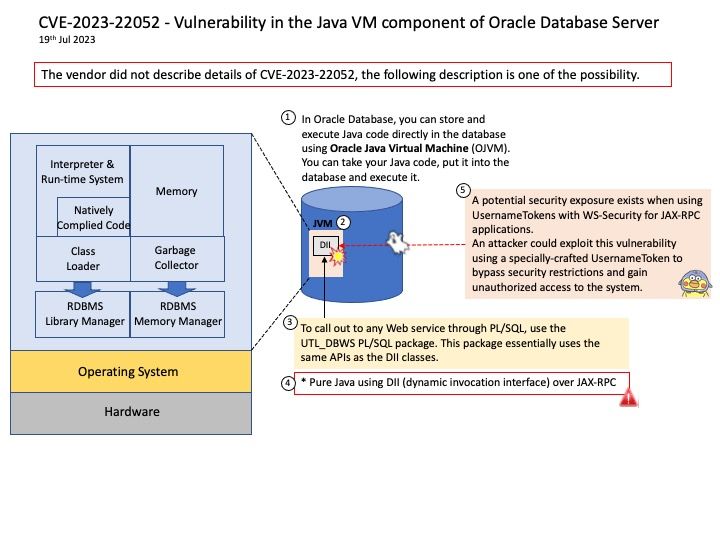
Preface: In Oracle Database, you can store and execute Java code directly in the database using Oracle Java Virtual Machine (OJVM). You can take your Java code, put it into the database and execute it.
Background: You can extend a relational database’s storage, indexing, and searching capabilities to include semistructured and nonstructured data (including Web Services) in addition to enabling federated data. By calling Web Services, the database can track, aggregate, refresh, and query dynamic data produced on-demand, such as stock prices, currency exchange rates, and weather information.
The Web services client code is written in SQL, PL/SQL, or Java to run inside Oracle Database, which then calls the external Web service. You can call a Web service from a Java client within the database, using one of the following methods:
- SQL and PL/SQL call specifications
- Pure Java
staticproxy class - Pure Java using dynamic invocation interface (DII) over JAX-RPC
For Web services call-outs using PL/SQL, use the UTL_DBWS PL/SQL package. This package essentially uses the same application programming interfaces (APIs) as the DII classes.
Vulnerability details: Vulnerability in the Java VM component of Oracle Database Server. Supported versions that are affected are 19.3-19.19 and 21.3-21.10. Difficult to exploit vulnerability allows low privileged attacker having Create Session, Create Procedure privilege with network access via multiple protocols to compromise Java VM. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of Java VM accessible data.
Supported Versions Affected: 19.3-19.19, 21.3-21.10
Official announcement: For details, please refer to the link – https://www.oracle.com/security-alerts/cpujul2023.html