Preface: c-ares 1.16.0: ares_destroy() with pending ares_getaddrinfo() leads to use-after-free
Background: Google added support for a feature known as asynchronous DNS to Google Chrome, which aims to speed up page loading times by resolving the IP address of a website before you click the link.
Recent versions of Google Chrome employ a feature called Async DNS. This feature bypasses the normal operating system mechanisms for resolving domain names and uses the browser directly. In this mode, DNS requests will uses SSL to communicate directly with Googles own DNS servers and some third party providers.
DNS features no only for domain lookup. Modern world technology can exploit DNS activities to do monitoring. (The word surveillance perhaps not suitable in this matter).
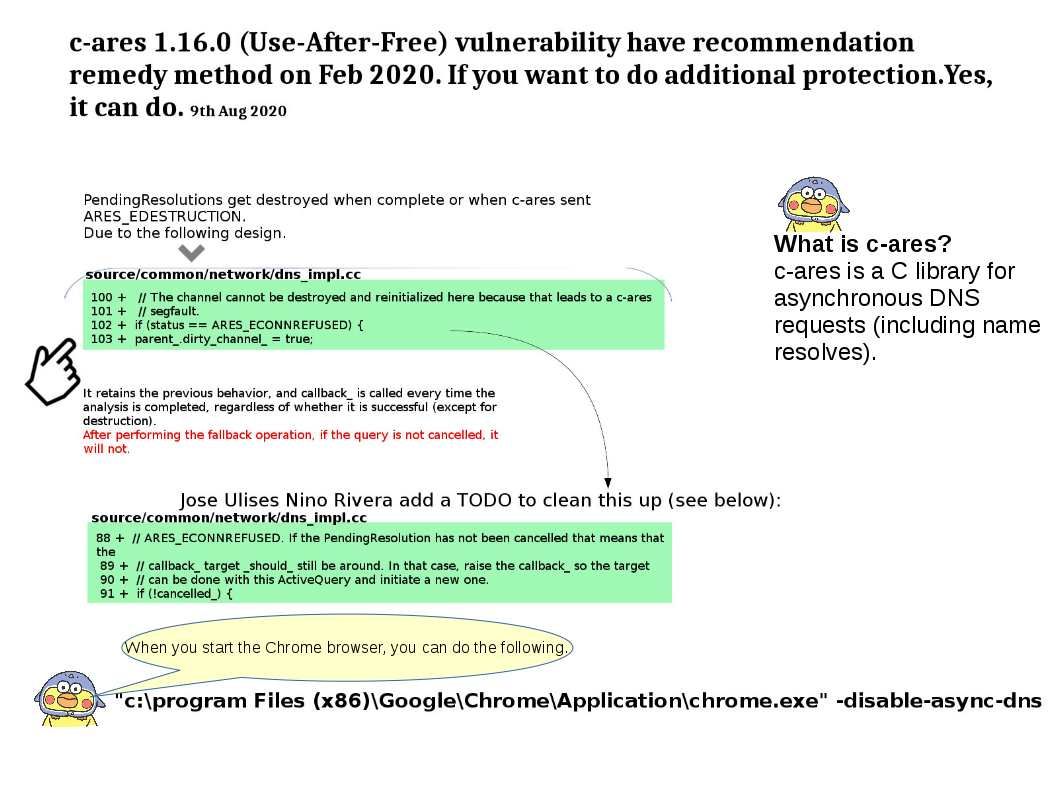
What is c-ares?
c-ares is a C library for asynchronous DNS requests (including name resolves).
Vulnerability details: PendingResolutions get destroyed when complete or when c-ares sent ARES_EDESTRUCTION. Refer to attached diagram, ARES_EDESTRUCTION only happened when the resolver was destroyed. Meanwhile, PendingResolutions can be destroyed, without the callback target being aware. This leads to potential use after free issues.
Additional: The recommendation remedy method posted on Feb 2020. If you want to do additional protection., please refer to information shown on bottom of the diagram.