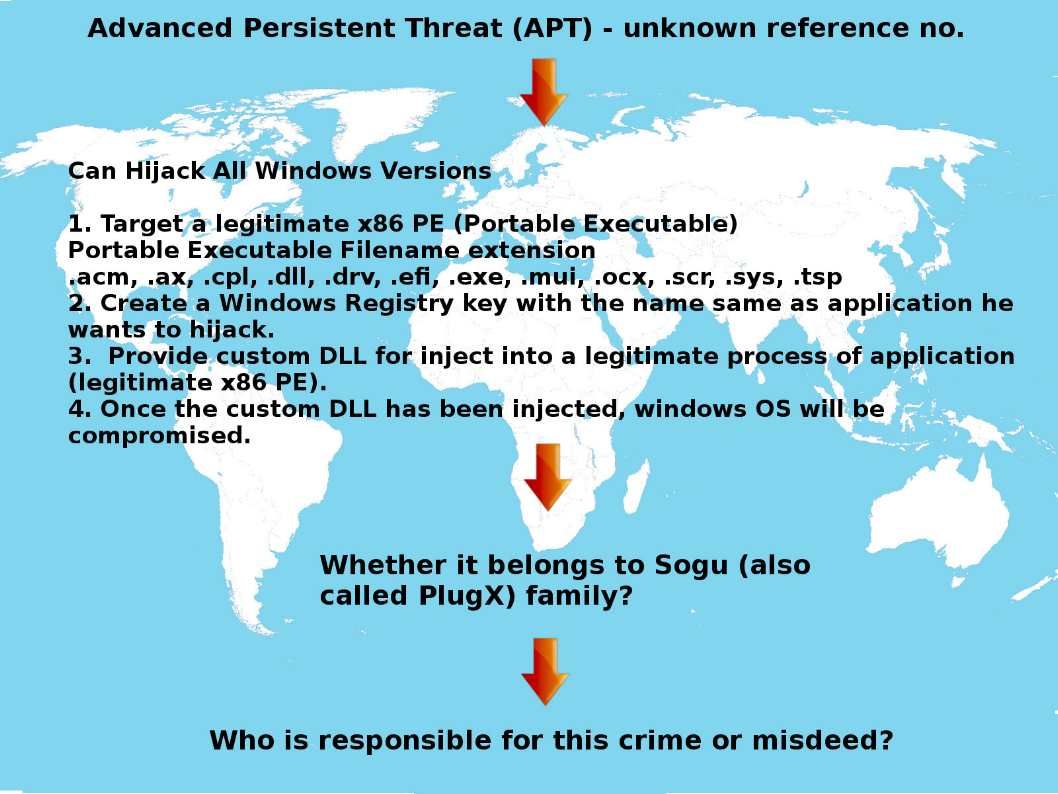
Can Hijack All Windows Versions
1. Target a legitimate x86 PE (Portable Executable)
2. Create a Windows Registry key with the name same as application he wants to hijack.
3. Provide custom DLL for inject into a legitimate process of application (legitimate x86 PE).
4. Once the custom DLL has been injected, windows OS will be compromised.
Whether we can blame Microsoft fifteen years old undocumented legitimate feature?
Should you have interest for APT 38. Below URL can provide the details.