Preface: I do not care about this vulnerability since social media communication not secure by far. This is not the news.
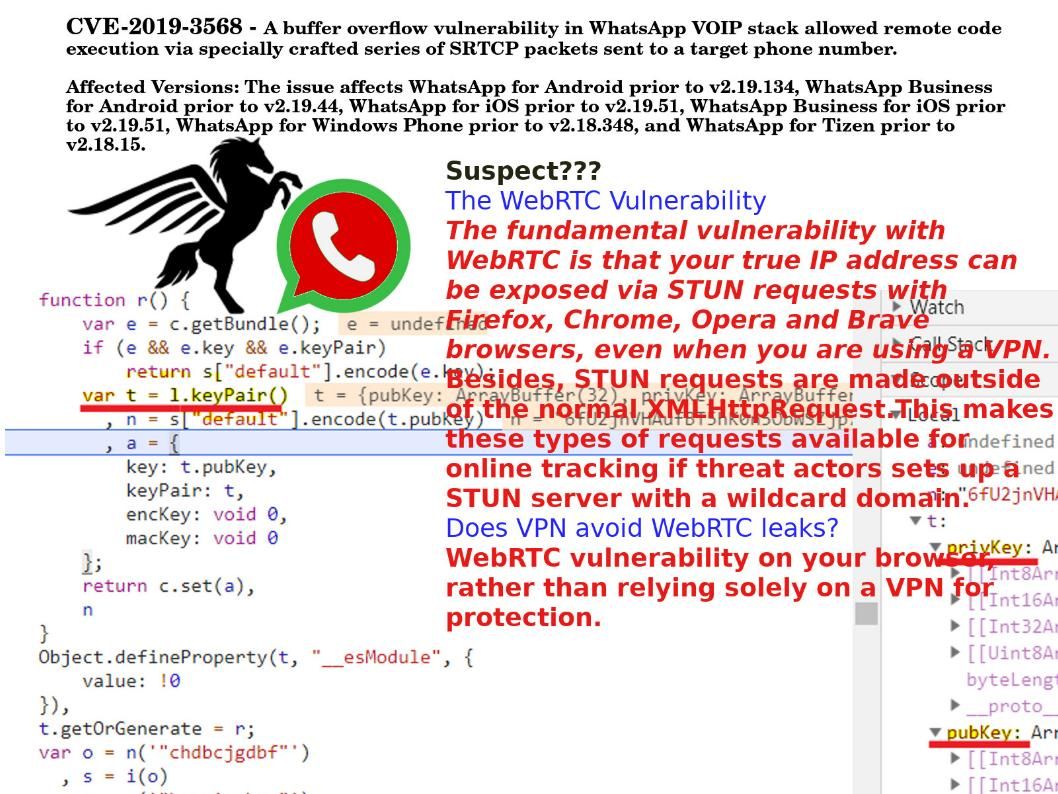
Headline news: Facebook Releases Security Advisory for WhatsApp. A remote attacker could exploit this vulnerability to take control of an affected device. For more details, please refer following url – https://www.facebook.com/security/advisories/cve-2019-3568
About vulnerability background Quote: Whatsapp, and messenger both of which uses STUN protocols to establish video call connectivities.
Doubt – The WebRTC Vulnerability
The fundamental vulnerability with WebRTC is that your true IP address can be exposed via STUN requests with Firefox, Chrome, Opera and Safari browsers, even when you are using a VPN.
Besides, STUN requests are made outside of the normal XMLHttpRequest.This makes these types of requests available for online tracking if threat actors sets up a STUN server with a wildcard domain.
Does VPN avoid WebRTC leaks?
WebRTC vulnerability on your browser, rather than relying solely on a VPN for protection.
Objective: As a matter of fact, the specify spyware is custom made for law enforcement. So, I believe that not easy to know the truth. Perhaps above hits will let you have more imaginations.