Preface: The registration of CVE records is largely out of sync with the time of the event. Perhaps the new release of CVE record by today, however it was happened few weeks or months ago. But with reference of these vulnerabilities records. Vulnerability scanner can precisely provide a result to you after scan.
Background: A block device, is, by definition, a device that stores or reads data in blocks. This means, always a certain amount of data is transmitted at every operation. How big that block is, highly depends on the protocol used. A network block device (NBD) is a standard protocol for Linux for exporting a block device over a network. NBDs are device nodes whose content is offered by a remote system. Generally, Linux users make use of NBDs to gain access to any storage device that does not reside in the local machine physically, but in a remote machine.
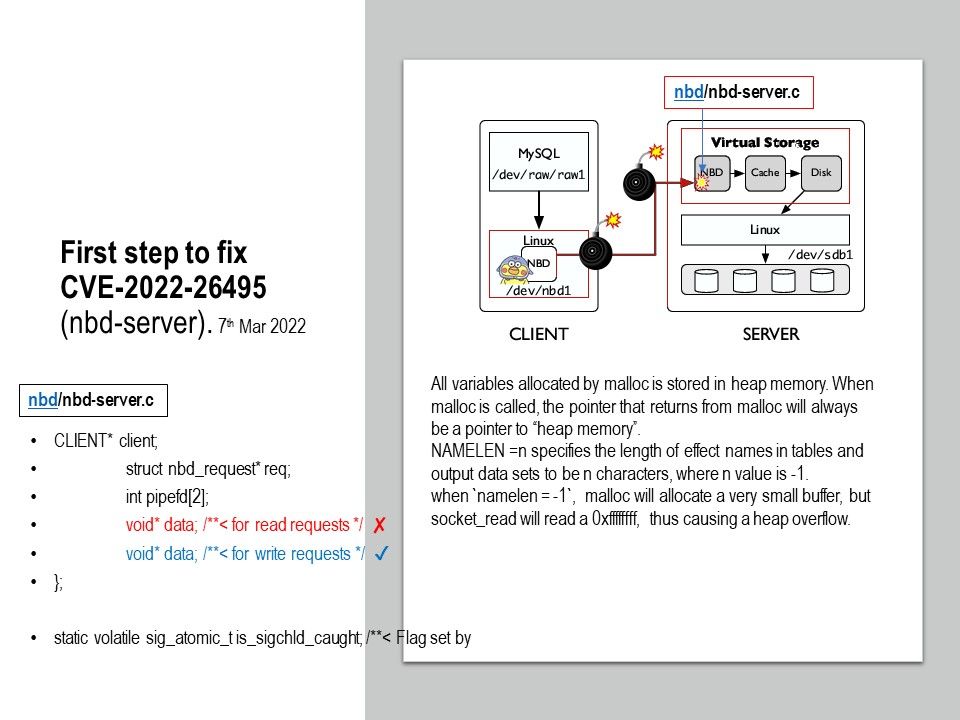
Vulnerability details: In nbd-server in nbd before 3.24, there is an integer overflow with a resultant heap-based buffer overflow. A value of 0xffffffff in the name length field will cause a zero-sized buffer to be allocated for the name, resulting in a write to a dangling pointer. This issue exists for the NBD_OPT_INFO, NBD_OPT_GO, and NBD_OPT_EXPORT_NAME messages.
All variables allocated by malloc is stored in heap memory. When malloc is called, the pointer that returns from malloc will always be a pointer to “heap memory”.
NAMELEN =n specifies the length of effect names in tables and output data sets to be n characters, where n value is -1.
when namelen = -1, malloc will allocate a very small buffer, but socket_read will read a 0xffffffff, thus causing a heap overflow.
Report security problem of nbd, please refer to the link – https://lists.debian.org/nbd/2022/01/msg00037.html