Preface:
When executing a process by switching it between various CPU cores is that, when switching a process to a new CPU core, the “L1” cache of the new core has to be updated and the previous core’s “L1” cache might requires to be deleted etc. Whereby in a somewhat unnecessary cache activity that ultimately downgrade the performance. But the traditional mainframe vector processor and crossbar switch did not have above technical limitation.
What technologies have changed the world? The success of the PCR clusters was followed by the purchase of the Multiprogrammatic Capability Resource (MCR) cluster in July, 2002 from Linux NetworX. The PCR cluster debuted as the Top 500 Supercomputers list in November, 2002.
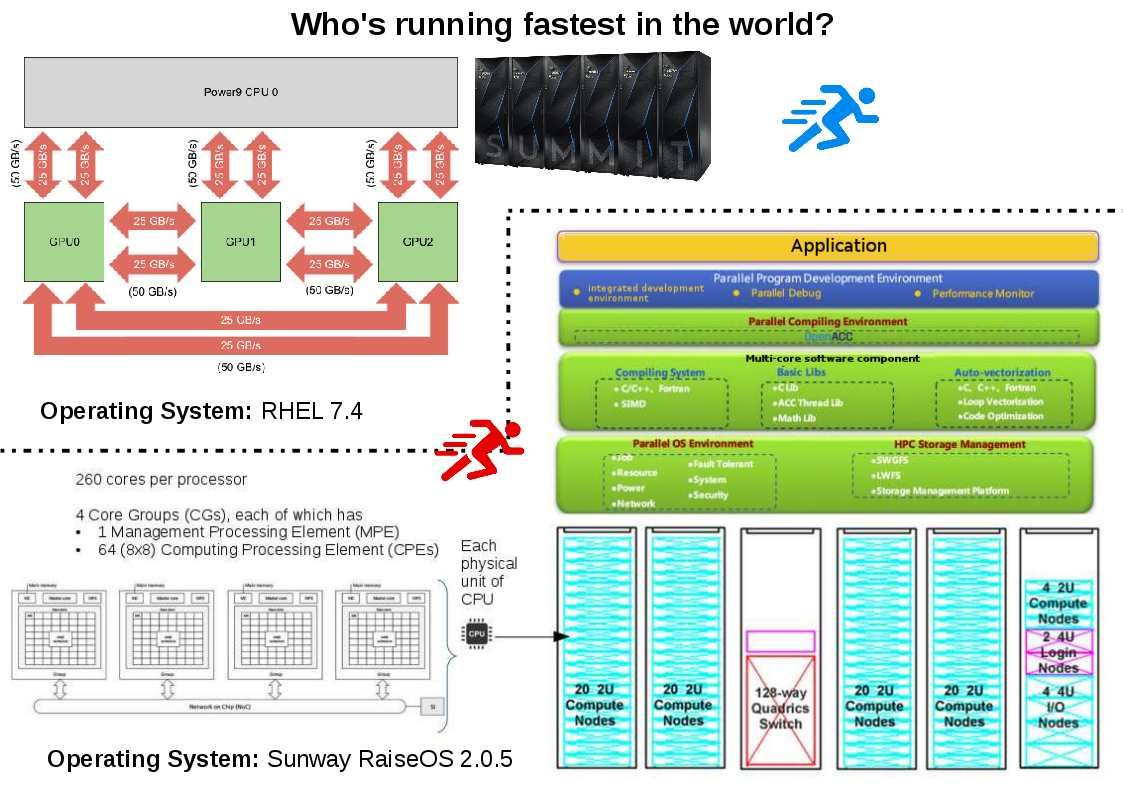
Who’s running fastest in the world?
1. Summit – IBM Power System AC922, IBM POWER9 22C 3.07GHz, NVIDIA Volta GV100, Dual-rail Mellanox EDR Infiniband , IBM DOE/SC/Oak Ridge National Laboratory
United States
Cores – 2,397,824, Rmax (TFlop/s)143,500.0
….
3. Sunway TaihuLight – Sunway MPP, Sunway SW26010 260C 1.45GHz, Sunway , NRCPC National Supercomputing Center in Wuxi China
Cores – 10,649,600 Rmax (TFlop/s) 93,014.6
Who knows who is the winner tomorrow?

Preface:
The samurai (or bushi) were the warriors of premodern Japan.Lone Wolf and Cub is a manga created by Japanese comics writer.Samurai respected justice.
Synopsis:
Justice is the legal or philosophical theory by which fairness is administered. It is the fundamental of human nature. But the concept of justice differs in every countries and culture.
Who is he?
Edward Snowden, an American contract employee at the National Security Agency, is the whistleblower behind significant revelations that surfaced in June 2013 about the US government’s top secret, extensive domestic surveillance programmes. Snowden flew to Hong Kong from Hawaii in May 2013, and supplied confidential US government documents to media outlets including the Guardian.
What’s the situation now?
He is on exile. His most recent interview in Moscow Russia on September 2018. (Refer below url)
https://www.youtube.com/watch?v=wimHE6SNddc
Why Edward Snowden should be pardoned?(Refer below url)
https://www.amnesty.org.uk/edward-snowden-nsa-whistleblower-pardon