Preface: The registration of CVE records is largely out of sync with the time of the event. Perhaps the new release of CVE record by today, however it was happened few weeks or months ago. But with reference of these vulnerabilities records. Vulnerability scanner can precisely provide a result to you after scan.
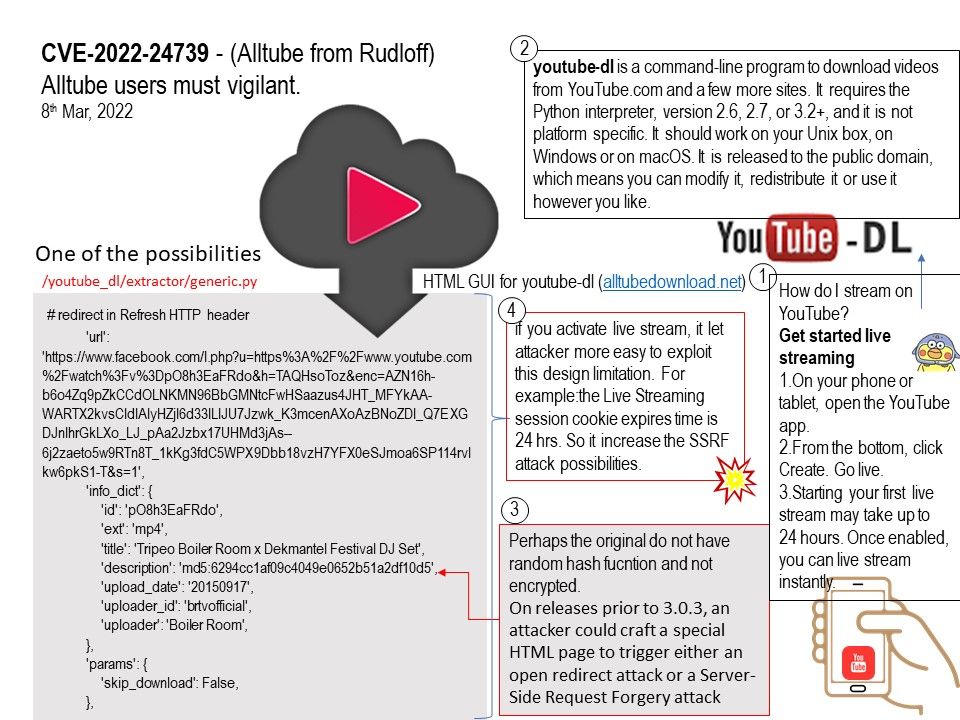
Background: youtube-dl is a command-line program to download videos from YouTube.com and a few more sites. It requires the Python interpreter, version 2.6, 2.7, or 3.2+, and it is not platform specific. It should work on your Unix box, on Windows or on macOS. It is released to the public domain, which means you can modify it, redistribute it or use it however you like.
Cope with Alltube, it make you easily download videos from YouTube, Dailymotion, Vimeo and other websites. Web GUI for youtube-dl. Contribute to Rudloff/alltube development by creating an account on GitHub. How do I download from Alltube? Clicking on the icon will open up the pop-up window. The extension will attempt to find the list of video qualities for the video in the watch page. The list of video will be displayed. To download the video, just click on the ‘Download’ button of the video quality.
Vulnerability details: Certain versions of Alltube from Rudloff contain the following vulnerability:
alltube is an html front end for youtube-dl. On releases prior to 3.0.3, an attacker could craft a special HTML page to trigger either an open redirect attack or a Server-Side Request Forgery attack (depending on how AllTube is configured). The impact is mitigated by the fact the SSRF attack is only possible when the `stream` option is enabled in the configuration. (This option is disabled by default.) 3.0.3 contains a fix for this vulnerability.
Remedy: Please refer to link – https://github.com/Rudloff/alltube/commit/3d092891044f2685ed66c73c870a021bee319c37