Preface: Apache Tomcat is one of the top technologies in Java developers’ tech stacks—and for good reason. According to the 2024 Java Developer Productivity Report, 36% of Java developers use Apache Tomcat as their application server.
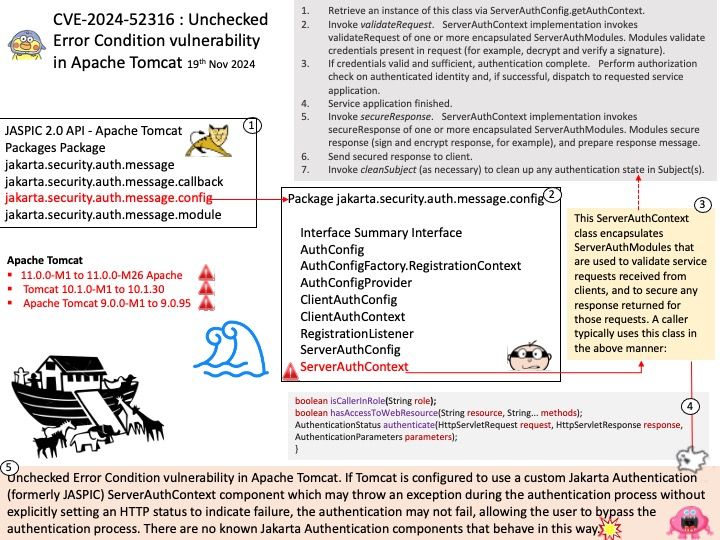
Background: Apache Tomcat (called “Tomcat” for short) is a free and open-source implementation of the Jakarta Servlet, Jakarta Expression Language, and WebSocket technologies. Jakarta is one of their project under which they have developed tomcat servlet container. Jakarta Authentication defines a general low-level SPI for authentication mechanisms, which are controllers that interact with a caller and a container’s environment to obtain the caller’s credentials, validate these, and pass an authenticated identity (such as name and groups) to the container.
Vulnerability details: Unchecked Error Condition vulnerability in Apache Tomcat. If Tomcat is configured to use a custom Jakarta Authentication (formerly JASPIC) ServerAuthContext component which may throw an exception during the authentication process without explicitly setting an HTTP status to indicate failure, the authentication may not fail, allowing the user to bypass the authentication process. There are no known Jakarta Authentication components that behave in this way.
Affected version : This issue affects Apache Tomcat: from 11.0.0-M1 through 11.0.0-M26, from 10.1.0-M1 through 10.1.30, from 9.0.0-M1 through 9.0.95. Users are recommended to upgrade to version 11.0.0, 10.1.31 or 9.0.96, which fix the issue.
Official announcement: Please refer to the link for details – https://nvd.nist.gov/vuln/detail/CVE-2024-52316