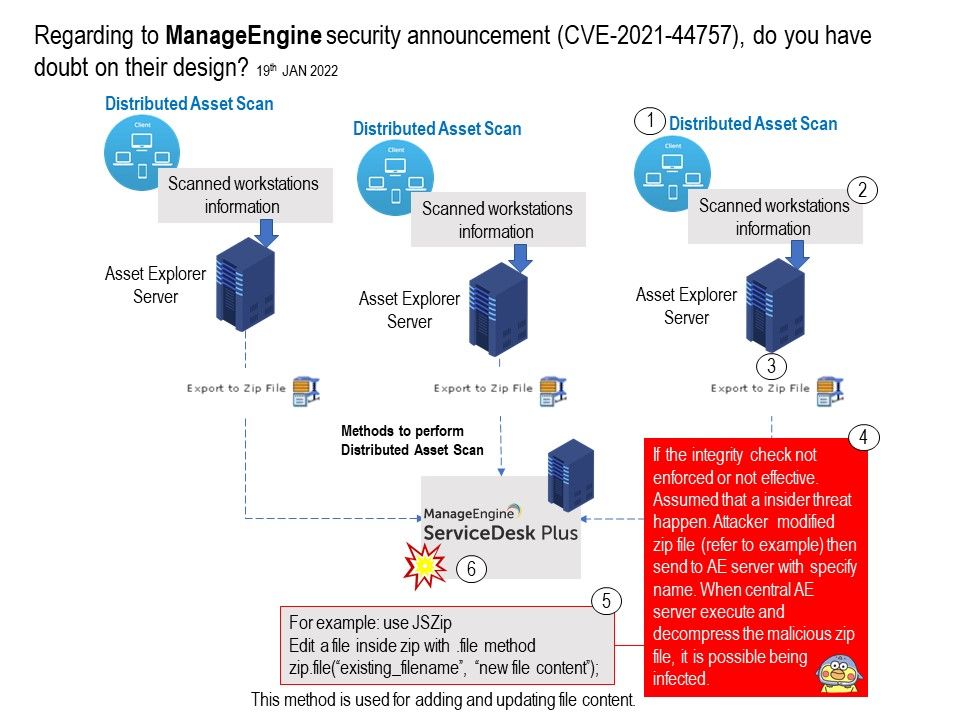
Preface: Asset scan is the key function to maintain the asset management integrity. If the company structure not operating standalone. In some circumstance, the system architect will formalize a distributed architecture. However, how to scan and collecting data is a important topic. Perhaps the file size is variable because of the data content. As a result, when the file transfer go to back-end system. it will using compression technology traditionally to resolve the network bandwidth consumption. For example: ZIP file. Furthermore, software developer aim to improve the process completion time.
Background (Asset Scan in Remote AE Server): The scanned information in the Remote AE Server can be updated periodically either manually or automatically in the Central AE Server.
You can install AssetExplorer as a Central Server by choosing the server type as Central AE Server on starting the application for the first time. The application is started as the Central AE Server.
As a result, Central AE server will tracks all your newly added assets, and have a record of all the assets in the organization.
About CVE-2021-44757: An authentication bypass vulnerability that can allow a remote user to perform unauthorized actions in the server. If exploited, this vulnerability may allow an attacker to read unauthorized data or write an arbitrary zip file on the server.
As usual, vendor not disclose the vulnerability in details. However, referring to existing system design. It relies on compression function assistance. Perhaps the earlier version of design do not enforce the data integrity check. And therefore it provide a channel to attacker create the trouble.
Official announcement: For details, please refer to link – https://pitstop.manageengine.com/portal/en/community/topic/a-critical-security-patch-released-in-desktop-central-and-desktop-central-msp-for-cve-2021-44757-17-1-2022