Preface: On 2017, Facebook’s artificial intelligence robots shut down after they start talking to each other in their own language. Maybe no one remembers!
Background: If you are a data scientist. You know the details of the algorithms, which libraries to use, and perform diagnostics. For the machine learning setup, perhaps you will use a opensource software technology. One of the way is creating an ML app using Flask, a commonly used web framework in Python.
Furthermore, you have another choices. Streamlit is a framework that is used by different machine learning engineers and data scientists to build UIs and powerful machine learning apps from a trained model.
- How to install streamlit?
pip install streamlit - Build the streamlit app
- Create a new Python file named app.py.
- Add our pickled model into a created folder.
- Import required packages.
- Unplick the model.
- Building your prediction logic.
- You will use material UI for styles and icons for your app
- Adding an image.
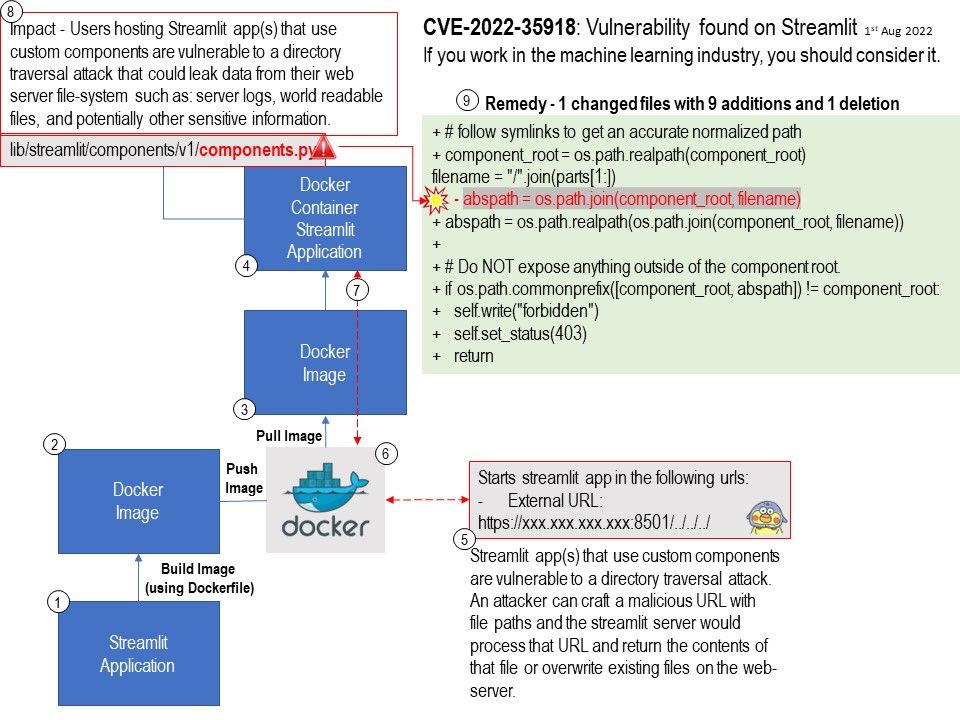
Vulnerability details: Users hosting Streamlit app(s) that use custom components are vulnerable to a directory traversal attack that could leak data from their web server file-system such as: server logs, world readable files, and potentially other sensitive information.
An attacker can craft a malicious URL with file paths and the streamlit server would process that URL and return the contents of that file.
Solution: Vendor strongly recommend users upgrade to v1.11.1 as soon as possible. Please refer to the link for details – https://github.com/streamlit/streamlit/security/advisories/GHSA-v4hr-4jpx-56gc