Preface: Did you check your JMS Security Authorization, fix your JMS application immediately.
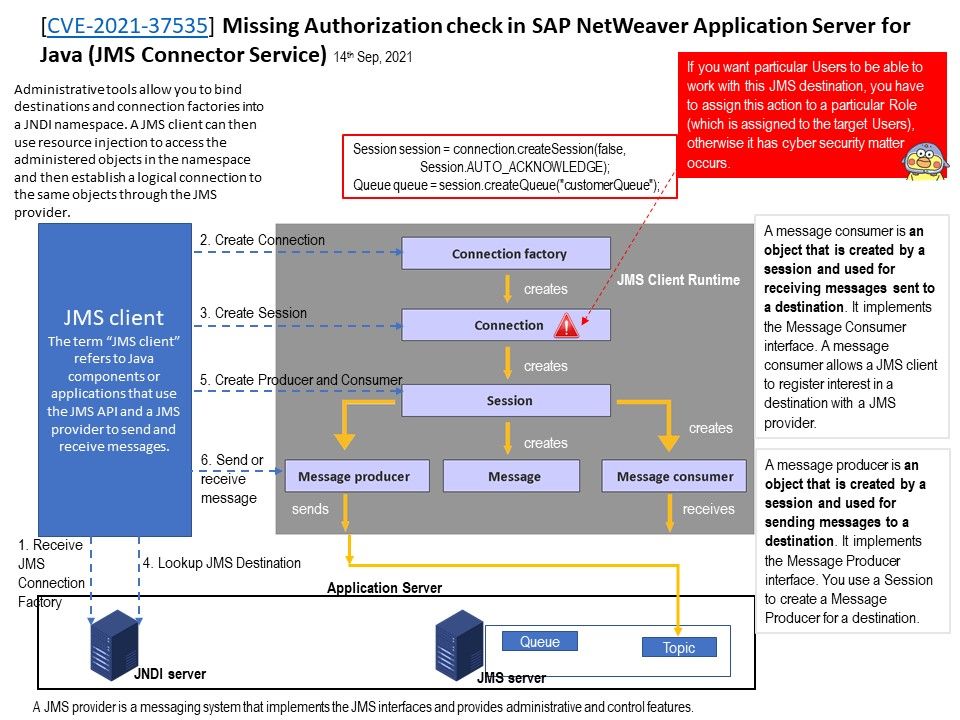
Background: The basic building blocks of a JMS application are:
- Administered objects: connection factories and destinations
- Connections
- Sessions
- Message producers
- Message consumers
- Messages
The JMS Connector Service is an enterprise messaging system that provides a way for business applications to exchange data
without needing to be directly connected to each other. The communication is obtained using messages. It allows different
message models like Point-to-Point Messaging or Publish-Subscribe scenarios.
Vulnerability details: Missing Authorization check in SAP NetWeaver Application Server for Java (JMS Connector Service)
The JMS Security Mechanism can helps you to protect your JMS application. By defining JMS actions for some API methods (such as createProducer(), createConsumer(), and so on) and assign permission to different user roles. In fact, it can minimize the risk.
In order to avoid unforseen issue happen in future. It is highly recommended to following vendor instruction to do the patching as early as possible.
Affected products – SAP NetWeaver Application Server Java (JMS Connector Service) , Versions – 7.11, 7.20, 7.30, 7.31, 7.40, 7.50
Official announcement – https://wiki.scn.sap.com/wiki/pages/viewpage.action?pageId=585106405